Certificate of Compliance: What Companies Need to Provide in 2026
When regulators request documentation, vendors demand proof, and auditors arrive unannounced, compliance becomes the core of trust and continuity. A certificate of compliance shows that your products, processes, or systems meet legal, regulatory, or contractual requirements.

For compliance officers, risk managers, CTOs, and CEOs in the U.S., managing these certificates directly affects audit outcomes, third-party trust, and regulatory relationships. As requirements grow, firms must dedicate more resources to compliance, highlighting its critical and complex role.
In this blog, we will explain what a certificate of compliance is, when you need it, what it should contain, who issues it, how you validate it, and how to manage it as part of ComplianceOps.
Key Takeaways
- A certificate of compliance formally documents adherence to regulatory, contractual, or internal requirements, supporting audit readiness and third-party trust.
- Effective compliance depends on a clearly defined scope, traceable evidence, formal authorization, and timely review cycles.
- Validation includes checking the issuer, requirement alignment, evidence, dates, and transaction traceability.
- Common failures include expired certificates, missing scope, inconsistent templates, and a lack of review processes.
- A structured operating model with tools like VComply ComplianceOps centralizes certificates, automates workflows, links evidence, and provides audit-ready reporting.
Did you know?
Regulatory requirements and compliance are now one of the top three business challenges in over 80% of surveyed countries. This is more than twice as many firms cite compliance burden as a challenge compared with concerns like talent acquisition or taxation.
Certificate of Compliance Meaning
A Certificate of Compliance (CoC) is a formal declaration showing that products meet defined obligations and regulatory standards. It’s essential for both domestic and international trade, providing proof of quality, safety, and legal compliance.
For U.S. imports, a CoC supports Customs clearance by confirming adherence to FDA, EPA, or CPSC regulations. For exports, it ensures the product meets the destination country’s standards, helping prevent delays or penalties.
Below are the key dimensions that define what a certificate of compliance represents in practice:
- Scope of Compliance: A certificate of compliance can apply to a product, service, system, process, or the organization as a whole. The scope must be explicit, because regulators and examiners evaluate compliance only within the stated boundary.
- Defined Requirements: The certificate references specific requirements, such as state insurance laws, federal regulations, industry standards, contractual obligations, or internal framework controls. Ambiguous or bundled requirements weaken their credibility during examinations.
- Evidence-Based Assertion: A certificate is not merely a statement of intent. It represents an assertion that compliance exists and can be supported with underlying documentation, controls, testing results, or operational records if requested.
- Context-Dependent Interpretation: The meaning of a certificate of compliance varies by context. In supply chains, it often supports vendor qualification, while in regulated industries like insurance, it signals exam readiness, control effectiveness, and ongoing regulatory accountability.
Certain categories of goods almost always require certification to clear international regulatory checks:
- Medical Equipment: Surgical tools, diagnostic devices, and hospital machinery.
- Industrial Chemicals and Materials: Including paints, solvents, and raw materials used in manufacturing.
- Consumer Goods: Clothing, toys, and household appliances.
- Agricultural Products: Seeds, fertilizers, and packaged food items.
- High-Tech Electronics: Smartphones, networking devices, and audio-visual equipment.
With a clear understanding of what a certificate of compliance represents, the next step is to explore what it actually proves, and the limitations you need to be aware of during audits and regulatory reviews.
What A Certificate Of Compliance Proves (and What It Does Not)
A certificate of compliance often appears to be definitive proof during audits and regulatory reviews. In reality, its strength depends on who issued it, how clearly the scope is defined, and whether supporting evidence exists.
What a certificate of compliance typically proves:
- Defined Requirement Was Met: The certificate confirms that a specific regulatory, contractual, or framework requirement was met at a defined point in time, based on the scope stated in the document.
- Alignment To A Stated Standard: It shows that a product, batch, service, system, or process aligns with a referenced standard or control set, as identified on the certificate.
- Formal Accountability Exists: A named, authorized party has reviewed the assertion and formally attested to compliance by signing the certificate, establishing ownership and responsibility.
What a certificate of compliance does not automatically prove:
- Ongoing or Continuous Compliance: Compliance can change after issuance. Regulators expect organizations to demonstrate continued adherence, not rely solely on a past certificate.
- Existence of Supporting Evidence: Unless the certificate references retained testing results, control documentation, or inspection records, it does not guarantee that evidence is available or sufficient.
- Independent Verification: Many certificates are self-issued. Without third-party validation, regulators may require additional documentation to confirm objectivity and reliability.
Also Read: Manufacturing Compliance Checklist: Complete 2026 Guide
Knowing what a certificate can and cannot prove naturally leads to understanding who is qualified to issue it, as the credibility of the document depends heavily on the issuer.
Who Issues A Certificate Of Compliance?
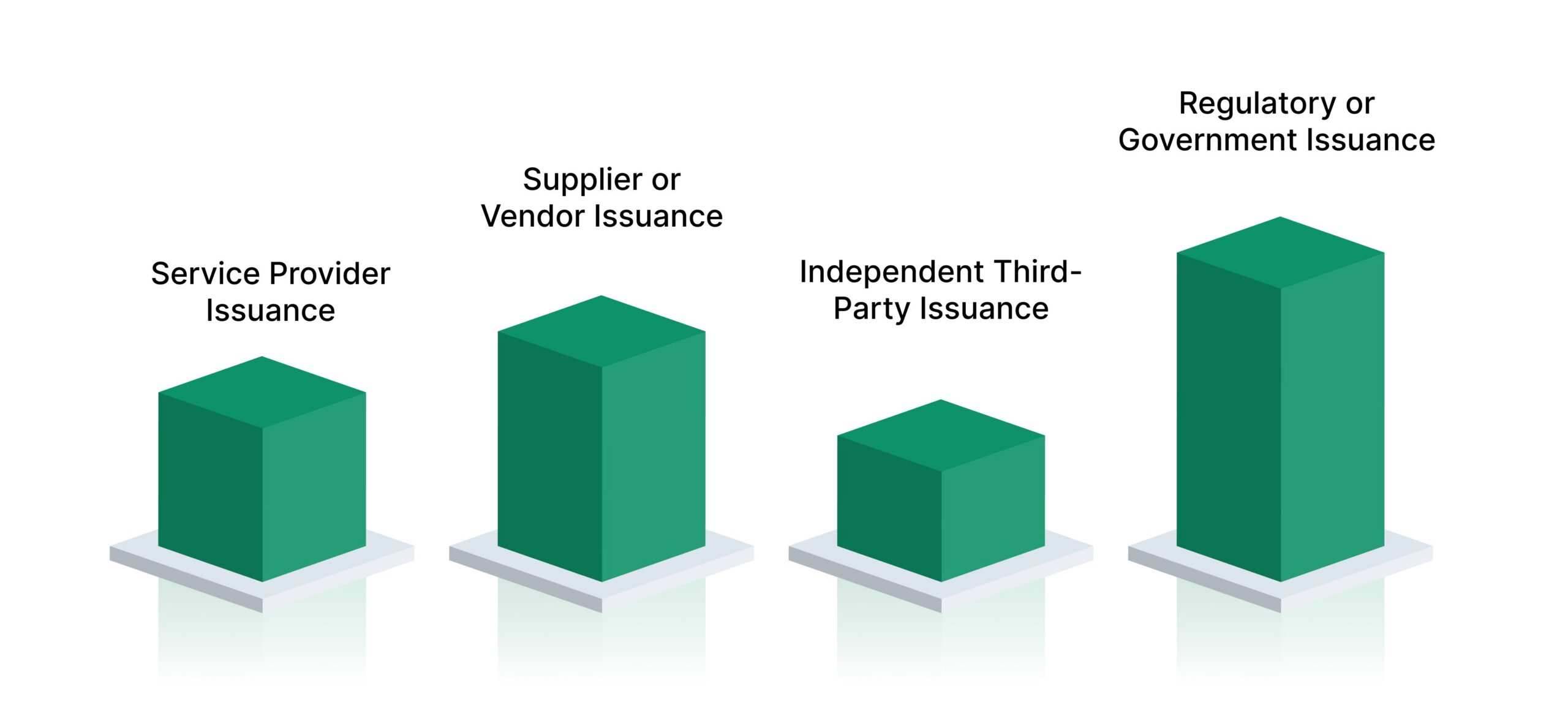
A certificate of compliance is only as credible as its issuer. For US compliance leaders, identifying who issued the certificate helps determine how regulators will assess its reliability, objectivity, and evidentiary value during examinations and audits.
Below are the primary issuer types and when each is typically appropriate:
- Manufacturer or Service Provider Issuance: Common when compliance relates to internally controlled products, services, or operational processes. This issuer type is typically accepted when the organization maintains strong internal controls and can produce supporting evidence during regulatory reviews.
- Supplier or Vendor Issuance: Frequently used in third-party risk and vendor management scenarios. Vendors issue certificates to confirm alignment with contractual, regulatory, or control requirements, particularly during onboarding or periodic due diligence.
- Independent Third-Party Issuance: Issued by accredited laboratories, assessors, or certification bodies when independent validation is required. Regulators and examiners often expect this issuer type for higher-risk activities or where objectivity is critical.
- Regulatory or Government Issuance: Provided directly by federal or state authorities in limited circumstances. These certificates carry the highest evidentiary weight and are typically associated with licensing, authorization, or formal regulatory approval processes.
VComply Compliance Ops centralizes certificates, links them to regulations and controls, and automates review and renewal tasks. This ensures your compliance evidence is always audit-ready and accessible to the right teams.
Once you know who can issue a certificate of compliance, it’s important to determine the situations in which obtaining one is necessary to satisfy regulatory, contractual, or internal requirements in the US.
When You Need A Certificate Of Compliance In The US
In the US regulatory environment, the need for a certificate of compliance is driven by who is requesting assurance and how that assurance will be reviewed. Requirements often arise through state regulators, enterprise customers, and third-party oversight expectations rather than a single federal mandate.
Below are the most common situations where a certificate of compliance is required:
- Vendor Onboarding and Third-Party Risk Reviews: Certificates are frequently requested to demonstrate that vendors meet regulatory, security, or operational requirements before contracts are executed or renewed.
- Customer Audits and Enterprise Procurement Reviews: Large customers and partners often require certificates to confirm compliance with contractual controls, especially during initial due diligence or periodic assessments.
- Regulatory Examinations and Inspections: State departments may request certificates as supporting documentation to validate adherence to specific laws, regulations, or internal control frameworks.
- Product Shipments and Import Requirements: When applicable, certificates support compliance assertions related to regulated products, cross-border transactions, or controlled materials.
- Contractual Deliverables and Quality Agreements: Many MSAs and quality agreements explicitly require certificates as formal proof that defined obligations have been met.
Use the following decision lens to determine when certificates should be treated as controlled compliance records:
- A Defined Requirement Exists: The obligation is clearly documented in a regulation, contract, or internal framework.
- An Accountable Owner Is Identified: Responsibility for compliance and certification is formally assigned.
- Evidence Must Be Retained and Defensible: Supporting documentation may be requested during audits or examinations and must be accessible and complete.
After understanding when certificates are required, it’s helpful to look at common use cases across different industries to see how they support compliance, audits, and third-party assurance in practice.
Common Certificate Of Compliance Use Cases By Industry
Certificates of compliance appear across industries, but their role changes based on regulatory pressure, risk exposure, and procurement complexity. Below are common certificate of compliance use cases across key industries:
- Financial Services: Certificates support vendor risk assessments, confirm adherence to regulatory controls, and document compliance with contractual obligations during audits and regulatory examinations.
- Healthcare: Organizations rely on certificates to demonstrate alignment with healthcare regulations, data protection requirements, and operational standards when engaging vendors or undergoing inspections.
- Manufacturing: Certificates validate that products, materials, or production processes meet specified regulatory and quality standards, often forming part of supplier qualification and acceptance workflows.
- Higher Education: Institutions use certificates to confirm vendor compliance with data security, privacy, and operational requirements, particularly when managing third-party services and research partnerships.
- Energy: Certificates help demonstrate compliance with safety, environmental, and operational standards, supporting regulatory reviews and contractor oversight in high-risk operating environments.
VComply’s GRCOps Suite integrates your compliance, risk, policy, and incident data into a single, auditable platform. This gives you complete visibility across the enterprise and ensures all regulatory, contractual, and operational obligations are continuously met.
With use cases in mind, the next step is defining what information a certificate of compliance must include to be auditable, reliable, and defensible during regulatory or contractual reviews.
What Information Should a Certificate Of Compliance Include
A certificate of compliance must withstand regulatory scrutiny, not just acknowledge intent. A well-structured certificate reduces follow-up requests and strengthens confidence during audits and examinations.
Below are the core elements that should appear in an auditable certificate of compliance:
- Issuer Legal Identity: The full legal name and registered address of the issuing entity, enabling regulators to verify responsibility and jurisdiction.
- Scope Identifier: A precise identifier for the product, service, system, or process covered, such as a SKU, model number, batch or lot, system name, or version.
- Referenced Requirement: The exact regulation, standard, contractual clause, or internal control the certificate addresses, avoiding broad or undefined assertions.
- Compliance Statement: A clear declaration describing what requirement was met and within what scope, timeframe, and conditions.
- Evidence References: Identifiers for supporting documentation, such as test reports, audit findings, inspection records, or control assessments, that substantiate the claim.
- Issuance and Validity Details: The date the certificate was issued and the period for which the compliance assertion remains valid.
- Authorized Sign-Off: The name and title of the individual authorized to attest to compliance, establishing formal accountability.
- Traceability References: Links to related purchase orders, shipments, contracts, or control identifiers that connect the certificate to business and compliance workflows.
To exceed baseline expectations, apply the following framing:
- Minimum Certificate Standard: Includes a compliance statement and authorized sign-off, offering limited assurance.
- Audit-Ready Certificate Standard: Includes defined scope, evidence identifiers, and traceability references, enabling faster reviews and defensible exam outcomes.
Also Read: Simplifying Compliance Workflows with VComply
After defining what a certificate should include, it’s key to distinguish it from similar documents to avoid confusion.
Certificate Of Compliance vs Certificate Of Conformity vs Certification vs Attestation
Across industries and search results, these terms are often used interchangeably, which creates confusion during audits and regulatory reviews. Understanding the practical and evidentiary differences between them is essential to ensuring the right documentation is produced, reviewed, and retained for examinations.
Below is a clear comparison to distinguish how each is used in practice:
- Certificate of Compliance: Declares that a specific regulatory, contractual, or framework requirement was met within a defined scope and time period, typically supported by internal or external evidence.
- Certificate of Conformity: Indicates that a product or deliverable aligns with predefined specifications or technical standards, with usage varying by industry and supply-chain context.
- Certification: Represents formal recognition that an organization, system, or product meets a standard, usually granted by an accredited certification body following an independent assessment.
- Attestation: A formal statement made by a responsible individual or organization asserting that certain conditions or controls exist, often used to support regulatory or contractual obligations.
In supply-chain and procurement contexts, some sources use “compliance” and “conformity” interchangeably; however, in regulated environments, examiners expect precise terminology aligned to the underlying requirement and evidence model.
With the differences clarified, the next step is understanding how to obtain a certificate of compliance effectively.
How To Get A Certificate Of Compliance
Obtaining a certificate of compliance requires a disciplined, repeatable process that aligns regulatory expectations with documented evidence. Regulators evaluate not only the certificate itself but also the rigor of the workflow used to produce it, particularly during state examinations and third-party reviews.
Below is a practical, exam-ready workflow for issuing a certificate of compliance:
- Identify the Applicable Requirement: Determine the precise regulation, contractual obligation, or internal control that must be satisfied, ensuring there is no ambiguity about what compliance means.
- Define the Compliance Scope: Specify what the certificate covers, such as a product, system, site, process, version, or time period, to prevent overbroad or unsupported assertions.
- Collect Supporting Evidence: Gather documentation that demonstrates compliance, including audit reports, testing results, inspections, policy records, or control assessments.
- Validate Evidence Quality: Confirm who produced the evidence, when it was generated, and whether it fully supports the stated requirement and defined scope.
- Draft the Certificate Using A Controlled Template: Use a standardized format that consistently captures scope, requirements, and accountability across the organization.
- Obtain Authorized Approval and Sign-Off: Secure formal approval from an individual with documented authority to attest to compliance.
- Store With Traceability: Retain the certificate alongside linked requirements and evidence to support future audits and examinations.
- Establish Review and Renewal Cadence: Define how often the certificate must be reviewed, renewed, or replaced based on regulatory or contractual expectations.
Once you know how to obtain a certificate, it’s equally important to validate any certificate you receive to ensure it’s accurate and reliable.
How To Validate A Certificate Of Compliance You Receive
Most search results explain what a certificate of compliance is, but few address how to verify one when it arrives from a vendor, partner, or internal team. Validation is critical because regulators expect you to assess the reliability of third-party assertions, not accept them at face value.
Below is a structured checklist to validate a certificate of compliance before relying on it:
- Requirement and Scope Alignment: Confirm that the certificate cites the correct regulation, contractual obligation, or control and that the stated scope matches what you are relying on for compliance.
- Issuer Appropriateness: Assess whether the issuer type is suitable for the requirement, such as a manufacturer, independent third party, or regulator, based on risk and regulatory expectations.
- Evidence Availability and Accessibility: Verify that referenced evidence exists, is retrievable, and can be produced promptly if requested during an audit or examination.
- Date and Validity Accuracy: Ensure the issuance date and validity period align with your review cycle, regulatory timelines, and contractual obligations.
- Authorized Signatory Confirmation: Confirm that the individual who signed the certificate holds appropriate authority and accountability for the compliance assertion.
- Transaction Traceability: Check that the certificate can be traced to the relevant purchase order, shipment, contract, or engagement it is intended to support.
Also Read: Workflow Automation for Compliance Programs
After learning how to validate certificates, it’s crucial to understand common mistakes that can lead to audit findings and compliance gaps.
Common Mistakes That Cause Audit Findings
Audit findings related to certificates of compliance rarely stem from intent. They arise when operational discipline breaks down across ownership, evidence management, and review processes. Below are common compliance operations failures that frequently lead to audit findings:
- Expired Certificates Treated As Current Evidence: Organizations rely on certificates that no longer align with the review period, creating gaps between asserted and actual compliance.
- Undefined or Incomplete Scope: Certificates fail to specify the applicable batch, system, site, version, or time period, weakening their reliability during examination.
- Missing Evidence Linkage: Compliance assertions lack references to underlying documentation, making it difficult to substantiate claims when challenged.
- Decentralized and Uncontrolled Storage: Certificates are scattered across emails or shared drives without clear ownership, version control, or access governance.
- Inconsistent Certificate Templates: Different business units issue certificates using varied formats, leading to uneven quality and regulator confusion.
- Absent Review and Exception Processes: Certificates are issued without defined review cycles or mechanisms to address gaps, deviations, or expired assertions.
With VComply Risk Ops, you can proactively identify where compliance gaps create operational and regulatory risks, assign ownership, and monitor mitigation actions. This reduces the likelihood of audit findings and regulatory penalties.
Now, the next step is implementing a simple operating model to track certificates efficiently across their lifecycle.
Certificate Of Compliance Tracking: A Simple Operating Model
Managing certificates of compliance at scale requires a repeatable operating model that aligns people, process, and accountability. Below is a simple operating model that supports consistent, exam-ready certificate management:
- Intake (Collect or Request): Certificates are requested or received from internal teams or third parties at defined trigger points, such as vendor onboarding, contract execution, or regulatory milestones. Ownership is typically shared between the business owner and the vendor manager.
- Review (Validate): Compliance and QA teams validate scope, issuer suitability, evidence references, and alignment with regulatory or contractual requirements before acceptance.
- Approve (Sign or Accept): Authorized owners formally approve internally issued certificates or accept third-party certificates, establishing accountability and readiness for examination.
- Monitor (Renew, Replace, or Retire): Compliance owners oversee ongoing monitoring, ensuring certificates are renewed, replaced, or retired based on validity periods, regulatory changes, or business events, with legal involvement as needed.
Once a tracking model is established, you can use VComply ComplianceOps to streamline management, ensure accountability, and maintain audit-ready certificates.
How VComply ComplianceOps Helps You Manage Certificates Of Compliance
Once an operating model is defined, execution becomes the challenge. Managing certificates across teams, vendors, and regulatory obligations requires system-level support to maintain consistency, visibility, and accountability without manual coordination.
VComply ComplianceOps enables outcomes-driven certificate management by supporting the full compliance lifecycle:
- Centralized Certificate and Evidence Repository: ComplianceOps provides a single source of truth for certificates of compliance and their supporting evidence, reducing fragmentation and retrieval delays during audits and examinations.
- Framework and Control Mapping: Certificates are directly linked to applicable regulations, contractual obligations, and internal controls, ensuring every compliance assertion is traceable and defensible.
- Structured Task Assignment and Accountability: Review, approval, and renewal responsibilities are assigned to defined owners, creating clear accountability across compliance, business, vendor management, QA, and legal teams.
- Automated Review and Expiration Management: The platform tracks validity periods and triggers reminders for reviews, renewals, or replacements, reducing reliance on manual follow-ups.
- Audit-Ready Reporting and Visibility: ComplianceOps delivers real-time insight into certificate coverage, gaps, and status by vendor, business unit, or requirement, supporting faster and more confident regulatory responses.
- Integrated ComplianceOps, RiskOps, PolicyOps, and CaseOps: Certificates are managed within a connected GRC operating layer, where compliance requirements, third-party risks, policy obligations, and incident records align to provide a complete, defensible compliance posture.
Also Read: Top 10 Real Estate Compliance Management Software in Dubai for 2025
With a strong platform in place, organizations can transform certificate management from a manual task into a structured, audit-ready process, setting the stage for stronger compliance outcomes. Book a demo with VComply to see it in action.
Final Thoughts
A certificate of compliance is more than a document collected for audits or vendor files. It functions as a measurable compliance signal that reflects how well requirements, ownership, and evidence are operationalized across the enterprise. When managed intentionally, certificates strengthen regulatory confidence, reduce examination friction, and support consistent compliance outcomes across state and business lines.
VComply helps compliance leaders move beyond document collection by turning certificates of compliance into governed, traceable, and auditable compliance records. Through ComplianceOps, organizations align certificates to regulatory requirements, controls, and evidence while maintaining accountability and visibility across teams.
Start a 21-day free trial to see how VComply ComplianceOps helps you manage certificates of compliance with clarity, control, and exam-ready confidence.
FAQs
A certificate of compliance is not universally mandatory, but it is required whenever regulators, contracts, or internal frameworks demand documented proof of adherence. In US organizations, it becomes essential during audits, vendor onboarding, or compliance examinations to demonstrate accountability and traceable adherence to applicable laws and controls.
Validity depends on regulatory, contractual, or internal control requirements. Typically, certificates are valid until the scope, process, or regulatory period changes. Organizations should track issuance and expiration dates, ensuring timely renewal or reissuance to maintain continuous compliance for audit readiness and regulatory examinations.
Responsibility usually lies with designated compliance owners, business unit leaders, or QA teams. In higher-risk areas, legal and executive sign-off may be required. Clear assignment ensures accountability, reduces errors, and supports regulatory exam expectations, confirming that certificates are authoritative and backed by validated evidence.
Submitting an invalid certificate can trigger audit findings, regulatory notices, or corrective actions. Examiners may require additional evidence, extend review periods, or escalate issues. It undermines trust, increases scrutiny, and may result in operational or contractual penalties.
Yes, certificates may need revocation or reissuance if evidence changes, regulatory expectations change, or errors are identified. Organizations should maintain controlled workflows to revoke, update, and redistribute certificates, ensuring continuous compliance and minimizing exposure during audits or examinations. Proper version control is essential.

