Five Steps of the Risk Management Process
What if one overlooked risk could derail months of hard work and compliance efforts?
From shifting regulations and cyber threats to operational disruptions, risks are evolving faster across industries such as finance, healthcare, and manufacturing.

A single oversight can lead to costly compliance failures, financial losses, or reputational damage. Many risk and compliance managers struggle to implement a structured approach that maintains secure and compliant operations.
If you are also struggling to implement a structured approach, this blog explores the five essential steps of the risk management process, helping you build a proactive strategy that strengthens resilience, ensures regulatory adherence, and drives smarter decision-making.
Key Takeaways
- A structured risk management process enables organizations to identify, assess, respond, mitigate, and monitor risks that impact their operations and compliance.
- Clear risk identification and analysis ensure you understand likelihood, impact, and priority before taking action.
- Response planning outlines the specific steps, responsibilities, and timelines required to address each risk effectively.
- Mitigation strategies include avoidance, transfer, sharing, acceptance, and buffering to reduce exposure and strengthen resilience.
- Continuous monitoring, supported by KRIs and control testing, is essential to catch emerging risks early and maintain long-term stability.
What is the Risk Management Process?
The risk management process is a structured sequence of activities your organization uses to identify potential threats, assess their likelihood and impact, and apply appropriate controls to mitigate them. It enables you to protect the business from operational failures or regulatory lapses while staying aligned with strategic objectives.
For risk and compliance managers, this process serves as a roadmap for turning uncertainty into manageable outcomes. By embedding this methodology into your daily operations, you ensure your organization is not just reacting to risk but actively controlling it.
Now that you understand what the risk management process involves, let’s explore why it’s so critical to organizational success.
Also Read: Improving Your Risk Assessment Process: Practical Steps and Tools
Why is Risk Management Important?

Effective risk management is critical for ensuring your organization can withstand unexpected threats and regulatory pressures while driving sustainable growth. Without it, compliance gaps, operational failures, and reputational damage can quickly spiral.
Here are five key reasons why a structured risk management process matters:
- Protects reputation and trust: In sectors such as healthcare, finance, and manufacturing, a single risk event can erode stakeholder confidence. Proactive risk management helps you maintain credibility.
- Minimizes financial and operational losses: From regulatory fines to business interruptions or supply‑chain breakdowns, unmanaged risks have real costs. A robust process helps you identify and mitigate these before they hit.
- Enhances decision‑making: With a clear view of your risk, you can make more informed strategic choices and allocate resources where they matter most.
- Supports compliance and audit readiness: For compliance managers and risk officers, aligning risk management with regulatory frameworks ensures you meet audit demands and avoid compliance breakdowns.
- Drives resilience and growth: Rather than simply reacting to threats, organizations that embed risk management into their operations position themselves for innovation and long-term success, even in volatile environments.
With the importance of risk management clear, the next step is to break down the core stages that make it effective.
What Are the Steps of Risk Management?

The risk management process is a structured approach that helps organizations handle uncertainty, protect assets, and maintain compliance. It provides a clear framework for identifying, evaluating, and addressing risks across departments.
Here are the five essential steps involved in an effective risk management process:
1. Risk Identification
Risk identification involves recognizing and documenting all potential threats, both current and emerging, that could affect your organization’s objectives, operations, or compliance posture. Here are some of the most common types of risks organizations may face:
- Regulatory & Compliance Risks: Risks arising from changing regulations, non-compliance with standards like SOX, HIPAA, PCI-DSS, FDA mandates, or accreditation requirements in higher education and healthcare.
- Operational Risks: Process failures, human errors, system outages, or workflow breakdowns that disrupt service delivery, manufacturing, or daily business operations.
- Cybersecurity & Data Privacy Risks: Threats such as phishing, insider misuse, or unauthorized access that can compromise sensitive customer, patient, or financial data.
- Financial & Credit Risks: Revenue volatility, inaccurate reporting, fraudulent activities, or credit defaults impacting financial stability.
- Strategic Risks: Poor business decisions, market shifts, competitive pressures, or failed expansions that impact long-term goals.
- Third-Party & Supply Chain Risks: Vendor non-compliance, delays, product quality issues, or dependency on single-source suppliers.
- Health, Safety & Environmental Risks: Workplace incidents, equipment failure, contamination, or environmental hazards are especially relevant in energy, manufacturing, and food & beverage sectors.
- Reputational Risks: Negative publicity, customer dissatisfaction, product failures, or ethical issues that damage trust.
A robust identification process ensures that you don’t miss critical threats, such as regulatory changes, cyber vulnerabilities, safety hazards, or operational breakdowns. By looking beyond today’s risks and anticipating those that may arise in the future, organizations build a more resilient and forward-looking risk framework.
With VComply RiskOps, organizations can centralize all risks in a unified risk register, categorize them accurately, and assign ownership with ease. We ensure that no risks are overlooked, providing risk managers with complete visibility into emerging threats across all departments.
2. Risk Analysis
Once risks are identified, the next step is to analyze their likelihood of occurrence and the potential impact they could have on your organization. This helps you clearly understand your level of exposure and the potential financial, operational, or regulatory consequences if the risk becomes real.
Organizations typically classify risks using categories such as high, medium, or low, or serious, moderate, or minor. The exact labels aren’t as important as using a consistent and repeatable method to determine which risks need immediate attention.
During risk analysis, organizations often evaluate:
- Likelihood: How probable is it that the risk will occur?
- Impact: How severe would the consequences be if it happened?
- Velocity: How quickly the risk could affect the business once triggered.
- Existing controls: Are current safeguards strong enough to reduce the risk?
- Residual risk: The level of risk that remains after applying controls.
For example, a risk with high impact but very low likelihood may not need the same urgent focus as a high-likelihood, high-impact threat that could disrupt operations, affect customers, or result in compliance failures.
Effective risk analysis ensures your limited time, budget, and resources are directed toward the most critical and high-priority risks.
3. Response Planning
Response planning answers a simple but important question: What should we do about each risk? In this step, you develop practical strategies that align with your organization’s risk appetite, resources, and day-to-day operations.
For example, if your risk analysis shows that employees are vulnerable to phishing attacks, your response plan might include:
- Security awareness training to help employees identify suspicious emails.
- Simulated phishing tests to measure improvement over time.
- Stronger access controls to limit unauthorized entry into systems.
A strong response plan should clearly outline:
- What actions will be taken?
- Who is responsible for each action/
- When must the actions be completed?
- What outcomes or improvements are expected?
This level of clarity ensures accountability across teams and helps everyone understand exactly how the organization plans to reduce or address each risk.
4. Risk Mitigation
Risk mitigation is the stage at which you implement your response plan. This is where policies, procedures, and controls are implemented to reduce the likelihood or impact of the risks you’ve identified. It turns your strategy into concrete steps that protect your organization.
For example, if phishing is a major risk, mitigation may include:
- Providing ongoing employee training.
- Updating onboarding materials with security best practices.
- Enforcing multi-factor authentication.
- Deploying email filtering and anti-phishing tools.
All controls should be tested regularly to ensure they are properly designed and functioning as expected.
Top Five Strategies for Risk Mitigation
Organizations use different strategies to address risks based on their likelihood, impact, and business priorities. Choosing the right approach helps reduce exposure while supporting operational stability.
1. Risk Avoidance
Risk avoidance means completely eliminating the activity, process, or situation that creates the risk. Instead of trying to manage it, the organization chooses not to engage in that activity at all. This is typically used when the potential harm outweighs the benefit.
2. Risk Transfer
Risk transfer shifts the financial or operational impact of a risk to a third party. This is often done through insurance, outsourcing, or vendor contracts that clearly define liability. The risk still exists, but another party is responsible for handling its consequences.
3. Risk Sharing
Risk sharing means distributing a risk across multiple parties, such as partners, suppliers, or business units. Each party absorbs a portion of the risk, reducing the impact on any single organization. This strategy is common in joint ventures, collaborations, and shared service models.
4. Risk Acceptance
Risk acceptance means the organization acknowledges a risk and refrains from taking further action to mitigate it. This typically happens when the risk is unlikely to occur or its impact is too minor to disrupt operations.
In these cases, the cost or effort required to mitigate the risk outweighs the potential benefit, so the organization decides to monitor it rather than invest in additional controls.
5. Risk Buffering
Risk buffering is a strategy that involves creating extra capacity or reserves, such as time, money, or operational resources, to absorb the impact of unexpected events. It strengthens an organization’s ability to adapt and respond to disruptions without significant downtime or loss.
This may include maintaining financial reserves, backup systems, additional project time, or excess production capacity that goes beyond normal operating needs. These resources act as a protective cushion when adverse events occur.
5. Risk Monitoring
Risk monitoring involves regularly checking your risks to ensure that nothing new or unexpected is developing. As regulations change, systems are updated, and new threats emerge, ongoing monitoring enables you to identify problems early before they escalate into serious issues.
Regular reviews, control testing, and updates to your risk register help you identify which risks are worsening or which new ones are emerging. A small risk can quickly escalate into a significant issue, particularly in industries such as finance or healthcare.
Simple activities that support effective risk monitoring:
- Review risks regularly to see if the likelihood or impact has changed.
- Test the controls to ensure they still function properly.
- Track warning signs using Key Risk Indicators (KRIs).
- Update the risk register whenever there is a change.
- Check vendor and third-party performance.
- Stay informed about new regulations and requirements.
Monitoring is not something you do once. It is a continuous process that helps your organization stay safe, compliant, and prepared for the future.
While following these steps is essential, it’s equally important to be aware of common pitfalls that can weaken your risk management efforts.
Common Mistakes During the Risk Management Process
Even experienced risk and compliance managers can encounter challenges when establishing or maintaining a risk management program. Small gaps such as missing data, unclear ownership, or outdated controls can lead to larger problems, including compliance failures, operational delays, or unexpected losses.
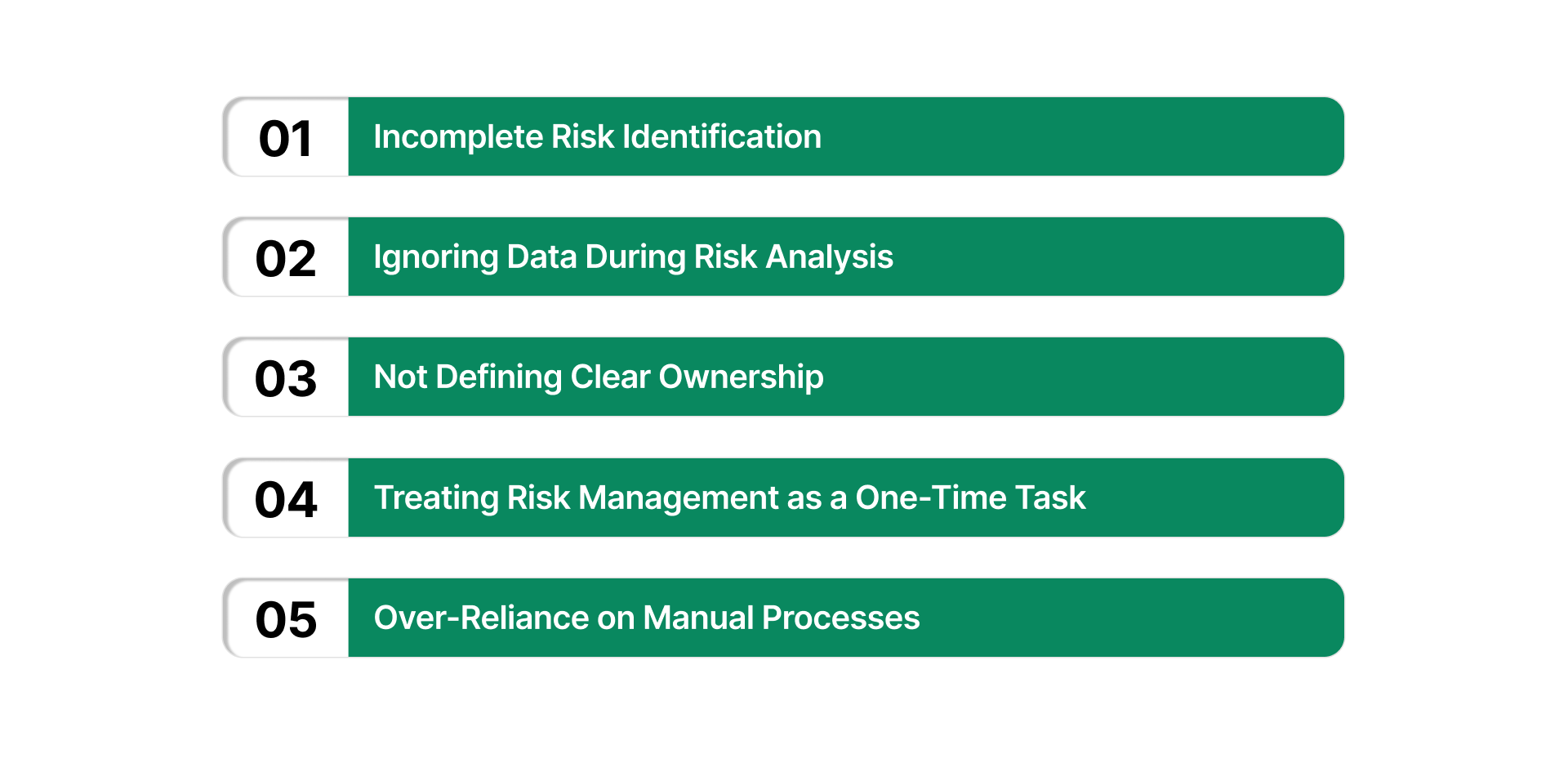
Understanding these pitfalls enables organizations to create a stronger, more reliable risk management process. Here are five common mistakes to watch out for:
- Incomplete Risk Identification: Many organizations focus only on obvious risks and overlook emerging, operational, or third-party risks. This creates blind spots that can lead to compliance issues or unexpected disruptions, especially in industries with complex regulations.
- Ignoring Data During Risk Analysis: Risk decisions made without accurate data often lead to incorrect scoring or poor prioritization. Failing to use incident reports, audit findings, KRIs, or vendor assessments can weaken your entire risk program.
- Not Defining Clear Ownership: When no one is assigned to monitor or manage a risk, actions get delayed or missed entirely. Clear ownership ensures accountability and facilitates the tracking of progress on mitigation or control activities.
- Treating Risk Management as a One-Time Task: Some organizations only assess risks during audits or annual reviews. But risks change constantly, new technologies, updated regulations, and evolving threats all require ongoing monitoring.
- Over-Reliance on Manual Processes: Using spreadsheets, emails, or disconnected tools leads to errors, missed deadlines, and outdated information. Manual tracking also makes it more challenging for risk and compliance teams to maintain alignment across departments.
To overcome these common challenges and simplify the risk management process, many organizations are turning to purpose-built platforms.
Also Read: Taking Control of Risk – Essential Risk Mitigation Strategies
How VComply Helps in the Risk Management Process
VComply is a cloud-based Governance, Risk, and Compliance (GRC) platform that helps organizations across industries, including financial services, healthcare, higher education, non-profits, food & beverages, energy, and manufacturing, streamline and automate the risk management processes.
RiskOps provides a centralized and collaborative environment to manage the entire risk lifecycle. From risk identification to ongoing monitoring, it strengthens workflows, establishes clear ownership, and delivers real-time visibility, helping teams respond to risks with confidence.
Here’s how RiskOps supports the risk management process:
- Risk Register: Centralizes all risks in one place, providing organizations with a clear and comprehensive view of their operational and business risk landscape.
- Risk Settings: Enables organizations to define their risk appetite by category, allowing them to tailor strategies to their specific risk profile and strategic goals.
- Automated Assessments: Automates inherent and residual risk assessments using predefined workflows, alerts, and response criteria to ensure consistent and timely evaluations.
- Risk Control Matrix: Displays strategic reports that show each risk and its associated controls, helping teams understand control effectiveness and identify areas that need improvement.
- Dashboards and Reporting: Combines risk and compliance data into a single, visual dashboard with the ability to download reports based on risk appetite, response strategies, and other parameters.
- Escalation Reports: Sends alerts when critical risks require escalation, helping organizations respond quickly and reduce the chance of unmanaged impacts.
Strengthen your risk posture with RiskOps and unify your risk strategy!
Wrapping Up
A structured risk management process enables organizations to proactively identify, assess, respond to, and monitor risks that could impact their operations. These steps, from identification to monitoring, help build resilience, ensure regulatory compliance, and support smarter decision-making across industries such as financial services, healthcare, education, and manufacturing.
To support these steps, VComply offers a powerful, cloud-based risk management platform tailored for compliance and risk managers. With features such as a centralized risk register, automated assessments, customizable dashboards, escalation alerts, and control matrix reporting, we streamline your entire risk management lifecycle.
Ready to level up your risk management strategy? Book a free trial today and explore how VComply can streamline your workflows and improve compliance outcomes!
FAQs
No, risk monitoring is continuous because business environments, systems, and threats are constantly evolving; ongoing review keeps your risk strategy up to date.
Whenever business conditions change, such as the introduction of new technologies, regulatory shifts, supply-chain disruptions, or emerging threats, the treatment strategy should be reviewed and adjusted accordingly.
A risk is a potential future event that may impact objectives, whereas an issue is something that has already occurred and requires resolution.

