Why Most Compliance Checklists Fail and How to Build One That Works
Audit reviews increasingly highlight a consistent gap: organizations can document compliance requirements but struggle to demonstrate how those requirements are executed. Under frameworks such as NIST, HIPAA and GDPR, missing evidence, unclear ownership, and inconsistent checklist execution often surface during audits.

For compliance leaders, the challenge is ensuring that every control is performed and traceable, not just defined.
A compliance checklist sits at the center of this execution layer, translating regulatory obligations into structured, repeatable actions. Its effectiveness determines whether compliance holds under scrutiny or breaks down during review.
This article outlines how to build and operationalize a compliance checklist that supports consistency, accountability, and audit readiness.
An Overview
- A compliance checklist must translate regulatory obligations (e.g., NIST, HIPAA, GDPR) into repeatable, accountable control actions, not static tasks
- Most compliance checklists fail when they remain disconnected from workflows, ownership, and evidence capture
- Effective checklists include defined ownership, execution frequency, evidence requirements, and escalation paths
- Different types, regulatory, audit, and operational, serve distinct purposes but must align within a unified compliance structure
- Building a compliance checklist requires mapping regulations, controls, workflows, evidence for audit defensibility
- Operationalizing a checklist depends on cross-functional execution, real-time visibility, and consistent tracking across teams
- Common gaps include inconsistent execution, lack of traceability, and fragmented tools, which weaken audit readiness
Practical Example
A weak checklist item might say:
Review access permissions quarterly.
A stronger version would say:
Conduct quarterly access review for all users with system admin privileges. The IT owner must export the user access report, review access against approved roles, document exceptions, attach evidence, and submit the review to the compliance manager by the last business day of each quarter.
That version is stronger because it defines:
- What needs to be reviewed
- Who owns it
- When it is due
- What evidence is required
- Who reviews it
- How exceptions are handled
That is the level of clarity compliance teams need.
How to Build a Compliance Checklist That Works
Step 1: Start With the Requirement
Do not begin with tasks. Begin with the actual obligation.
Identify the regulation, policy, standard, contract clause, or internal control that needs to be managed. Then break it into specific, measurable activities.
Step 2: Assign Ownership
Every task should have a named owner or role-based owner.
Avoid vague ownership such as “operations team” or “HR.” Use specific roles wherever possible.
Step 3: Define Evidence
For every checklist item, define what proof is required.
Evidence could include:
- Signed forms
- Reports
- Screenshots
- Inspection photos
- Training records
- Policy acknowledgments
- Meeting minutes
- System logs
- Corrective action records
Step 4: Set Frequency and Deadlines
Some tasks are annual. Others are monthly, quarterly, event-based, or triggered by incidents.
Make the frequency clear so teams know when work needs to happen.
Step 5: Build in Review and Approval
Completion should not always be the final step.
For high-risk activities, add a review layer. This ensures the work was not only completed but checked for quality and accuracy.
Step 6: Track Exceptions
A checklist should show more than what went right.
It should also capture what was missed, delayed, failed, or incomplete. Every exception should lead to a corrective action, owner, and deadline.
Step 7: Centralize Reporting
The checklist should give compliance leaders a clear view of:
- Completed tasks
- Overdue items
- Missing evidence
- Open issues
- High-risk gaps
- Recurring failures
- Audit readiness status
This helps leaders act before problems escalate.
From Checklist Completion to Compliance Confidence
The most mature compliance teams are changing how they think about checklists.
They are not asking only, “Did we complete the checklist?”
They are asking:
“Can we prove the work was done correctly?”
“Can we show ownership?”
“Can we identify where risk is building?”
“Can we repeat this process across the organization?”
“Can we stay ready before the audit begins?”
That is the difference between compliance activity and compliance confidence.
A checklist should not simply help teams prepare for audits. It should help the organization operate with more discipline, visibility, and accountability every day.
How Technology Helps
Spreadsheets may work for small teams or simple tasks. But as compliance programs grow, they become difficult to manage manually.
Compliance software helps teams:
- Automate recurring tasks
- Assign ownership
- Send reminders
- Escalate overdue items
- Attach evidence
- Track corrective actions
- Maintain audit trails
- Generate dashboards and reports
This turns the checklist into a living workflow instead of a static document.
Also read: 11 Best GRC Tools and Platforms to Use in 2025
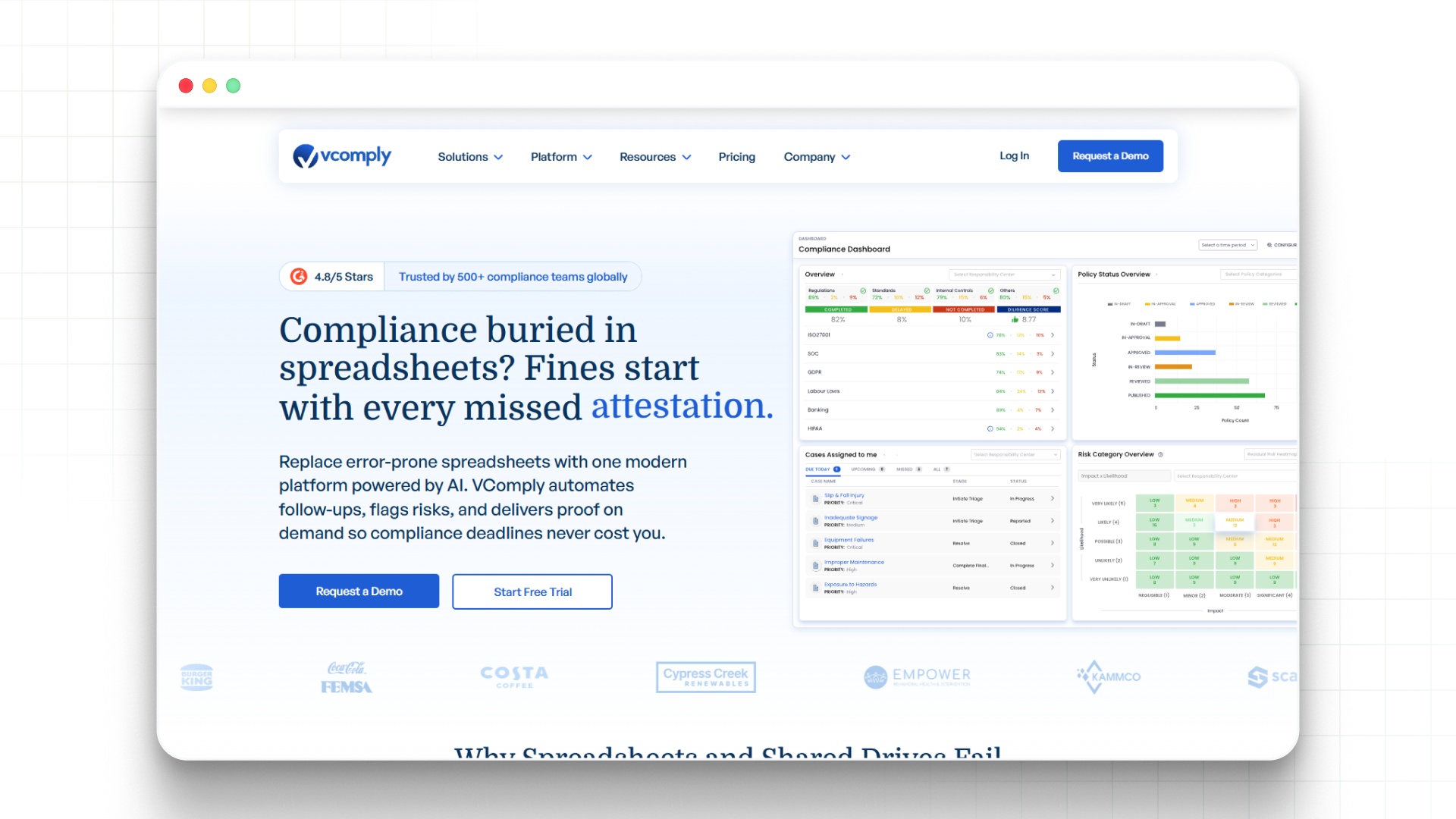
As control execution spans multiple teams and dependencies, maintaining consistency and visibility becomes increasingly complex. Book a demo with VComply to see how workflow-driven systems can help coordinate execution, capture evidence, and reduce breakdowns across control processes.
VComply’s GRCOps Suite structures controls into unified workflows, enabling consistent execution, centralized visibility, and audit-ready evidence.
- Centralized control tracking with defined ownership
- Workflow-driven execution across teams
- Real-time visibility into control performance
- Integrated evidence capture for audits
- Alignment with risk and compliance frameworks
See how structured workflows improve control execution and strengthen governance visibility across your organization. Book a demo with VComply now.
Final Thoughts
Most compliance checklists fail because they are built for tracking, not accountability.
A better checklist connects requirements to owners, deadlines, evidence, reviews, exceptions, and reporting. It helps compliance teams move beyond manual follow-up and gives leadership a clearer view of risk and readiness.
The goal is not to create a longer checklist.
The goal is to create a checklist that helps the organization prove that compliance work is happening, documented, reviewed, and improving over time.
As organizations scale, maintaining this consistency becomes difficult due to fragmented workflows and limited visibility. VComply’s ComplianceOps addresses this by structuring checklist execution within controlled workflows, ensuring accountability and audit-ready evidence.
Start a 21-day free trial of VComply to explore how VComply can help standardize compliance execution and strengthen oversight across your organization.
FAQs