Incident Response Report: Structure, Examples, and How to Write One That Holds Up Under Audit
Regulatory investigations and post-incident audits increasingly scrutinize not just how incidents are handled, but how they are documented. Inconsistent reporting, missing timelines, and unclear decision trails often create challenges during supervisory reviews, especially under frameworks like NIST and breach disclosure requirements.

For security, compliance, and audit leaders, the challenge extends beyond response; it is ensuring every action and outcome is clearly traceable and defensible.
An incident response report sits at the center of this requirement, connecting technical response with governance expectations. It must capture decisions, control gaps, and corrective actions in a structured, audit-ready format.
This article examines how to structure and write an incident response report that holds up under audit scrutiny, outlining its core components, common gaps, and the practices that support consistent, decision-ready reporting.
Quick Look
- An incident response report must document decisions, timelines, and control performance, not just describe events.
- Regulatory and audit scrutiny (e.g., NIST-aligned expectations) require clear, traceable reporting with evidence.
- Standard components include timeline, impact, root cause, actions taken, and remediation plans.
- Poorly structured reports create gaps in audit defensibility and limit leadership visibility.
- Effective reporting links incidents to control failures and broader risk exposure, enabling systemic improvement.
- Writing requires disciplined steps: real-time capture, structured narrative, fact validation, and audit readiness checks.
- Consistency through templates and workflows is critical to compare incidents and scale oversight.
What is an Incident Response Report?
An incident response report is not a retrospective summary; it is a structured record that connects incident activity to accountability, oversight, and control outcomes. In regulated environments, it must clearly document what occurred, how decisions were made, and whether response actions aligned with defined procedures and expectations.
Definition
An incident response report serves as a formal, traceable record of the incident lifecycle, capturing actions, decisions, and outcomes in a way that supports audit, regulatory review, and internal accountability. It goes beyond description by linking events to control effectiveness, response quality, and organizational readiness under scrutiny.
How It Fits Into the Incident Response Lifecycle
An effective incident response report aligns directly with each phase of response:
- Detection: Initial identification, alert source, and validation steps
- Containment: Actions taken to isolate affected systems and prevent spread
- Recovery: Restoration of systems, validation of integrity, and resumption of operations
- Lessons Learned: Post-incident review, control evaluation, and improvement planning
Who Uses the Report and Why
Different stakeholders rely on the report for distinct decision-making needs:
- Audit teams: Validate control effectiveness and evidence completeness
- Executives: Assess business impact, response adequacy, and accountability
- Regulators: Review compliance with reporting obligations and response standards
- Security leaders: Improve incident response processes and operational readiness
Also read: Operational Risk Management Examples and Strategies
Why Incident Response Reports Matter Beyond Documentation
In practice, the value of an incident response report is determined by how well it supports oversight, not how thoroughly it describes events. Reports that fail to connect incident activity with governance expectations often fall short during audits, leadership reviews, and regulatory inquiries.
To meet operational demands, reporting must translate technical response into decision-relevant insight and defensible evidence:
1. Regulatory and Audit Expectations
Incident response reports function as evidence artifacts in regulatory and audit contexts. They demonstrate whether response actions align with established frameworks such as NIST and sector-specific requirements.
Without structured documentation, organizations face challenges in proving compliance, reconstructing decisions, and responding to enforcement scrutiny, particularly when timelines or control actions are unclear.
2. Decision Visibility for Leadership
Leadership relies on incident response reports to understand what happened, why it mattered, and how effectively it was handled. Clear timelines, quantified impact, and documented decisions enable executives to assess risk exposure, allocate resources, and evaluate accountability.
Reports that lack clarity often delay decision-making and weaken organizational response alignment.
3. Post-Incident Learning and Control Improvement
An incident response report should enable systematic learning, not just closure. By identifying control failures, response gaps, and process inefficiencies, it supports continuous improvement.
This structured feedback loop informs policy updates, strengthens controls, and reduces the likelihood of recurrence, aligning incident management with long-term governance maturity.
Also read: Cybersecurity Risk Avoidance: Proactive Strategies to Safeguard Your Organization
8 Core Components of an Incident Response Report
An effective incident response report must move beyond descriptive documentation and provide structured insight into how the incident unfolded, how it was handled, and what it reveals about control effectiveness. Each component plays a role in ensuring the report can withstand audit scrutiny and support operational improvement. The following elements establish that structure:
1. Incident Overview and Classification
This section defines the incident’s identity and severity, establishing context for all subsequent analysis. Classification must align with internal policies and recognized frameworks to ensure consistency across incidents.
- Incident type (e.g., data breach, ransomware, system outage)
- Severity level based on predefined classification criteria
- Scope of impact across systems, users, or regions
- Reference to internal classification standards or frameworks
- Initial assessment of risk exposure
2. Timeline of Events
A clear, chronological timeline enables reconstruction of events and evaluation of response speed and effectiveness.
- Timestamp of detection and alert validation
- Escalation points and stakeholder involvement
- Containment actions and timing
- Recovery milestones and resolution confirmation
- Any delays or gaps in response execution
3. Affected Systems, Data, and Users
This section quantifies impact and clarifies exposure, supporting both internal decision-making and regulatory reporting.
- Systems, applications, or infrastructure affected
- Type and sensitivity of data exposed or at risk
- Number and category of impacted users or entities
- Business operations disrupted or degraded
- Regulatory implications based on data type
4. Actions Taken and Response Measures
Documenting response actions provides visibility into how effectively the incident was handled.
- Containment strategies implemented
- Eradication of the threat or root issue
- Recovery processes and validation steps
- Coordination across teams and functions
- Deviations from standard response procedures
5. Root Cause Analysis
Understanding how the incident originated is essential for preventing recurrence.
- Identified attack vector or failure trigger
- Vulnerabilities exploited or control breakdowns
- Process or system weaknesses contributing to the incident
- External vs internal causation factors
- Supporting evidence or investigation findings
6. Control Gaps and Risk Exposure
This section connects the incident to broader governance and risk management concerns.
- Missing or ineffective controls
- Failures in monitoring, detection, or escalation
- Policy or procedural gaps
- Residual risk following incident resolution
- Alignment with enterprise risk frameworks
7. Recommendations and Remediation Plan
Actionable recommendations translate findings into improvement steps.
- Immediate remediation actions
- Long-term control enhancements
- Policy or process updates required
- Ownership and accountability for implementation
- Timelines for remediation completion
8. Lessons Learned and Follow-Up Actions
This section ensures the incident contributes to organizational learning.
- Key takeaways from response effectiveness
- Required changes in training or awareness
- Improvements to incident response playbooks
- Follow-up audits or validation checks
- Continuous monitoring enhancements
Also read: What Is the Difference Between Risk Control and Risk Management?
6 Simple Steps to Write an Incident Response Report
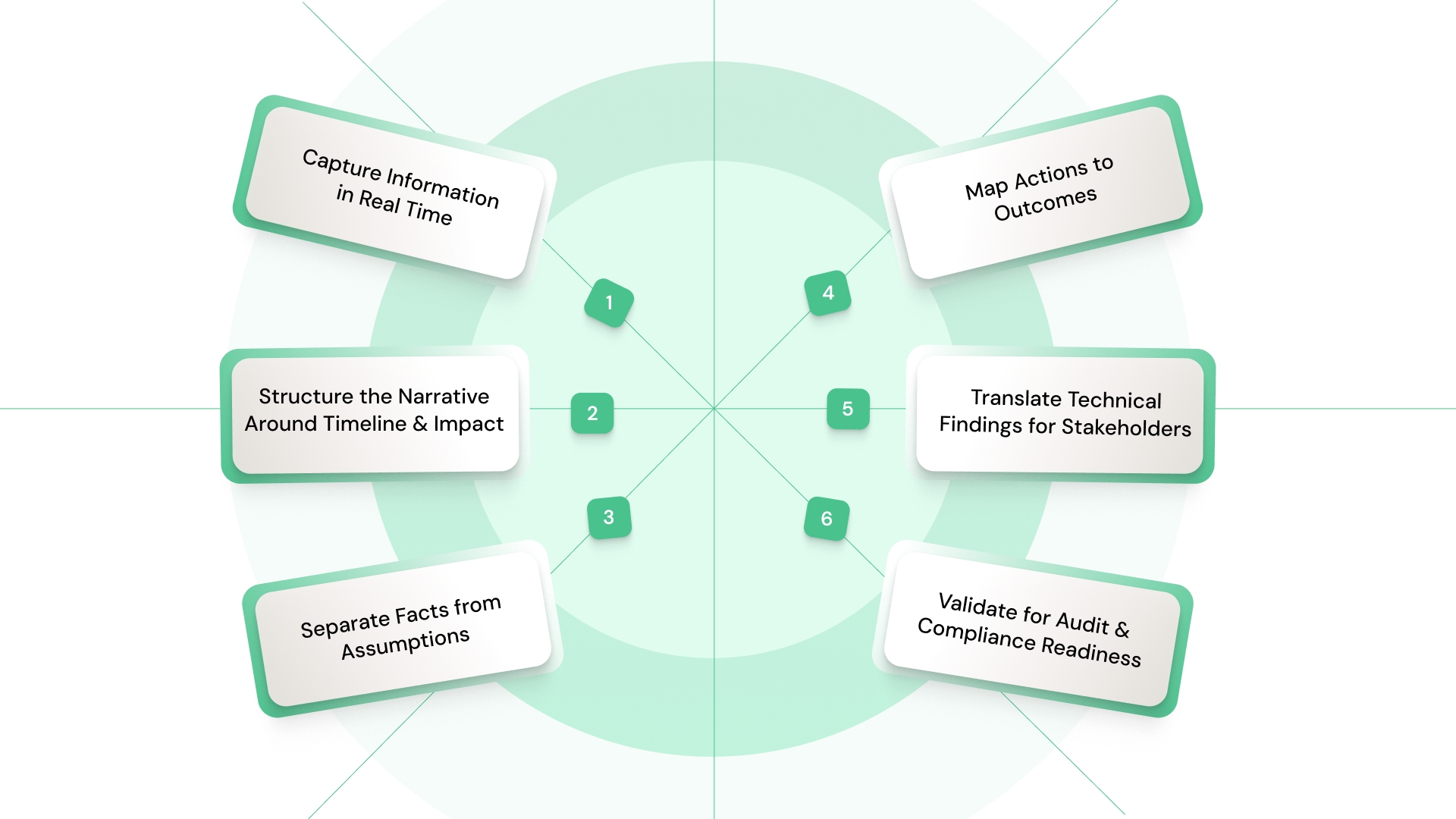
Writing an incident response report requires disciplined structuring, not retrospective storytelling. The objective is to create a document that is factually accurate, operationally clear, and defensible under audit.
Each step ensures that information is captured, validated, and presented in a way that supports both technical and executive stakeholders:
Step 1: Capture Information in Real Time
Accurate reporting depends on timely data capture during the incident lifecycle.
- Log events, actions, and timestamps as they occur
- Preserve system logs and forensic evidence
- Document decisions and responsible parties
- Track communication between teams
- Avoid reliance on post-incident reconstruction
Step 2: Structure the Narrative Around Timeline and Impact
A well-structured report ensures clarity and prevents fragmented documentation.
- Organize content chronologically
- Link events to business and operational impact
- Avoid scattered or redundant descriptions
- Maintain consistency in format across incidents
- Ensure logical progression of events
Step 3: Separate Facts from Assumptions
Maintaining objectivity is critical for credibility and audit defensibility.
- Clearly distinguish verified facts from hypotheses
- Avoid speculative language
- Support claims with evidence or logs
- Document uncertainties explicitly
- Update assumptions as new information emerges
Step 4: Map Actions to Outcomes
Reports must demonstrate whether response actions were effective.
- Link each action to a measurable outcome
- Identify actions that failed or delayed containment
- Highlight successful mitigation steps
- Evaluate response efficiency
- Connect actions to control effectiveness
Step 5: Translate Technical Findings for Stakeholders
Reports must be accessible to both technical and non-technical audiences.
- Simplify technical findings without losing accuracy
- Provide context for business impact
- Use clear, structured language
- Avoid excessive technical jargon
- Ensure readability for leadership and audit teams
Step 6: Validate for Audit and Compliance Readiness
Before finalization, the report must meet governance standards.
- Verify completeness of all sections
- Ensure traceability of actions and decisions
- Cross-check against regulatory requirements (e.g., NIST guidance)
- Confirm evidence is properly documented
- Review for consistency and clarity
See how standardized workflows can ensure every incident report remains complete, traceable, and aligned with governance expectations. Book a demo with VComply to learn more.
Common Gaps That Undermine Incident Reports
Even well-documented incidents can fail to meet governance expectations if reporting lacks structure, clarity, or accountability. These gaps often become visible during audits or leadership reviews, where incomplete or inconsistent reporting limits the ability to assess response effectiveness. The following issues frequently reduce the value of incident response reports:
1. Lack of Structured Format
Without a standardized format, reports vary in depth and clarity, making comparison and analysis difficult across incidents. This inconsistency weakens oversight and prevents organizations from identifying patterns or systemic issues, ultimately limiting their ability to improve incident response processes at scale.
2. Missing Timeline or Evidence
Incomplete timelines or missing supporting evidence undermine the report’s credibility. When actions cannot be traced or validated, audit defensibility is compromised, and organizations may struggle to demonstrate compliance with regulatory expectations or internal policies.
3. Overly Technical Without Context
Reports that focus heavily on technical detail without contextual explanation limit their usefulness for leadership. Decision-makers require clarity on impact, risk, and accountability, not just technical descriptions, making balance essential for effective communication.
4. Failure to Link to Control Failures
If reports do not connect incidents to underlying control gaps, they fail to support improvement. Without identifying process or system weaknesses, organizations miss opportunities to strengthen governance and reduce future risk exposure.
Also read: Differences and Similarities between ISO 27001 and SOC 2
Best Practices for Writing Incident Response Reports
Consistent, high-quality reporting depends on disciplined practices that ensure clarity, comparability, and decision relevance across incidents. These practices strengthen both operational oversight and audit readiness:
1. Keep Reports Fact-Based and Clear
Maintain objectivity by focusing on verified information, supported by evidence and structured documentation.
Impact: Improves audit defensibility and reduces ambiguity in regulatory reviews.
2. Use Standardized Templates Across Incidents
Adopt a consistent reporting structure to ensure comparability and completeness.
Impact: Enables trend analysis, strengthens oversight, and supports scalable incident management.
3. Focus on Decision-Relevant Insights
Prioritize insights that inform action, rather than presenting raw data without context.
Impact: Enhances leadership decision-making and aligns reporting with governance objectives.
Explore how CaseOps structures incident reporting workflows to improve accountability, visibility, and audit readiness across your organization.
Incident Response Report Template (Practical Format)
Sample Structure
A usable incident response report template must go beyond headings and ensure traceability, accountability, and audit defensibility. Each section should capture not just what happened, but how decisions were made and whether controls performed as expected.
- Incident Identification
- Incident ID, date/time of detection, reporting source
- Incident type and severity classification (aligned to internal policy)
- Business unit / systems affected
- Executive Summary
- Concise description of the incident and its business impact
- Key decisions made during response
- Current status (resolved, ongoing monitoring, escalation)
- Detailed Timeline of Events
- Detection time and validation steps
- Escalation points and stakeholders involved
- Containment, eradication, and recovery milestones
- Any delays, gaps, or deviations from expected response time
- Impact Assessment
- Systems, applications, and infrastructure affected
- Data exposure (type, sensitivity, volume)
- Operational disruption (downtime, service impact)
- Regulatory exposure (e.g., breach notification triggers)
- Response Actions and Effectiveness
- Actions taken across containment, eradication, and recovery
- Tools, teams, and workflows involved
- Effectiveness of each action (what worked, what did not)
- Deviations from incident response playbooks
- Root Cause Analysis
- Initial attack vector or failure trigger
- Control breakdowns (technical or procedural)
- Contributing factors (human error, system gaps, third-party risk)
- Evidence supporting findings
- Control Gaps and Risk Implications
- Missing or ineffective controls identified
- Monitoring or detection failures
- Residual risk after incident closure
- Alignment with enterprise risk categories
- Remediation and Action Plan
- Immediate fixes implemented
- Long-term corrective actions
- Ownership and accountability for each action
- Defined timelines and validation checkpoints
- Lessons Learned and Governance Impact
- Key insights from response execution
- Required updates to policies, procedures, or playbooks
- Training or awareness gaps identified
- Recommendations for strengthening incident response maturity
Also read: Understanding Cybersecurity Risk Management
Bringing Discipline to Incident Reporting Workflows with VComply
Incident reporting often breaks down in execution, not intent. Teams operate across fragmented tools, timelines are inconsistently captured, and accountability becomes difficult to trace once incidents move beyond initial response.
This lack of structure limits visibility, complicates audits, and weakens the organization’s ability to learn from incidents in a consistent, repeatable way.
VComply addresses these challenges by structuring incident management through its CaseOps module, enabling organizations to manage reporting as part of a controlled, end-to-end workflow rather than a standalone task.
- Centralized incident tracking with structured workflows and ownership assignment
- Real-time capture of actions, timelines, and decisions for audit-ready reporting
- Standardized reporting formats aligned with governance and compliance needs
- Integrated visibility across incidents, risks, and controls
- Configurable workflows to align with internal policies and regulatory expectations
Book a demo with VComply to see how structured systems can help you operationalize your incident response reporting workflow.
Conclusion
An effective incident response report does more than document events; it establishes a defensible record of decisions, control performance, and organizational readiness under scrutiny.
When structured correctly, it enables leaders to assess response effectiveness, auditors to validate compliance, and teams to identify systemic weaknesses that require attention.
Without this level of clarity and consistency, reporting becomes fragmented, limiting both oversight and the organization’s ability to improve incident response maturity over time.
In practice, many organizations struggle to maintain this level of structure across incidents, especially when reporting relies on manual processes and disconnected systems.
VComply’s CaseOps module addresses this by introducing disciplined workflows, centralized visibility, and standardized reporting structures that align incident management with governance expectations.
By ensuring that every incident is tracked, documented, and reviewed within a controlled system, teams can move from reactive reporting to consistent, audit-ready processes.
Start a 21-day free trial of VComply to explore how CaseOps supports structured incident accountability and strengthens reporting consistency across your organization.
FAQs
An incident response report should include a clear timeline, impact assessment, actions taken, root cause analysis, control gaps, and recommendations. It must provide traceable evidence and structured insight to support audit, regulatory review, and internal decision-making.
Typically, the incident response lead or security operations team is responsible, with input from IT, compliance, and legal teams. Accountability depends on organizational structure, but it must ensure accuracy, completeness, and alignment with governance requirements.
The report should be detailed enough to reconstruct events, validate decisions, and support audits. It must balance technical depth with clarity, ensuring both technical teams and leadership can understand the incident and its implications.
A timeline provides chronological clarity, enabling stakeholders to assess response speed, identify delays, and validate actions taken. It is essential for audit defensibility and understanding how effectively the incident was managed.
Organizations can standardize reporting by using structured templates, defined workflows, and centralized systems. Platforms like VComply help enforce consistency, improve visibility, and align reporting with governance and compliance requirements.
Reports should be reviewed immediately after incident closure and periodically as part of audit and governance processes. Regular review ensures lessons are captured, controls are improved, and reporting standards remain consistent.

