Third-Party Risk Assessment: Essential Steps for 2026
Imagine waking up to find that a vendor you trusted just triggered a breach that exposed your customer data, disrupted operations, and put your leadership team under regulatory scrutiny. As you expand your use of cloud services, outsourced platforms, and partner ecosystems, your organization’s risk no longer stops at your firewall.

Third parties now represent potential fault lines in your compliance, security, and operational continuity strategies. Recent research shows that at least 35.5% of all data breaches in 2024 were linked to third-party compromises, up significantly from previous years. For compliance officers, risk managers, CTOs, and CEOs, mastering third-party risk assessment is a foundational requirement for resilient, audit-ready operations.
In this blog, we will walk through the essential steps you need to build a strong third-party risk assessment process and stay ahead of emerging threats.
Key Takeaways
- Third-party risk assessment helps organizations identify and control vendor-related regulatory, operational, and data risks.
- A strong program follows a clear lifecycle: inventory, classification, assessment, scoring, remediation, and continuous monitoring.
- Risk-based classification ensures oversight focuses on vendors with the highest business and regulatory impact.
- Audit-ready evidence and tracked remediation are critical for successful US exams.
- Centralized execution makes third-party risk assessment scalable, consistent, and defensible.
Did you know? According to Verizon’s 2025 Data Breach Investigations Report, 30% of all data breaches in the year ending October 31, 2024, involved third‑party suppliers, vendors, or hosting partners, up from just 15% the year before, showing how rapidly vendor ecosystem vulnerabilities are being exploited.
What Is Third-Party Risk Assessment?
Third-party risk assessment is the structured process you use to evaluate the risks introduced by external vendors before and during engagement. For organizations operating under state-based regulatory oversight, it ensures vendors do not weaken your compliance posture, operational resilience, or policyholder trust.
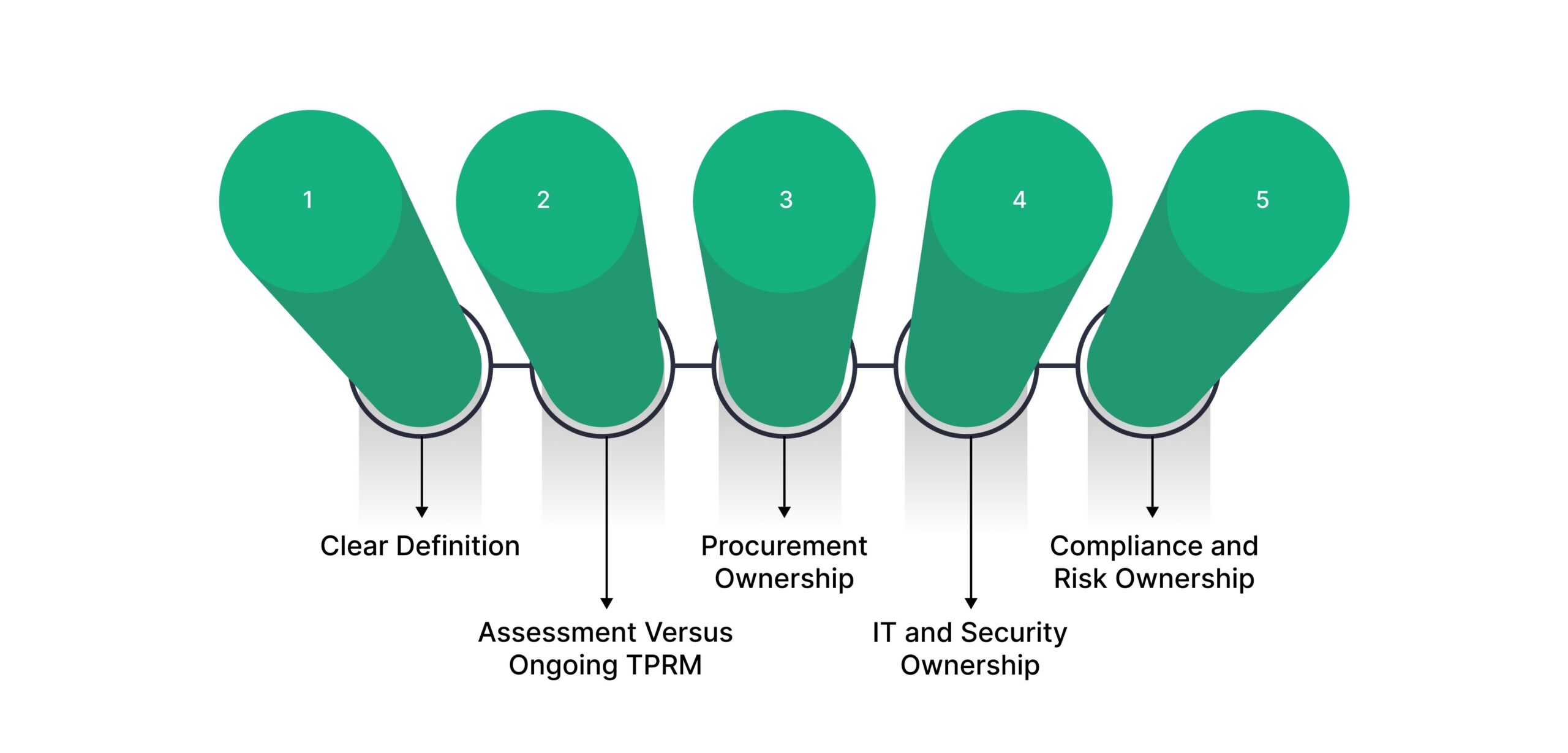
Below is a practical breakdown to clarify ownership, scope, and execution.
- Clear Definition: Third-party risk assessment evaluates how a vendor’s controls, practices, and dependencies may impact your regulatory obligations, data protection responsibilities, and operational continuity.
- Assessment Versus Ongoing TPRM: A third-party risk assessment is a point-in-time evaluation, while ongoing third-party risk management (TPRM) continuously monitors vendor risk throughout the lifecycle, including renewals, incidents, and regulatory exams.
- Procurement Ownership: Procurement initiates assessments during vendor onboarding, ensuring risk reviews align with sourcing decisions, contract terms, and vendor criticality before agreements are finalized.
- IT and Security Ownership: IT and security teams assess system access, data handling practices, integrations, and cybersecurity controls, focusing on risks that could affect policyholder data or core platforms.
- Compliance and Risk Ownership: Compliance and enterprise risk teams define assessment criteria, validate evidence, maintain audit trails, and ensure results support state examinations, internal audits, and board reporting.
Once you understand what third-party risk assessment entails, the next step is identifying the specific risk categories that must be evaluated to protect regulatory, operational, and data integrity.
Core Types Of Third-Party Risk You Must Evaluate
As a compliance leader, you face a complex risk scene shaped by outsourcing, digital ecosystems, and state-level regulatory expectations. Evaluating third-party risk requires more than surface checks.
Below are the core risk types you must evaluate as part of a defensible third-party risk assessment program.
- Cybersecurity and Data Privacy Risk: This risk centers on how vendors protect sensitive data, including policyholder information, claims data, and underwriting records. You must assess access controls, breach response readiness, and data handling practices to ensure vendor weaknesses do not trigger reportable incidents or regulatory scrutiny.
- Compliance and Regulatory Risk: Vendors may expose you to noncompliance with US regulations such as HIPAA, SOX, or state department requirements. This risk emerges when third parties lack documented controls, audit evidence, or governance practices that align with your regulatory obligations.
- Operational and Business Continuity Risk: Operational risk evaluates whether a vendor can consistently support critical functions during disruptions. You assess dependency levels, disaster recovery capabilities, and service resiliency to prevent claims delays, system outages, or examination findings tied to vendor failures.
- Financial and Reputational Risk: Financial instability or unethical practices at a vendor can quickly become your risk. You must consider solvency indicators, litigation exposure, and public incidents that could damage policyholder trust or raise concerns during market conduct exams.
- Fourth-Party Risk Exposure: Fourth-party risk arises when your vendors rely on subcontractors you do not directly control. Weak controls at these downstream providers can create contagion effects, making it essential to evaluate how vendors oversee and govern their own third-party relationships.
VComply Risk Ops helps you centralize all vendor risk data, score vendors objectively, and track remediation progress. By linking risk types to actionable dashboards, your team can quickly identify high-impact risks, prioritize mitigation, and maintain audit-ready oversight across your third-party ecosystem.
Now, let’s break it down into actionable steps that teams can follow consistently throughout the vendor lifecycle.
Essential Steps for Third-Party Risk Assessment
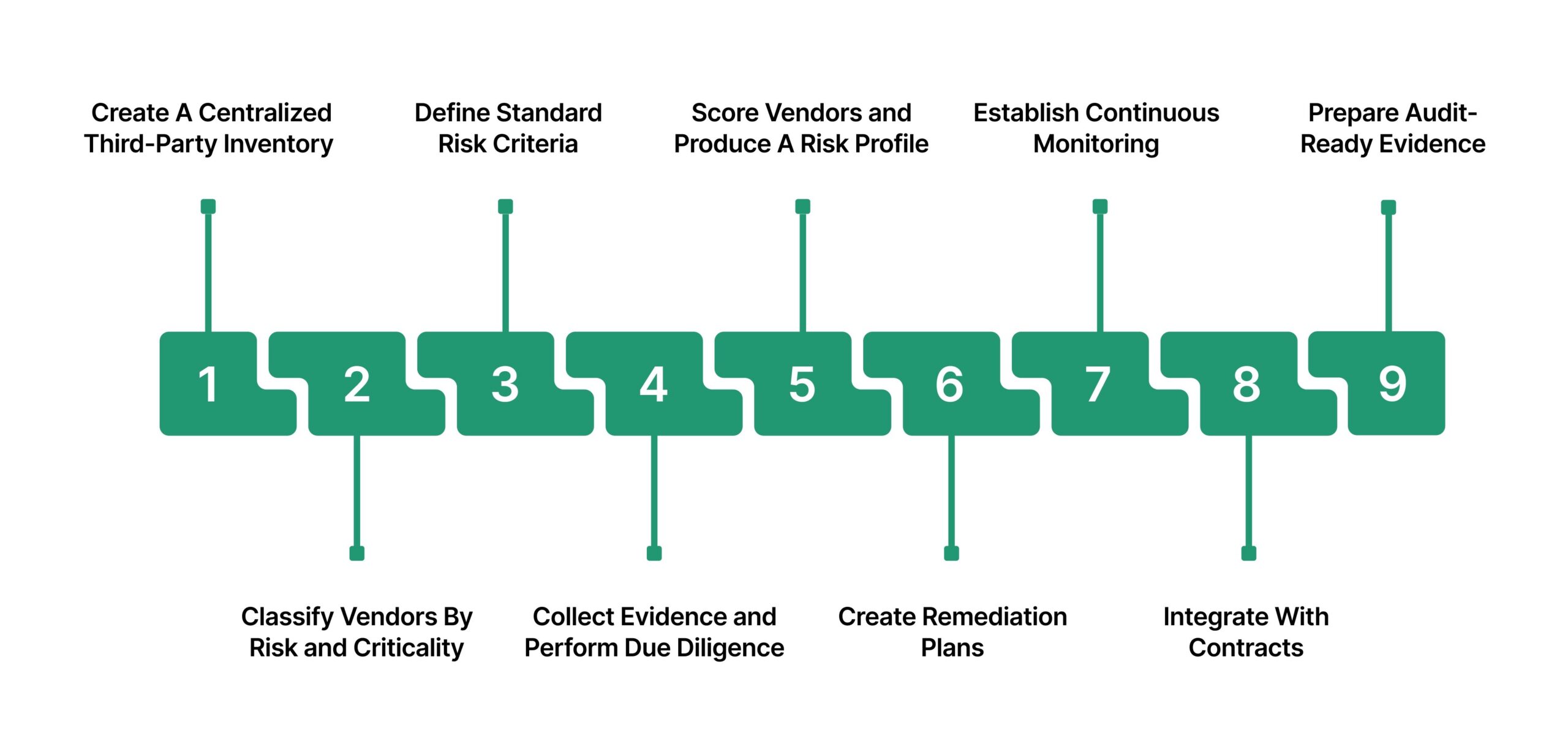
Managing third-party risk effectively requires more than policy statements or ad hoc reviews. You need a clear sequence of actions that teams can follow consistently, produce defensible evidence, and scale as vendor relationships grow.
Below are the practical, ordered actions you should follow to run assessments and maintain an effective TPRM program.
Step 1: Create A Centralized Third-Party Inventory
A centralized third-party inventory is the foundation of any defensible risk assessment program. Without a complete and accurate view of your vendor ecosystem, risk evaluations become fragmented and difficult to justify during state examinations.
Below are the key elements you should capture to build an audit-ready third-party inventory.
- Vendor Identification Details: Capture the legal vendor name, service provided, and business function supported. This establishes clarity on how each third party contributes to underwriting, claims, policy administration, or customer operations.
- Risk Criticality Classification: Record the vendor’s criticality level based on its role in core processes. Clear classification supports risk-based oversight and examination defensibility.
- Data Access and Sensitivity: Document the type of data accessed, such as policyholder personal information or claims data. This helps you align assessment depth with data exposure risk.
- Contract and Engagement Information: Maintain contract identifiers, effective dates, renewal timelines, and termination clauses. Contract visibility supports timely reassessments and regulatory evidence requests.
- Primary and Escalation Contacts: Identify vendor contacts responsible for risk, security, and compliance matters. Clear ownership accelerates remediation and communication during incidents.
- Geographic and Jurisdictional Coverage: Track vendor operating regions and data processing locations. This is essential for assessing jurisdictional risk and cross-border exposure.
Recommended Metadata Schema (Sample CSV Header): Vendor_Name, Service_Provided, Business_Function, Criticality_Level, Data_Types_Accessed, Contract_ID, Contract_End_Date, Primary_Contact, Operating_Region, Assessment_Status
Also Read: A Complete Guide on Third-Party Risk Management
Establishing this centralized inventory creates the execution layer needed to scale third-party risk assessments consistently, support audit inquiries, and maintain ongoing visibility across your vendor environment.
Step 2: Classify Vendors By Risk and Criticality
Once your vendor inventory is established, classification determines how much oversight each third party requires. Without consistent classification, teams apply uneven scrutiny, creating gaps that surface during state exams.
Below are the core criteria and a practical tiering model you can apply consistently.
- Access Level To Systems and Data: Evaluate the extent of system access, including whether the vendor connects to core platforms or processes sensitive policyholder or claims data.
- Data Sensitivity and Volume: Assess the type and volume of information handled, such as personally identifiable information, protected health information, or financial records tied to policy administration.
- Business Criticality: Determine how essential the vendor is to day-to-day operations. Vendors supporting claims processing or policy servicing typically require higher oversight.
- Regulatory Exposure: Consider whether vendor activities directly impact compliance with state regulations or federal requirements, increasing examination and enforcement risk.
Sample Risk Tiering Model
| Risk Tier | Assignment Rule |
| High Risk | Vendor has direct access to sensitive policyholder data, supports core functions, or creates material regulatory exposure. |
| Medium Risk | Vendor supports important business processes with limited data access and moderate operational dependency. |
| Low Risk | Vendor provides non-critical services with minimal data access and no direct regulatory impact. |
Consistent classification enables you to scale assessments efficiently, apply proportionate controls, and clearly justify oversight decisions during audits and regulatory reviews.
Step 3: Define Standard Risk Criteria and Assessment Scope
After classification, you need consistent criteria to evaluate vendors in a way regulators and executives can trust. Without defined risk factors and scoring logic, assessments become subjective and difficult to defend.
Below are the core elements to define before you begin assessments.
- Security Controls and Data Protection (Suggested Weight: 35%): Evaluate how the vendor safeguards systems and data, including access controls, encryption practices, incident response readiness, and vulnerability management. This factor typically carries the highest weight due to policyholder data exposure and breach reporting obligations.
- Financial Health and Business Stability (Suggested Weight: 20%): Assess financial viability, ownership structure, and long-term sustainability. Financial instability increases the risk of service disruption and operational impact during critical processes.
- Service Level and SLA Criticality (Suggested Weight: 20%): Measure the importance of the services provided and the strength of contractual service commitments. Vendors supporting time-sensitive functions, such as claims processing, require tighter performance oversight.
- Compliance Alignment and Governance (Suggested Weight: 15%): Review whether the vendor maintains documented policies, internal controls, and audit evidence aligned with your compliance obligations and examination expectations.
- Dependency and Concentration Risk (Suggested Weight: 10%): Consider reliance on the vendor and the availability of alternatives. High dependency increases operational and regulatory exposure if the relationship fails.
To ensure consistency and exam readiness, use standardized assessment templates mapped to recognized frameworks such as SOC 2, ISO 27001, and HIPAA.
Framework-mapped templates allow you to collect relevant evidence once and reuse it across assessments, audits, and regulatory reviews, strengthening defensibility while reducing assessment fatigue.
Step 4: Collect Evidence and Perform Due Diligence
Risk scoring is only as strong as the evidence behind it. A structured evidence collection process ensures findings are verifiable, traceable, and consistently applied across vendors.
Below are the key due diligence methods and a practical questionnaire structure to support defensible assessments.
- Structured Risk Questionnaires: Use standardized questionnaires aligned to your defined risk criteria. Questionnaires should focus on how controls operate in practice, not just whether policies exist.
- Security Attestations and Certifications: Collect formal attestations and certifications, such as SOC 2 reports or ISO 27001 certificates, to validate control maturity and independent oversight.
- Penetration Test and Vulnerability Reports: Review recent testing results to understand the practical security posture. Pay attention to remediation status, not just test completion.
- Contractual and Legal Review: Examine contracts for data protection obligations, audit rights, breach notification timelines, and subcontractor controls. Contracts often reveal risk gaps missed by questionnaires.
Sample Questionnaire Structure
- Organizational and Governance Controls: Mandatory evidence: security policies, governance charters, risk ownership documentation.
- Data Protection and Privacy Controls: Mandatory evidence: data flow diagrams, encryption standards, and access management procedures.
- Security Operations and Incident Response: Mandatory evidence: incident response plan, breach notification procedures, and recent incident summaries.
- Business Continuity and Resilience: Mandatory evidence: disaster recovery plans, testing results, recovery time objectives.
- Third-Party and Subcontractor Oversight: Mandatory evidence: subcontractor risk assessments, contractual flow-down clauses.
With VComply Compliance Ops, you can automate evidence collection, store documentation in a centralized repository, and map assessments to frameworks like SOC 2, ISO 27001, and HIPAA. This ensures your compliance reviews are consistent, defensible, and easily auditable without the burden of manual tracking.
Step 5: Score Vendors and Produce A Risk Profile
Once evidence is collected, scoring converts qualitative findings into decisions that leadership and regulators can understand. A structured scoring approach ensures vendor risks are prioritized objectively and tracked over time.
Below is a practical approach to scoring vendors and producing clear risk profiles.
- Control Effectiveness and Impact Scoring Model: Score each risk domain based on control effectiveness and potential business impact. Effectiveness measures how well controls operate, while impact reflects consequences to policyholders, operations, and compliance obligations.
- Score Normalization Across Assessments: Normalize scores so results remain comparable across vendors and assessment cycles. Normalization prevents scoring inflation and ensures consistent interpretation during portfolio-level reviews.
- Risk Thresholds and Escalation Rules: Define thresholds that trigger escalation, remediation, or leadership review. Clear thresholds demonstrate structured decision-making and reduce ambiguity during regulatory examinations.
- Residual Risk and Business Acceptance: After remediation actions are defined, reassess to determine residual risk. Document formal business acceptance for residual risk that remains within approved tolerance, creating a clear audit trail for examiners and governance committees.
Sample Scoring Matrix:
| Control Effectiveness | Low Impact | Medium Impact | High Impact |
| Strong Controls | Low Risk | Medium Risk | Medium Risk |
| Moderate Controls | Medium Risk | Medium Risk | High Risk |
| Weak Controls | Medium Risk | High Risk | High Risk |
A well-defined scoring and profiling process transforms assessment data into actionable insight, enabling disciplined oversight and transparent risk governance across your third-party ecosystem.
Step 6: Create Remediation Plans and Assign Ownership
Identifying risk without remediation creates regulatory exposure rather than control. Clear ownership and documented follow-through demonstrate that third-party risks are actively managed, not merely recorded.
Below is a practical approach to remediation planning and execution.
- Standardized Remediation Ticket Format: Each remediation item should include the risk description, affected control, required corrective action, assigned owner, target completion date, and evidence requirements. Standardization ensures clarity and consistent tracking across vendors.
- Defined SLA Targets Based On Risk Severity: Set remediation timelines aligned to risk level. High-risk issues require accelerated resolution, while lower-risk gaps may follow standard review cycles. Documented SLAs support defensible prioritization.
- Clear Escalation and Oversight Path: Establish escalation rules for overdue or unresolved issues. Escalation to compliance leadership or risk committees reinforces accountability and governance.
- Verification and Evidence Validation: Require objective evidence to confirm remediation, such as updated policies, test results, or control screenshots. Verification prevents premature closure and strengthens audit readiness.
Remediation Workflow Overview
Create Remediation Ticket → Assign Owner → Track Progress Against SLA → Collect and Validate Evidence → Approve Closure.
A disciplined remediation process transforms assessment findings into measurable risk reduction, providing regulators and leadership with confidence that third-party risks are addressed systematically.
Step 7: Establish Continuous Monitoring and Triggered Reviews
Third-party risk does not remain static between annual assessments. Changes in a vendor’s environment can introduce new exposure overnight, creating gaps that surface during incidents or regulatory exams.
Below are the key monitoring signals and trigger rules you should define.
- Security Incidents and Control Failures: Monitor reported breaches, security incidents, or control breakdowns affecting vendors. Any confirmed incident involving sensitive data or core systems should immediately elevate the vendor’s risk status.
- Certification and Evidence Expiry: Track expiration dates for certifications, attestations, and policy documents. Lapsed evidence weakens your risk posture and requires prompt reassessment or follow-up validation.
- External Intelligence and Public Signals: Monitor credible news sources, regulatory actions, and open-source intelligence related to vendor misconduct, sanctions, or litigation. These signals often indicate emerging reputational or compliance risk.
- Financial and Organizational Changes: Identify changes such as mergers, acquisitions, leadership turnover, or financial distress. Structural changes can impact service stability and risk ownership.
- Defined Trigger Rules For Reassessment: Establish clear rules that initiate reassessments, such as a confirmed breach, material contract change, or loss of critical certification. Trigger-based reviews ensure risk responses are timely and consistent.
A structured monitoring and trigger model ensures third-party risk oversight remains current, defensible, and aligned with ongoing regulatory expectations rather than point-in-time reviews.
Step 8: Integrate With Contracts and Procurement Controls
Risk assessments lose effectiveness if findings are not enforced through contracts and procurement decisions. Integrating risk requirements into procurement ensures accountability begins before onboarding and continues throughout the vendor lifecycle.
Below are the essential contractual elements and practical controls to embed.
- Data Processing and Confidentiality Obligations: Require a formal data processing addendum that defines permitted data use, storage locations, security safeguards, and breach notification timelines aligned with policyholder protection expectations.
Sample language: “Vendor shall process policyholder data solely for contracted services and implement safeguards no less protective than industry standards.”
- Service Level Agreements and Performance Commitments: Define SLAs tied to service availability, response times, and recovery objectives. Clear performance obligations reduce operational risk and support enforcement when service failures occur.
- Audit and Examination Rights: Include explicit rights to audit vendor controls or request independent assurance reports. Audit rights are critical for responding to regulator or examiner evidence requests.
Sample language: “Vendor agrees to provide audit reports or supporting evidence upon reasonable request.”
- Subcontractor and Fourth-Party Obligations: Require disclosure and oversight of subcontractors. Contracts should mandate equivalent risk controls and flow-down obligations to reduce downstream exposure.
- Termination and Risk Exit Provisions: Define termination rights tied to material control failures or regulatory risk. Exit provisions protect continuity and demonstrate proactive risk governance.
Contract Review Checklist
- Data protection and breach notification clauses included
- SLAs aligned to service criticality
- Audit and evidence access rights defined
- Subcontractor governance requirements documented
- Termination and transition support provisions validated
Embedding risk controls into contracts and procurement decisions ensures assessment outcomes translate into enforceable obligations, strengthening compliance, operational resilience, and exam readiness.
Step 9: Prepare Audit-Ready Evidence and Reporting
During state exams and internal audits, the quality of your evidence matters as much as the controls themselves. Disorganized or incomplete documentation creates delays, follow-up questions, and credibility risk.
Below is a practical approach to packaging evidence and reporting outcomes.
- Versioned and Controlled Documentation: Maintain version-controlled policies, assessments, and remediation records. A clear version history shows examiners that documents are actively maintained rather than created for audit purposes.
- Date-Stamped Operational Evidence: Capture date-stamped screenshots, system logs, and workflow records that demonstrate when assessments, reviews, and approvals occurred. Time-bound evidence supports traceability and control effectiveness.
- Signed Attestations and Approvals: Retain signed management attestations, vendor confirmations, and internal approvals. Attestations validate accountability and formal risk acceptance decisions.
- Centralized Evidence Repository: Store all third-party risk evidence in a centralized location with consistent naming conventions. Centralization reduces response time and minimizes the risk of missing documentation during exams.
Sample Audit Evidence Index
| Evidence ID | Vendor Name | Control Area | Evidence Type | Review Date | Owner |
| TPR-001 | Vendor A | Data Security | SOC 2 Report | 03/15/2026 | Compliance |
| TPR-002 | Vendor B | Business Continuity | DR Test Results | 02/28/2026 | Risk |
| TPR-003 | Vendor C | Incident Response | Signed Attestation | 01/10/2026 | Legal |
A structured evidence and reporting approach enables faster audit responses, reduces examiner friction, and reinforces confidence in your third-party risk governance program.
Also Read: Your Guide to Major Life Science Compliance Risks
Beyond general controls, third-party risk must also be evaluated through an industry-specific lens to meet sector-based regulatory expectations.
Industry-Specific Considerations
Third-party risk does not affect every industry in the same way. As a compliance leader, you often rely on vendors embedded across regulated sectors, each with distinct risk signals and examination expectations.
Below are key considerations and targeted assessment add-ons by industry.
1. Financial Services Vendors: Vendors supporting payments, data aggregation, or financial reporting introduce heightened concentration and resiliency risk. Regulators expect evidence that you understand dependency levels and contingency planning, consistent with OCC third-party risk management guidance.
Suggested assessment add-ons:
- Vendor concentration analysis and exit feasibility
- Business continuity and stress-testing results
- Financial solvency and ownership transparency
2. Healthcare Vendors: Vendors handling claims adjudication, care management, or health data must meet strict HIPAA obligations. You must demonstrate clear accountability for Business Associate Agreements and defined breach notification workflows.
Suggested assessment add-ons:
- Executed Business Associate Agreements
- Breach notification timelines and escalation procedures
- Data minimization and retention controls
3. Manufacturing and Energy Vendors: Vendors supporting operational technology, infrastructure services, or supply chain logistics introduce continuity and safety risks. Disruptions can affect underwriting assumptions and claims exposure.
Suggested assessment add-ons:
- Operational technology access controls
- Supply chain dependency mapping
- Disaster recovery and site resiliency evidence
VComply’s GRCOps Suite unifies ComplianceOps, RiskOps, PolicyOps, and CaseOps into a single platform, enabling continuous monitoring, trigger-based reassessments, and lifecycle oversight. Your organization gains real-time visibility into third-party risks, ensuring timely remediation and defensible governance across every vendor relationship.
Now, let us have a look at some of the common pitfalls you should avoid.
Common Pitfalls and How To Avoid Them
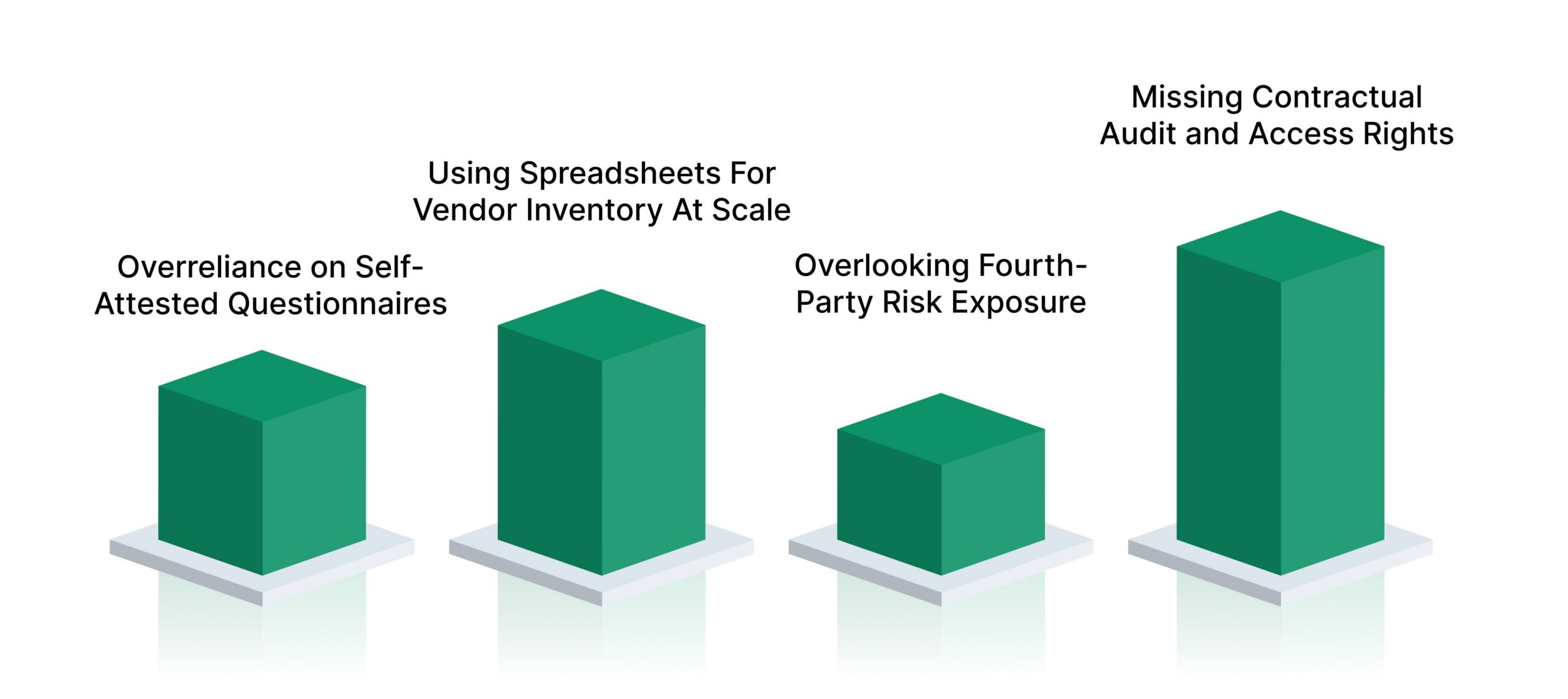
Even mature organizations encounter recurring breakdowns in third-party risk management. These issues often emerge during regulatory exams or incident reviews, when remediation is costly and time-sensitive. Understanding common pitfalls allows you to strengthen controls proactively and demonstrate disciplined risk governance.
Below are frequent challenges and how to address them.
- Overreliance on Self-Attested Questionnaires: Accepting vendor responses without independent validation weakens risk conclusions. Regulators expect evidence that controls operate effectively, not just that policies exist.
- Using Spreadsheets For Vendor Inventory At Scale: Spreadsheets lack version control, audit trails, and accountability. As vendor ecosystems grow, this approach increases the risk of omissions and inconsistent oversight.
- Overlooking Fourth-Party Risk Exposure: Failing to assess vendor subcontractors creates blind spots in your risk posture. Downstream failures often surface as direct regulatory and operational issues.
- Missing Contractual Audit and Access Rights: Without clear audit rights, you may be unable to obtain evidence during exams or incidents. Contracts must support ongoing oversight, not just initial onboarding.
Also Read: 7 Essential Steps for Effective Third-Party Due Diligence
To support consistent execution and documentation, the following questionnaire outline provides a practical reference point.
Appendix: Sample Assessment Questionnaire Outline
This appendix provides a structured outline you can use to design consistent third-party risk assessment questionnaires. The intent is to support efficient evidence collection while maintaining defensibility during state examinations. Questions should be tailored by vendor risk tier, but the core structure should remain consistent.
Section A: Organizational & Legal Information
- What is the vendor’s legal entity name and ownership structure?
- Which services are provided to your organization?
- Where are the primary operations and data processing locations based?
- Who is accountable for compliance and risk oversight within the organization?
- Has the vendor been subject to regulatory actions or litigation in the last three years?
Section B: Security Controls & Certifications
- Which security frameworks or standards are formally adopted?
- Are independent assurance reports available (for example, SOC 2 Type II)?
- How is access to systems and data authenticated and reviewed?
- How are security incidents detected, escalated, and investigated?
- When was the most recent security assessment or penetration test completed?
Section C: Data Handling & Privacy
- What categories of data are collected, processed, or stored on your behalf?
- How is sensitive data encrypted in transit and at rest?
- What data retention and deletion practices are followed?
- How are privacy obligations communicated to employees and subcontractors?
- What is the breach notification process and required response timeframe?
Section D: Business Continuity & Resilience
- Is a documented business continuity and disaster recovery plan maintained?
- What recovery time and recovery point objectives are defined?
- How often are continuity plans tested and validated?
- What dependencies could disrupt service delivery?
- How are clients notified during operational disruptions?
Section E: Subcontractors and Fourth Parties
- Does the vendor rely on subcontractors to deliver contracted services?
- How are subcontractors vetted and monitored for risk?
- Are equivalent security and compliance obligations contractually enforced?
- How is subcontractor performance reviewed and documented?
- How are changes to subcontractor relationships communicated?
This outline supports consistent, scalable assessments while ensuring evidence collected aligns with audit expectations and ongoing third-party risk oversight.
How VComply Simplifies Third-Party Risk Assessment
Executing third-party risk assessments at scale requires more than defined steps and templates. You need a system that operationalizes the entire lifecycle, maintains defensible evidence, and supports regulatory and executive scrutiny. VComply serves as the execution layer that connects assessment activities, documentation, and oversight into a single, controlled process.
Below is how VComply maps directly to each stage of third-party risk assessment.
- Centralized Vendor Registry and Risk Classification: VComply provides a single source of truth for all third-party relationships, capturing vendor profiles, criticality, data access, contracts, and ownership details.
- Automated Assessments and Evidence Collection: Standardized assessment workflows allow you to issue role-based questionnaires, collect structured responses, and attach supporting evidence in one place. Evidence is automatically time-stamped and versioned, reducing manual follow-ups and strengthening audit readiness.
- Risk Scoring and Executive Dashboards: Configurable scoring models translate assessment findings into clear risk ratings aligned with your defined thresholds. Dashboards provide real-time visibility into vendor risk posture, remediation status, and trends, enabling confident reporting to senior management and boards.
- Remediation Workflows and Accountability: Identified issues are converted into tracked remediation actions with assigned owners, SLA-based deadlines, escalation rules, and verification requirements. This ensures risk treatment is documented, measurable, and defensible during audits.
- Continuous Monitoring and Lifecycle Oversight: VComply supports ongoing monitoring through scheduled reviews, trigger-based reassessments, and evidence renewal tracking. Changes in vendor risk are captured and reflected without relying on manual intervention.
- Unified GRC Operations Across All Ops Modules: Third-party risk management within VComply integrates seamlessly across ComplianceOps, RiskOps, PolicyOps, and CaseOps, ensuring vendor risks align with regulatory obligations, enterprise risk posture, policy enforcement, and incident handling within a unified GRCOps framework.
Also Read: Top 10 Archer Alternatives for Compliance in 2026
By aligning technology directly with process, VComply enables organizations to move from fragmented assessments to a scalable, audit-ready third-party risk management program with clear executive visibility. Book a demo with VComply and see how it works for your business.
Final Thoughts
Third-party risk assessment has evolved into a core governance discipline for organizations operating in a highly regulated, interconnected environment. As vendor ecosystems grow more complex, your ability to demonstrate structured oversight, timely remediation, and audit-ready evidence directly influences regulatory outcomes, operational resilience, and leadership confidence.
VComply enables you to execute third-party risk assessment as a continuous, well-governed process rather than a manual, fragmented exercise. By centralizing vendor data, automating assessments, and supporting executive and examiner reporting, VComply helps compliance leaders maintain control, consistency, and accountability across the entire third-party lifecycle.
Start your 21-day free trial of VComply to strengthen your third-party risk assessment program with confidence and clarity.
FAQs
Critical vendors should be reassessed at least annually, while moderate- and low-risk vendors may follow a longer cycle. Reassessments should also occur after incidents, contract changes, regulatory updates, or material changes in the vendor’s operations or ownership.
Regulators commonly request vendor inventories, completed risk assessments, evidence artifacts, remediation records, contracts with audit rights, and governance reporting. They also look for proof of periodic reviews, issue tracking, and documented risk acceptance decisions tied to senior management oversight.
You should prioritize vendors based on business criticality, data sensitivity, and regulatory exposure. Focusing resources on high-risk and critical vendors demonstrates a risk-based approach, which regulators expect, while allowing lower-risk vendors to follow streamlined assessment and monitoring processes.
Inherent risk reflects the level of risk a vendor poses before controls are applied. Residual risk represents the remaining exposure after evaluating and mitigating control gaps. Regulators expect both to be documented, along with management’s approval of any accepted residual risk.
Yes, when assessments are mapped to common control objectives, evidence can support multiple frameworks. A single assessment may address SOC 2, HIPAA, and state requirements, provided documentation clearly demonstrates how controls align with each applicable regulatory expectation.

