7 Breakpoints in Automated Vulnerability Management and How to Fix Execution Gaps
Security advisories continue to highlight a recurring issue: vulnerabilities are identified quickly, but remediation and validation lag behind. Security teams rarely struggle with identifying vulnerabilities; they struggle with proving that those vulnerabilities were addressed, validated, and closed within defined timelines.

As vulnerability data increases across systems, tools generate alerts faster than teams can respond. Without structured workflows, vulnerabilities remain unassigned, remediation actions lack validation, and evidence is either incomplete or reconstructed later. This weakens accountability and creates uncertainty around actual risk exposure across the organization.
Agencies like CISA have underscored these challenges in their reports.
This guide explains where automated vulnerability management breaks in execution and how to structure it through workflows, ownership, and measurable outcomes.
At a Glance
- Vulnerability management fails when detection is not connected to remediation workflows, ownership, and evidence generation
- Severity scores alone do not reflect actual business risk without context from assets, data sensitivity, and exposure
- Execution gaps often occur between scanning tools, ticketing systems, and incident response workflows
- Audit readiness depends on linking vulnerabilities to actions, actions to owners, and outcomes to evidence
- Measurement should focus on remediation timelines, validation success, and exception handling, not scan volume
- Scalable programs require systemization across risk, compliance, and incident workflows within a unified structure
What Is Automated Vulnerability Management
Automated vulnerability management is the process of identifying, prioritizing, assigning, and remediating security vulnerabilities using structured workflows and integrated systems. It connects detection tools with remediation actions, ownership, and validation mechanisms.
Failures occur when automation stops at scanning and does not extend into execution. Without workflow integration, ownership tracking, and evidence generation, organizations cannot demonstrate whether vulnerabilities were addressed consistently or within defined risk thresholds.
Also read: How to Improve Compliance Management for Audit-Ready Programs 2026
6 Core Stages of Automated Vulnerability Management Across Systems and Teams
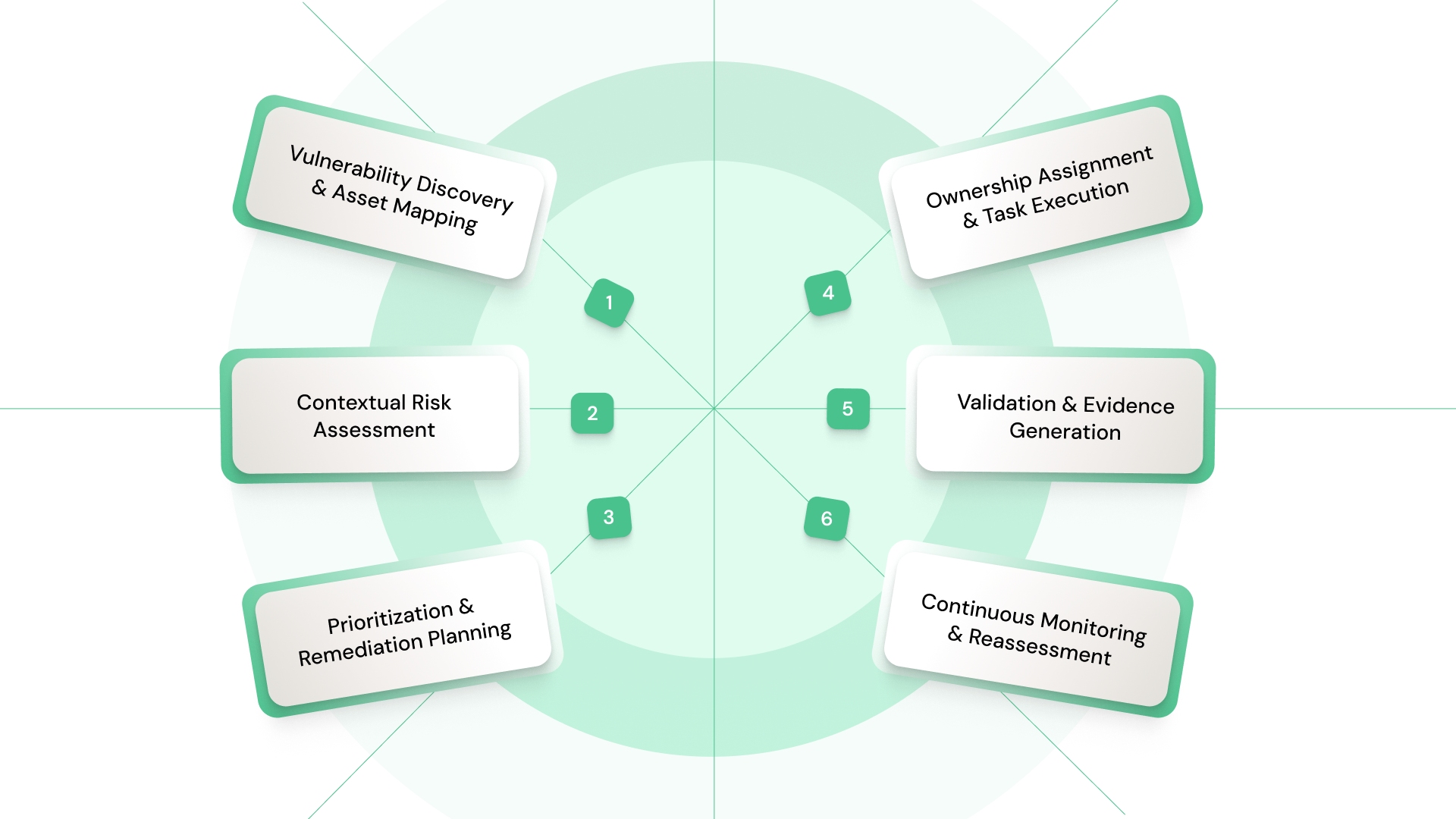
Automated vulnerability management must function as a continuous execution cycle rather than a sequence of isolated tools. Each stage should contribute to traceability, ownership, and measurable outcomes across systems:
The lifecycle becomes effective when each stage connects detection to validated remediation:
1. Vulnerability Discovery and Asset Mapping
Scanning tools identify vulnerabilities across infrastructure, applications, and endpoints, but their value depends on accurate asset mapping. Each vulnerability must be linked to specific systems, owners, and business functions.
Without asset context, vulnerabilities cannot be prioritized or assigned effectively, leading to delays and inconsistent remediation across environments.
2. Contextual Risk Assessment
Not all vulnerabilities carry equal impact, even if severity scores appear similar. Risk assessment must incorporate asset criticality, data sensitivity, and exposure levels.
This ensures that remediation efforts align with actual business risk instead of generic scoring models, improving prioritization accuracy across systems and teams.
3. Prioritization and Remediation Planning
Prioritization converts risk signals into actionable remediation plans with defined timelines. This includes assigning severity thresholds, remediation deadlines, and escalation criteria.
Without structured prioritization, teams address vulnerabilities inconsistently, focusing on volume rather than impact, thereby weakening the overall risk posture.
4. Ownership Assignment and Task Execution
Each vulnerability must be assigned to a specific owner responsible for remediation and validation. Tasks should include deadlines, dependencies, and escalation paths.
Without clear ownership, vulnerabilities remain unresolved or delayed, creating gaps that become visible during audits or incident investigations.
5. Validation and Evidence Generation
Remediation must be validated through testing, logs, or verification processes. Evidence should be generated during execution, not collected later. Without validation, organizations cannot confirm whether vulnerabilities were resolved effectively, reducing confidence in remediation outcomes.
6. Continuous Monitoring and Reassessment
Vulnerability management requires continuous monitoring to detect new exposures, validate recurring issues, and reassess risk. This ensures that remediation remains aligned with evolving threats and system changes, preventing vulnerabilities from reappearing without detection.
Also read: Business Resilience Framework: Building Operational Strength for 2026
Prioritizing Vulnerabilities Based on Risk Exposure, Not Severity Scores Alone
Severity scores provide a starting point, but they do not reflect how vulnerabilities impact business operations. Effective prioritization requires combining technical severity with contextual risk factors.
Prioritization becomes meaningful when risk signals guide remediation decisions:
1. Asset Criticality and Business Impact
Vulnerabilities affecting critical systems or sensitive data require immediate attention, regardless of their technical severity. Mapping vulnerabilities to business-critical assets ensures that remediation aligns with operational impact instead of generic scoring models.
2. Exposure and Attack Surface
External-facing systems or widely accessible applications increase the likelihood of exploitation. Vulnerabilities in these environments require higher prioritization due to their exposure, even if severity ratings appear moderate.
3. Exploit Availability and Threat Intelligence
Known exploits and active threat patterns increase the urgency of remediation. Integrating threat intelligence into prioritization ensures that vulnerabilities are addressed based on real-world risk rather than theoretical scoring.
4. Control Effectiveness and Compensating Measures
Existing controls may reduce the impact of certain vulnerabilities. Evaluating control effectiveness helps determine whether remediation can be deferred or requires immediate action, improving resource allocation across teams.
When prioritization starts combining asset context, exposure, and control effectiveness, maintaining consistency across systems becomes difficult without structure. VComply helps align vulnerability prioritization with risk, controls, and execution workflows.
Integrating Vulnerability Management With Incident Response and Case Handling
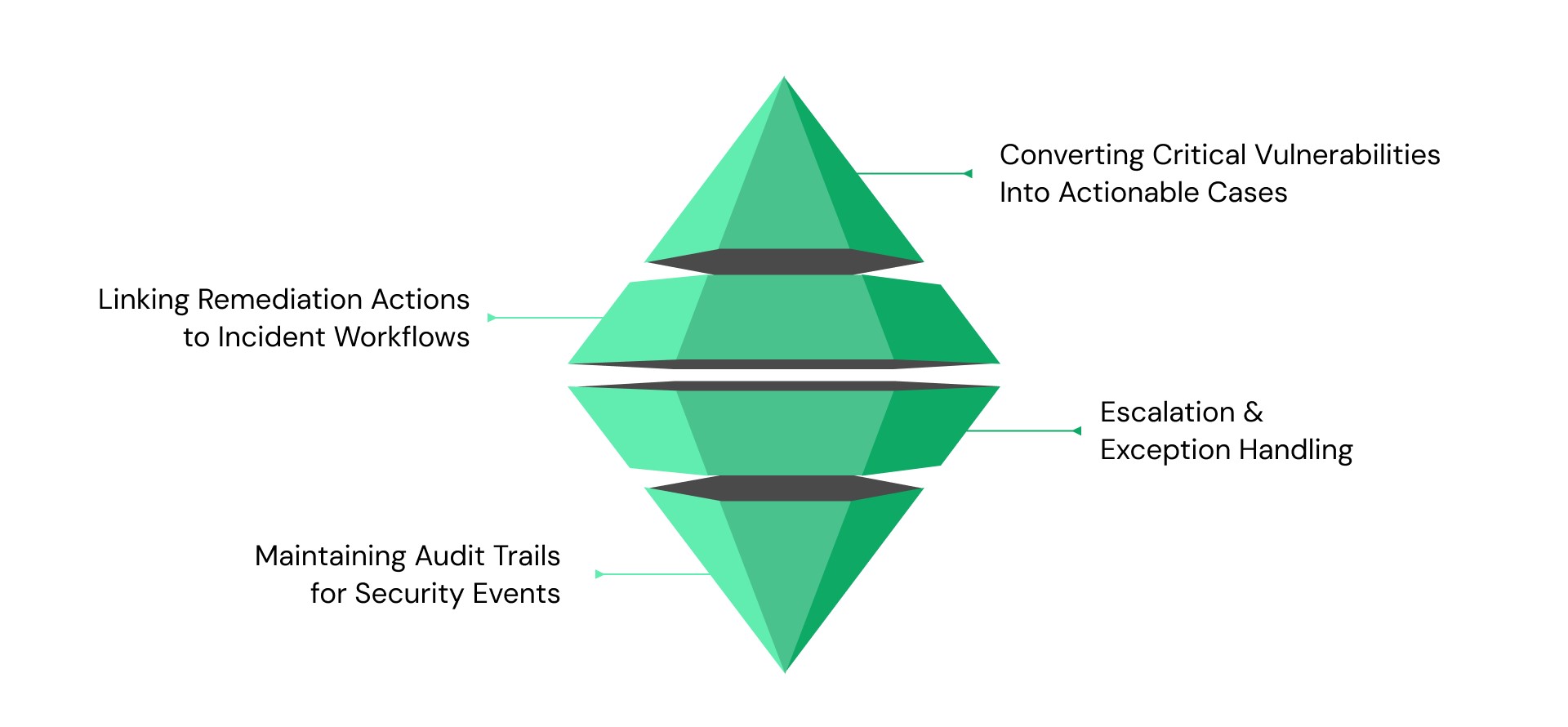
Vulnerability management and incident response often operate separately, creating gaps between detection and resolution. Integration ensures that vulnerabilities are tracked, escalated, and resolved through structured workflows:
Execution improves when vulnerabilities connect directly to incident workflows:
1. Converting Critical Vulnerabilities Into Actionable Cases
High-risk vulnerabilities should trigger case creation with defined ownership, timelines, and escalation paths. This ensures that critical issues are tracked and resolved systematically instead of being lost within scanning tools.
2. Linking Remediation Actions to Incident Workflows
Remediation tasks should follow structured workflows similar to incident handling, including investigation, action, validation, and closure. This creates consistency across security operations and improves accountability.
3. Escalation and Exception Handling
Unresolved vulnerabilities or delays should trigger escalation workflows. This ensures that high-risk issues receive attention and are not deprioritized due to operational constraints or workload distribution.
4. Maintaining Audit Trails for Security Events
Every remediation action should be logged with timestamps, ownership, and validation status. This creates a traceable audit trail that supports compliance requirements and incident investigations.
Also read: GDPR and CCPA: Key Differences and How You Stay Compliant
Measuring Vulnerability Management Effectiveness Using Execution Metrics
Measurement must focus on execution outcomes rather than scan volume. Effective metrics provide insight into whether vulnerabilities are resolved consistently and within defined timelines:
Performance becomes visible when execution is measured systematically:
1. Mean Time to Remediate (MTTR)
This metric measures how quickly vulnerabilities are resolved after detection. Delays indicate gaps in prioritization, ownership, or workflow efficiency, highlighting areas that require structural improvement.
2. Validation Success Rates
This measures whether remediation actions are verified successfully. Low validation rates indicate ineffective remediation or incomplete execution, which increases risk exposure across systems.
3. Exception and Deviation Trends
Recurring exceptions indicate systemic issues in workflows, ownership, or prioritization. Tracking these trends helps identify areas where vulnerability management fails to enforce consistent execution.
4. Evidence Completeness and Traceability
This measures whether remediation actions generate complete and verifiable evidence. Incomplete evidence reduces audit defensibility and indicates gaps in workflow integration.
7 Common Gaps in Automated Vulnerability Management
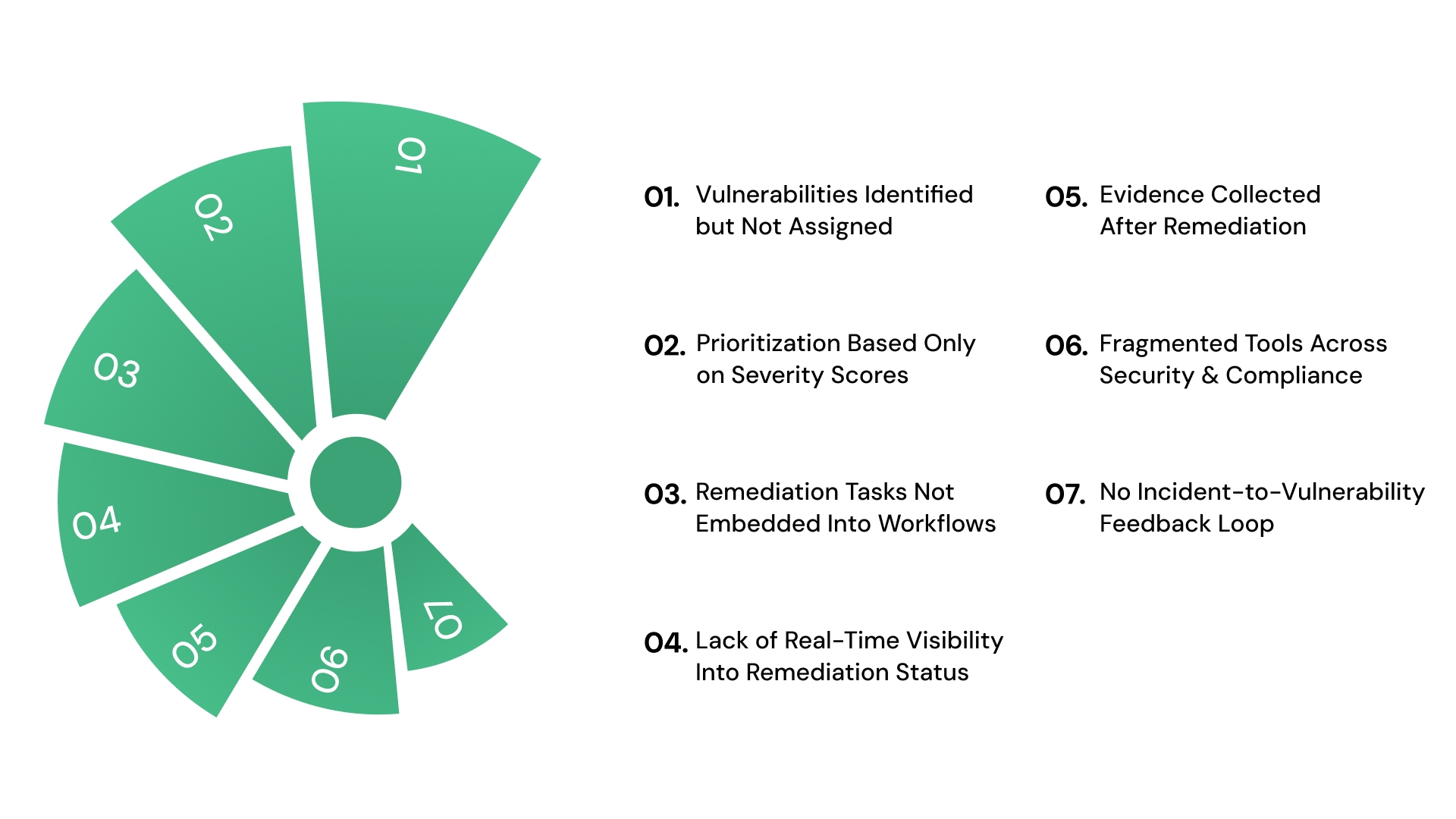
Execution gaps emerge when vulnerability management is not embedded into workflows, ownership structures, and validation mechanisms. These gaps reduce effectiveness and increase audit exposure:
The most critical breakdowns that disrupt execution include:
1. Vulnerabilities Identified but Not Assigned
Scanning tools generate vulnerability data, but ownership is not defined at the execution level. This creates a backlog of unresolved issues where no individual is accountable for remediation timelines or validation outcomes.
Over time, vulnerabilities remain open without visibility into status, increasing exposure and making it difficult to demonstrate accountability during audits.
2. Prioritization Based Only on Severity Scores
Severity scores are often treated as the primary prioritization mechanism, ignoring asset criticality, exposure, and business impact. This results in low-risk vulnerabilities being addressed before high-impact ones.
During audits or incidents, organizations struggle to justify remediation decisions because prioritization lacks alignment with actual risk exposure and operational impact.
3. Remediation Tasks Not Embedded Into Workflows
Remediation activities are tracked outside operational systems, often through emails or standalone tickets. This disconnect prevents consistent execution and creates dependency on manual follow-ups.
Without embedding tasks into workflows, organizations cannot ensure that remediation actions are completed, validated, or tracked across systems.
4. Lack of Real-Time Visibility Into Remediation Status
Vulnerability status is often compiled in periodic reports rather than tracked continuously. This delays detection of unresolved issues and limits leadership visibility into risk exposure.
During audits, organizations cannot present a current view of remediation progress, which weakens confidence in control effectiveness and governance maturity.
5. Evidence Collected After Remediation
Evidence is frequently gathered during audit preparation rather than generated during remediation. This leads to incomplete records, missing timestamps, and inconsistent validation.
Auditors recognize reconstructed evidence patterns quickly, which reduces credibility and raises concerns about whether remediation was executed as documented.
6. Fragmented Tools Across Security and Compliance
Vulnerability data, remediation tracking, and reporting are managed across multiple systems that do not share context. This fragmentation creates inconsistencies in data, delays reconciliation, and limits cross-functional visibility.
As a result, teams operate with partial information, increasing the likelihood of missed vulnerabilities and duplicated efforts.
7. No Feedback Loop From Incidents to Vulnerability Management
Incidents often expose vulnerabilities that were previously identified but not prioritized or resolved. However, these insights are not integrated back into vulnerability workflows.
This prevents organizations from adjusting prioritization models or improving controls, leading to repeated failures and increased risk exposure over time.
Also read: Understanding the Three Lines of Defense Model in Risk Management
Best Practices to Maintain Continuous, Scalable Vulnerability Management
Sustaining vulnerability management requires moving from periodic activity to continuous execution. This means embedding detection, prioritization, remediation, and validation into structured workflows that operate across systems and teams:
Consistency improves when vulnerability management is treated as an ongoing execution system rather than a scanning function:
1. Continuous Monitoring Instead of Periodic Scanning
Scheduled scans create visibility at fixed intervals but leave gaps between assessments where vulnerabilities remain undetected. Continuous monitoring integrates detection into daily operations, allowing organizations to identify and respond to vulnerabilities as they emerge, reducing exposure windows and improving response timelines.
2. Integration Across Risk, Compliance, and Security
Vulnerability management often operates separately from risk and compliance functions, leading to misaligned priorities and reporting. Integrating these functions ensures that vulnerabilities are evaluated within the context of regulatory requirements and business risk, improving decision-making and aligning remediation efforts with governance objectives.
3. Structured Ownership and Accountability
Assigning ownership at a high level does not ensure execution. Each vulnerability and remediation task must have a clearly defined owner responsible for completion and validation. Structured accountability ensures that vulnerabilities are addressed within defined timelines and that delays are escalated appropriately across teams.
4. Automated Evidence Generation Within Workflows
Evidence must be generated as part of remediation workflows, including logs, approvals, and validation records. This ensures that every action is traceable and verifiable. Without embedded evidence generation, organizations rely on retrospective documentation, which reduces audit defensibility and increases operational overhead.
5. Feedback Loops for Continuous Improvement
Insights from incidents, failed validations, and audit findings should directly influence vulnerability prioritization and workflow design. Establishing feedback loops ensures that vulnerability management evolves based on execution outcomes, reducing recurring issues and improving long-term effectiveness across systems.
When these gaps persist across tools and teams, it often reflects missing workflow integration. Solutions like VComply help connect vulnerabilities, remediation tasks, and evidence within a unified execution system.
Also read: Operational Risk Management Examples and Strategies
Turning Vulnerability Management Into a Structured GRC Workflow With VComply
Vulnerability management often breaks because detection, remediation, and validation operate across disconnected systems. This fragmentation delays execution, weakens accountability, and reduces visibility into actual risk exposure.
VComply structures vulnerability management by connecting risk, compliance, policy, and incident workflows into a unified system:
- Use ComplianceOps to map vulnerabilities to regulatory controls and track remediation against compliance requirements
- Apply RiskOps to prioritize vulnerabilities based on business impact, exposure, and risk thresholds
- Manage policy alignment and remediation standards through PolicyOps to ensure consistent execution
- Track vulnerabilities as cases using CaseOps, including escalation, investigation, and resolution workflows
- Use the GRCOps Suite to maintain centralized visibility across vulnerabilities, risks, and remediation status
This approach ensures that vulnerability management operates as a continuous, measurable workflow across systems and teams. Book a demo with VComply to evaluate how structured workflows improve remediation execution and audit readiness.
Conclusion
Automated vulnerability management determines how effectively organizations translate detection into remediation, validation, and measurable outcomes. When vulnerabilities are connected to workflows, ownership, and evidence, execution becomes consistent and defensible.
VComply enables organizations to unify vulnerability management with risk, compliance, and incident workflows, improving visibility and accountability across systems.
Start a 21-day free trial of VComply to evaluate how structured systems improve vulnerability management execution and audit readiness.
FAQs
Automated vulnerability management connects scanning tools with remediation workflows, ownership, and validation. It ensures vulnerabilities are not only detected but also assigned, resolved, and verified within defined timelines and supported by audit-ready evidence.
Failures occur when detection is not linked to workflows, ownership is unclear, and evidence is not generated during execution. These gaps create inconsistencies between identified vulnerabilities and actual remediation outcomes.
Prioritization should combine severity scores with asset criticality, exposure, and threat intelligence. This ensures that remediation focuses on actual business risk instead of generic scoring models.
Key metrics include remediation timelines, validation success rates, exception trends, and evidence completeness. These indicators provide insight into whether vulnerabilities are addressed consistently and can be validated during audits.
Organizations can map vulnerabilities to controls and regulatory requirements, ensuring that remediation supports compliance objectives. Platforms like VComply help integrate these workflows into a unified system.
Vulnerability management should be monitored continuously with periodic reviews based on risk changes, incidents, and regulatory updates. Continuous validation ensures alignment with evolving threats and operational conditions.

