Understanding SOC Compliance: Key Concepts and Benefits
Your credibility as a trusted service provider relies on proving trust, not just uptime or features. Yet in the daily rush of meetings, releases, and incidents, teams often fear the impact of compliance audits on productivity and reputation.

According to a 2025 compliance benchmark report, 92% of organizations underwent at least two audits last year, and over half conducted four or more, showing that audit fatigue is now the norm, not the exception.
For those managing compliance, risk, or security, audits are more than a checklist; they test your reputation with real business impact. In this blog, we will break down what SOC compliance is, why it matters, and how to approach it strategically.
Key Takeaways
- SOC compliance validates internal controls for security, privacy, and operational reliability, reinforcing stakeholder confidence.
- Selecting Type I or II ensures your compliance approach aligns with business needs and customer expectations.
- Scoping controls and mapping evidence minimizes disruption and maintains continuous readiness.
- Using platforms like VComply accelerates sales, enhances credibility with enterprise buyers, and streamlines vendor risk assessments.
- Ongoing compliance strengthens governance, operational discipline, and reduces audit fatigue.
Did You Know?
A recent survey of cybersecurity and risk professionals found that 77% of organizations require SOC 2 compliance as a key control in vendor evaluations, making it central to third‑party risk management and business trust decisions. This shows that SOC compliance is more than a back‑office checkbox; it’s a critical factor in procurement and vendor selection as organizations strengthen security and third‑party risk controls.
What Is SOC Compliance and Why Does It Matter for Regulated Industries
SOC compliance is a formal assurance process that validates how well an organization designs, implements, and operates controls to protect information systems and sensitive data. Defined by the AICPA’s SOC framework, it results in an independent auditor report confirming that controls meet established standards.
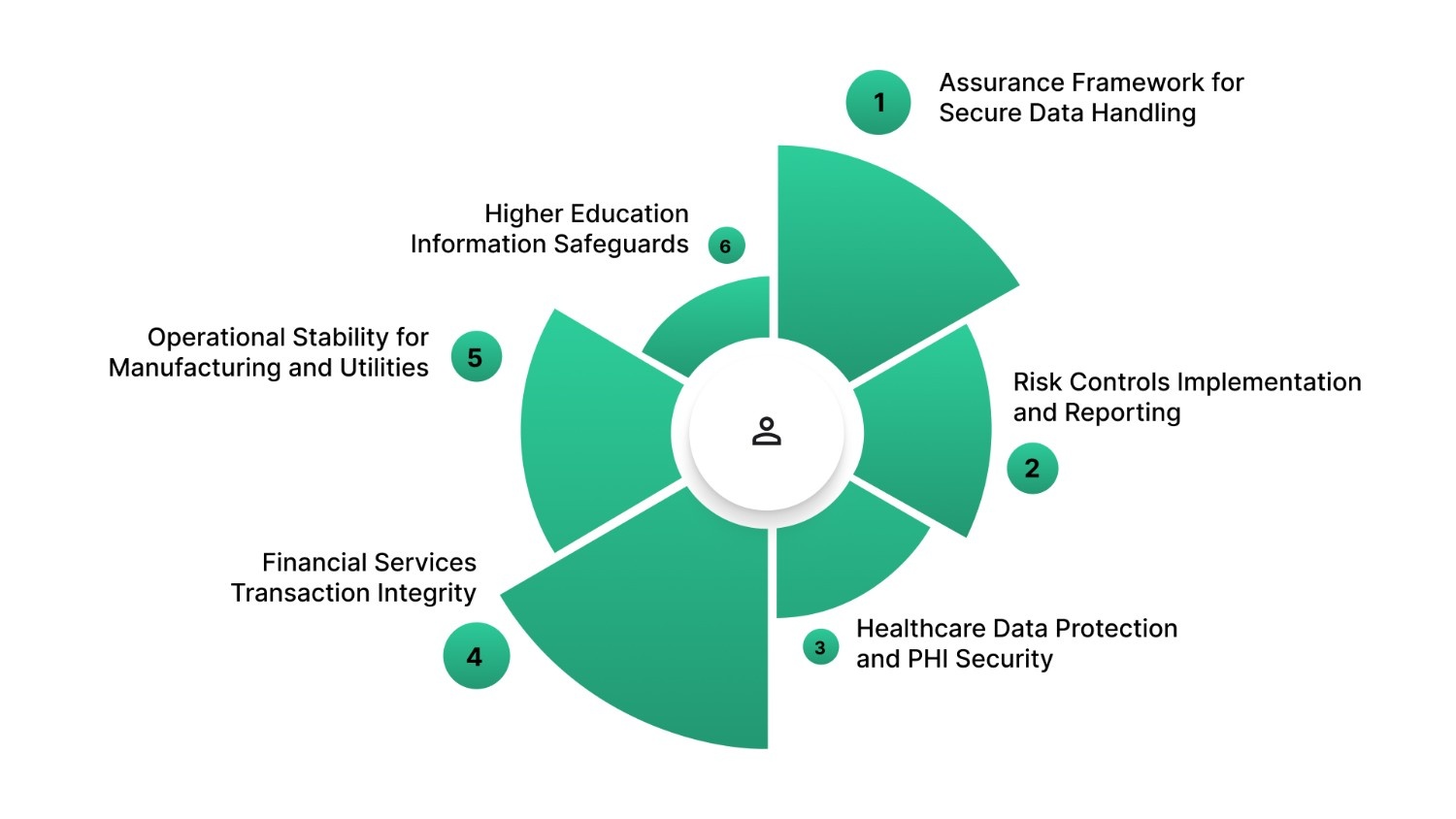
Below are key aspects that explain strong SOC compliance relevance across highly regulated sectors:
- Assurance Framework for Secure Data Handling: SOC compliance verifies that controls align with recognized trust principles, giving stakeholders confidence in data protection.
- Risk Controls Implementation and Reporting: Demonstrates that internal controls are properly designed and reliably mitigate risks in security, availability, processing integrity, confidentiality, and privacy.
- Healthcare Data Protection and PHI Security: Protects patient health information (PHI) and ensures safeguards meet regulatory and industry standards.
- Financial Services Transaction Integrity: Confirms systems handling financial data are secure and maintain accuracy, completeness, and reliability.
- Operational Stability for Manufacturing and Utilities: Enhances operational stability and resiliency for complex, interconnected systems.
- Higher Education Information Safeguards: Ensures sensitive student and research data are safeguarded across IT and administrative functions.
Also Read: Choosing Compliance Management Solutions for Financial Services
Once you grasp the significance of SOC compliance, the next step is implementing practical practices to manage it efficiently and maintain audit readiness.
6 Practical Ways to Improve Compliance Management for SOC Readiness
Improving compliance management is not a one-time task but a structured, ongoing operational discipline that accelerates audit readiness and enhances your team’s productivity.
Below are six evidence-based practices that help transform chaotic, manual compliance workflows into a predictable, scalable operating model.
- Centralize Documentation: Store all controls, policies, and evidence in a unified repository with version control and approval workflows to prevent gaps and ensure auditor access.
- Assign Ownership: Designate a single owner for each control and evidence stream to enhance accountability and streamline coordination.
- Standardize Evidence Collection: Use consistent templates and naming conventions so auditors can verify compliance efficiently, reducing rework and stress.
- Align Controls with Operations: Embed controls into daily workflows to ensure documentation reflects actual practices.
- Automate Reminders: Use automated alerts for reviews, evidence updates, and control tests to minimize errors and missed checkpoints.
- Monitor Continuously: Understand dashboards and real-time monitoring to detect deviations or gaps early, enabling proactive correction before audits.
Implementing Strong compliance practices naturally builds understanding of the SOC audit and the attestation process that validates your controls.
What a SOC Audit Is and How the Attestation Process Works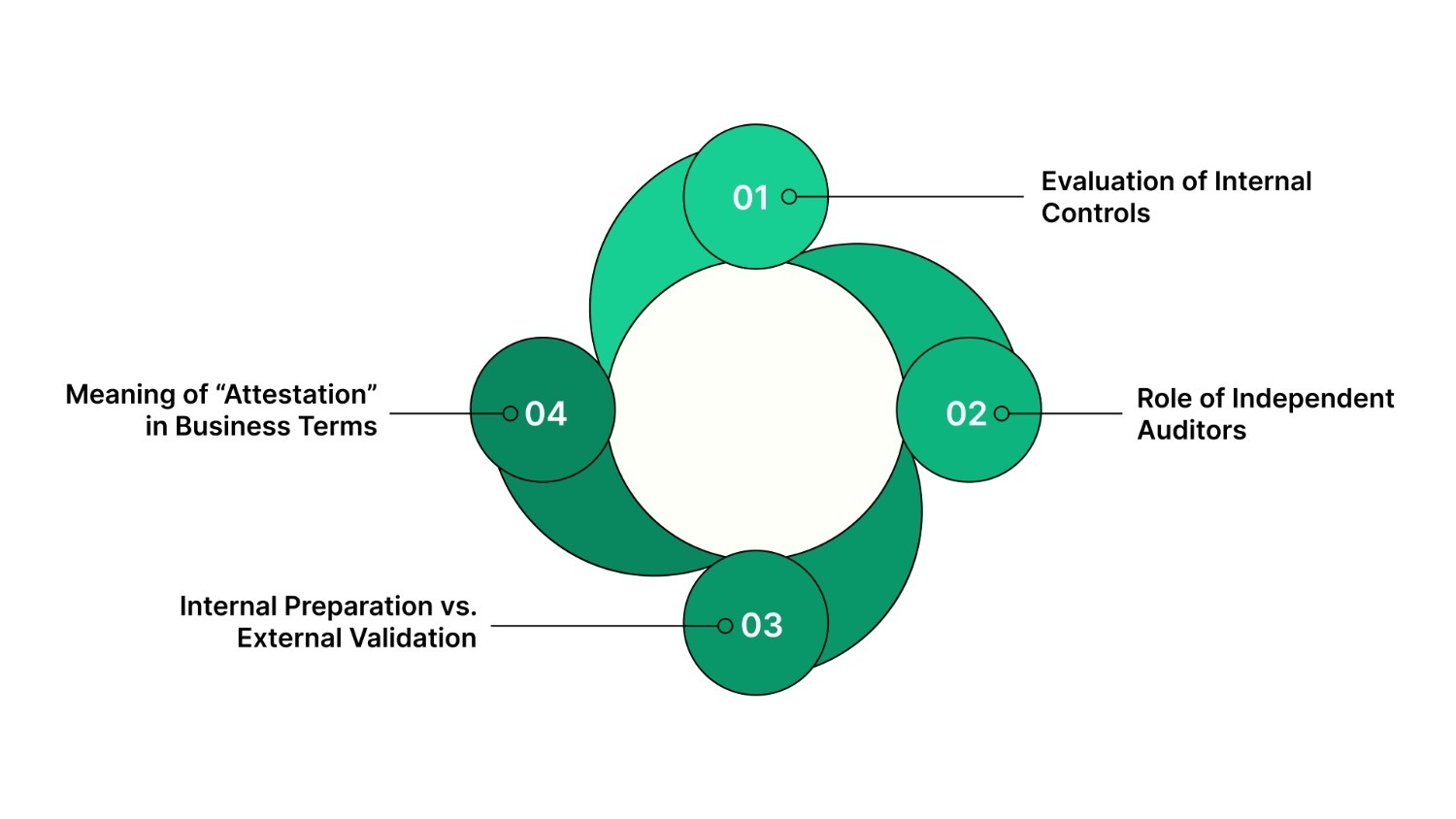
A SOC audit is an independent review of internal controls over security, availability, processing integrity, confidentiality, and privacy. Conducted by a licensed CPA firm, it produces an attestation report verifying compliance with the AICPA Trust Services Criteria.
Below is a clear breakdown of the SOC audit and attestation process:
- Evaluation of Internal Controls: Auditors assess whether controls are properly designed and, for Type II audits, whether they operate effectively over time.
- Role of Independent Auditors: The audit must be conducted by a licensed Certified Public Accountant (CPA) or CPA firm that is independent from your organization, ensuring objective evaluation and credibility.
- Internal Preparation vs. External Validation: Your team prepares documentation and evidence, while auditors independently verify control effectiveness.
- Meaning of “Attestation” in Business Terms: The auditor formally confirms that controls meet criteria based on collected evidence. It is an assurance opinion, not a certification or pass/fail result.
Understanding the audit process sets the stage for selecting the SOC report type that aligns with your business goals and stakeholder expectations.
SOC Report Types Explained: Choosing the Right One for Your Business
When planning your SOC compliance journey, it’s essential to understand how the different SOC reports serve distinct assurance needs. Choosing the correct type ensures you meet stakeholder expectations without unnecessary effort or cost.
Below is a concise overview of the core SOC report categories and their most relevant use cases:
SOC 1 – Financial Reporting Assurance
SOC 1 reports focus specifically on internal controls relevant to financial reporting, particularly if your service affects how customers’ financial statements are prepared or audited. This is especially important for vendors involved in payroll processing, billing systems, or other financial operations.
SOC 2 – Data Security and Operational Controls
SOC 2 reports evaluate controls tied to the Trust Services Criteria, including security, availability, processing integrity, confidentiality, and privacy, and are most relevant for technology and service organizations handling sensitive customer data. These reports provide more comprehensive assurance to customers.
SOC 3 – Public Trust and Marketing Assurance
SOC 3 reports cover much of the same Trust Services Criteria as SOC 2 but are designed for public distribution, omitting detailed audit evidence. They’re useful when you want to showcase compliance broadly, such as on websites or marketing materials, without sharing confidential audit data.
Managing SOC readiness often breaks down at the execution layer: missed evidence, unclear ownership, and last-minute scrambles. VComply’s ComplianceOps helps teams assign control ownership, centralize evidence, and automate review cycles so SOC readiness becomes part of daily operations instead of an audit-season fire drill.
Also Read: Understanding Regulatory Compliance Management in the U.S.
After identifying the right SOC report type, it’s crucial to determine whether a Type I or Type II audit best meets your operational needs and assurance goals.
SOC Type I vs. Type II Reports: Scope, Evidence, and Timelines
Choosing between a Type I and Type II SOC report is one of the most critical decisions in your organization’s audit journey, especially for first-time audits or when planning a long-term compliance strategy.
Below is a distinction that affects how much assurance you can provide to customers, how auditors evaluate your controls, and how much time and effort your teams must invest.
Type I – Snapshot Assessment Of Control Design
SOC Type I evaluates whether controls are properly designed and implemented at a specific point. Auditors verify that policies, procedures, and safeguards exist, but don’t assess ongoing operation. Ideal for early-stage teams, audits and reporting can typically be completed within weeks.
Type II – Continuous Evaluation Of Operational Effectiveness
SOC Type II assesses whether controls operate effectively over time (typically 3–12 months). Auditors collect evidence throughout the period to ensure consistent performance, offering stronger stakeholder assurance. Its extended scope requires thorough preparation and ongoing coordination.
Typical Timelines And Effort
- Type I: Shorter timeframe, often completed within a few weeks to months after readiness is achieved, requiring primary focus on documentation and design evidence.
- Type II: Requires a defined observation period (commonly 6–12 months) before auditors begin fieldwork, making the overall timeline significantly longer and more resource-intensive.
When To Consider Moving From Type I To Type II
Organizations use Type I for early compliance or quick assurance. Once controls are mature and enterprise clients require sustained evidence, Type II provides the highest assurance and credibility.
Whichever report type you choose, your SOC compliance journey is grounded in the Trust Services Criteria that define what auditors evaluate.
Trust Services Criteria That Define SOC Compliance Scope
In a SOC audit, auditors don’t just review tools or policies; they assess whether controls meet the Trust Services Criteria, which define what to protect and how, ensuring alignment with business commitments and stakeholder expectations.
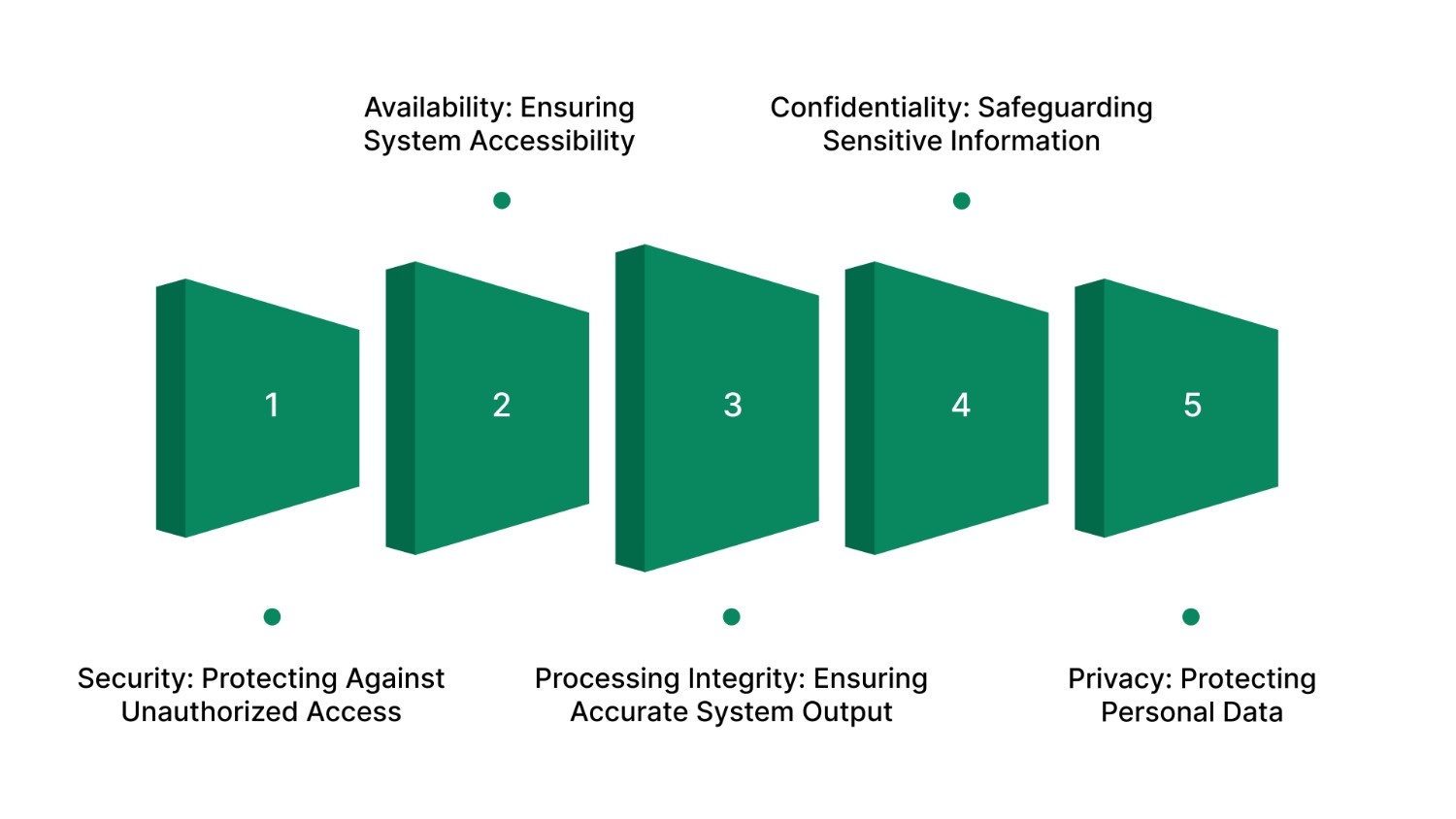
Below are the five criteria auditors use to assess compliance during a SOC 2 engagement:
- Security: Protecting Against Unauthorized Access: Protect systems and data from unauthorized access, misuse, or damage to maintain availability, integrity, confidentiality, and privacy.
- Availability: Ensuring System Accessibility: Ensure systems and services remain accessible as promised in SLAs, including disaster recovery and uptime commitments.
- Processing Integrity: Ensuring Accurate System Output: Verify data is processed completely, accurately, and in a timely manner, and with proper authorization, critical for transaction-heavy or real-time services.
- Confidentiality: Safeguarding Sensitive Information: Protect sensitive information, such as proprietary business data, throughout its lifecycle.
- Privacy: Protecting Personal Data: Handle personally identifiable information (PII) in line with privacy commitments and legal requirements from collection to disposal.
SOC compliance ultimately fails when risks stay invisible until audit time. VComply’s RiskOps connects Trust Services Criteria directly to enterprise risks. This helps teams identify control gaps early, assess impact, and track remediation before issues turn into audit findings or customer escalations.
Knowing the criteria behind SOC compliance helps clarify who benefits from SOC reports and how your organization can understand them strategically.
Who Needs SOC Compliance and Why
SOC reports serve a clear business purpose: they provide independent assurance that an organization’s internal controls are properly designed and effective. Rather than existing for auditors alone, they help stakeholders evaluate risk, security, and operational reliability in a standardized, credible way.
Organizations That Benefit Most From SOC Compliance
- Customers and Prospects: SOC reports give buyers confidence that your systems and processes meet established security and operational standards, reducing friction during vendor evaluation and onboarding.
- Procurement and Vendor Risk Teams: Instead of lengthy questionnaires or custom audits, SOC reports offer a consistent, third-party validated view of controls, streamlining due diligence and risk assessments.
- Internal Leadership and Boards: Executives and boards use SOC reports to understand control effectiveness, assess operational risk, and ensure accountability across technology and business functions.
When SOC Compliance Becomes Essential
SOC compliance is typically required, or strongly expected, when one or more of the following conditions apply:
- Selling to Enterprise or Regulated Customers: Organizations in finance, healthcare, higher education, energy utilities, and other regulated sectors often require SOC reports before contract approval or renewal.
- Handling Sensitive or Regulated Data: Companies processing personally identifiable information (PII), protected health information (PHI), or financial data must demonstrate that controls align with recognized standards.
- Expanding Into New Markets or Industries: Entering regulated or security-sensitive industries increases scrutiny from customers, partners, and regulators, making SOC compliance a competitive necessity.
- Supporting Internal Governance and Risk Management: Even without external pressure, SOC audits help organizations formalize controls, improve operational discipline, and maintain audit readiness assessment as they scale.
Also Read: Top 10 Real Estate Compliance Management Software in Dubai for 2025
Once you’ve identified the need for SOC compliance, effective preparation ensures audits integrate smoothly into daily operations without unnecessary disruption.
How to Prepare for a SOC Audit Without Disrupting Operations
SOC audit preparation doesn’t have to disrupt operations. Structured planning, organized evidence collection, and clear control scoping let you integrate readiness into daily processes, improving control quality while minimizing business disruption.
Below are key steps that help you prepare efficiently and confidently:
- Define and Scope Controls: Identify in-scope systems, processes, and Trust Services Criteria to focus audit efforts and avoid unnecessary work.
- Map Controls to Evidence: Link each control to specific, verifiable evidence, logs, policies, change histories, or review records, to simplify auditor verification.
- Centralize Documentation: Use a compliance repository instead of spreadsheets to manage versioning, access, and traceability, reducing errors and manual reconciliation.
- Adopt Continuous Readiness: Treat audit prep as ongoing with automated data collection, periodic mock assessments, and regular control updates.
- Engage Stakeholders Early: Involve control owners, IT, and operations teams early so evidence collection fits naturally into daily workflows.
Now, let’s explore some challenges that must be addressed to maintain efficiency and readiness.
Common SOC Compliance Challenges Organizations Face
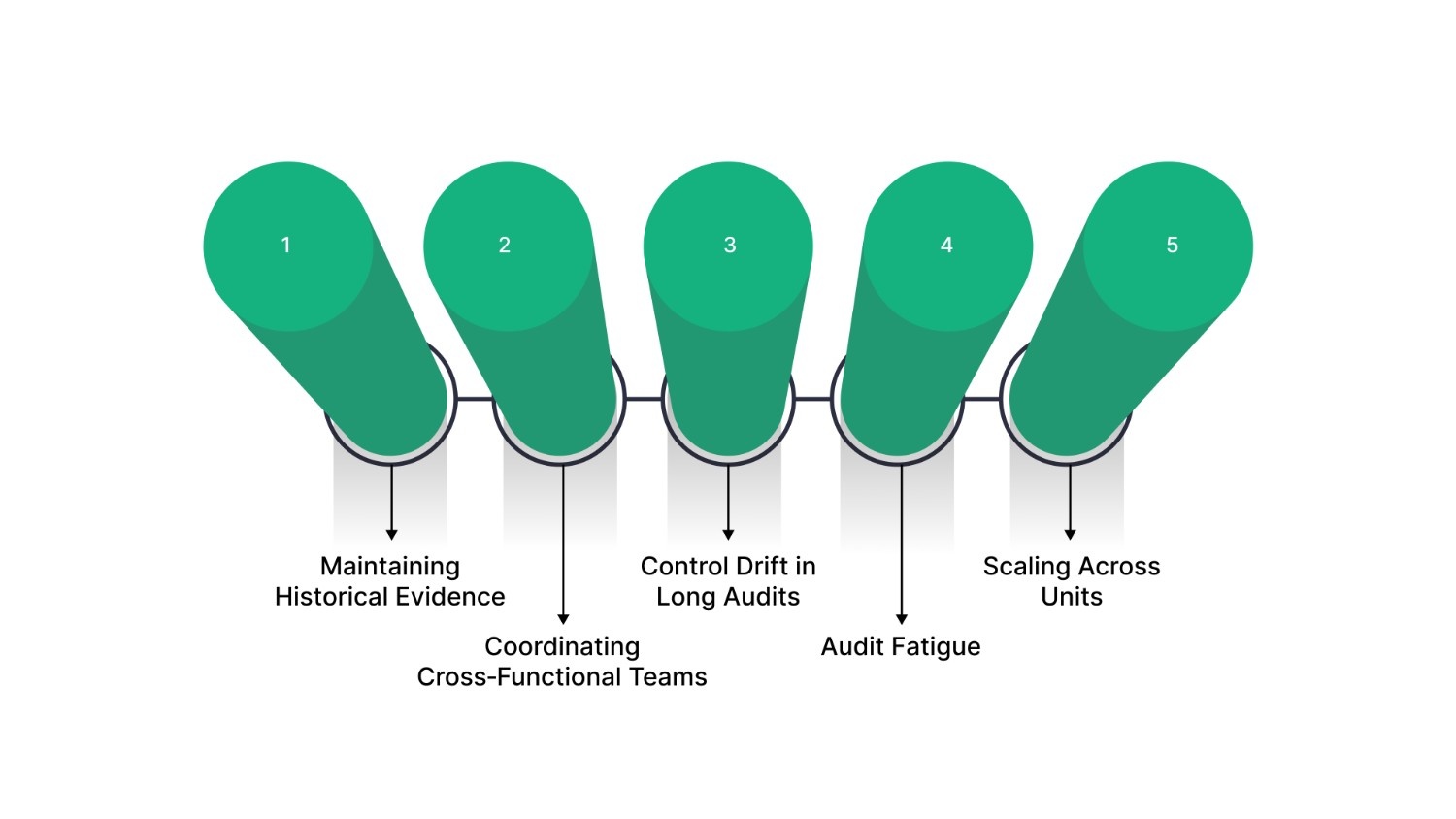
Even strong SOC compliance efforts face challenges that can reduce efficiency, strain teams, and delay audit readiness. Knowing these hurdles helps prevent operational or stakeholder disruptions.
Below are the key obstacles many organizations face in managing SOC compliance, along with the operational impacts they create.
- Maintaining Historical Evidence: SOC audits require continuous control evidence (logs, reviews, change records). Manual or scattered documentation often leads to gaps.
- Coordinating Cross‑Functional Teams: IT, security, HR, and operations must collaborate. Without clear roles, evidence collection stalls and audits are delayed.
- Control Drift in Long Audits: Over extended periods, controls may not be applied consistently. Lack of monitoring creates gaps between documented policies and actual operations.
- Audit Fatigue: Repetitive evidence requests and manual processes cause burnout, diverting teams from core priorities.
- Scaling Across Units: As organizations grow, maintaining consistent compliance across functions, regions, and systems becomes complex.
Effectively addressing these challenges requires tools that embed SOC compliance into daily operations; solutions like VComply are invaluable for this.
How VComply Helps Organizations Operationalize SOC Compliance
VComply is a unified Governance, Risk & Compliance (GRC) platform that helps compliance officers, risk managers, CTOs, and executives operationalize SOC compliance. It embeds readiness into daily operations, providing a single source of truth for controls, evidence, risk insights, and audits.
Below is how VComply can help your organization operationalize SOC compliance:
- ComplianceOps for SOC: Centralizes controls, tasks, and ownership on a dashboard with automated reminders and alerts, keeping controls audit-ready and reducing manual follow-ups.
- Centralized Evidence Management: Store, organize, and retrieve versioned, linked evidence in one repository for quick, accurate auditor verification.
- Scalable GRC Across Industries: Supports healthcare, finance, manufacturing, energy, and higher education with frameworks, customizable controls, and reporting that grow with your business.
- Integrated Compliance, Risk, Policy, and Audit: Beyond SOC readiness, VComply unifies ComplianceOps, RiskOps, PolicyOps, and CaseOps, improving visibility, reducing tool switching, and streamlining governance.
Streamline your SOC compliance and scale your GRC program. Book a VComply demo to see how its centralized, automated platform supports compliance, risk, and audit readiness.
Final Thoughts
SOC compliance goes beyond audits; it drives operational excellence, resilience, and trust. It embeds security controls, streamlines risk management, and strengthens governance and discipline, reducing disruption and supporting sustainable growth and competitive advantage.
VComply provides compliance officers, risk managers, CTOs, and CEOs with a unified GRC platform that centralizes controls, automates evidence collection, and scales across industries. Dashboards, calendars, task tracking, and audit support reduce manual work, improve accountability, and maintain continuous readiness.
Simplify your SOC compliance and build a resilient, audit-ready program. Start your 21-day free trial of VComply today to see how centralized compliance management transforms risk and audit workflows.
FAQs
A SOC 2 readiness assessment helps you evaluate your current controls, documentation, and security posture before an audit. It identifies gaps, risks, and missing controls so you can remediate issues early, streamline audit preparation, and avoid last‑minute findings. It’s a key step in planning your SOC 2 journey.
SOC 2 reports typically cover a 12‑month period, so annual audits are common to maintain up‑to‑date assurance. Some organizations choose more frequent reviews, such as twice yearly, when customers or internal risk teams demand continuous assurance.
SOC audits must be conducted by an independent licensed CPA firm. These auditors assess your control design and operation against trust criteria and issue the final SOC report, providing third‑party assurance that your controls meet established standards.
If there’s a gap between SOC reports and no bridge letter is provided, customers may question your compliance continuity. While bridge letters aren’t mandatory, they help maintain trust for short periods before your next audit report is released.
No. A bridge letter fills a short gap between audit reports and represents management’s assertion that controls haven’t materially changed, but it cannot substitute for the comprehensive, independently verified attestation of a full SOC audit.

