How to Build Compliance Policies in 2026 That Stand Up to Audit Scrutiny
Regulatory enforcement actions increasingly highlight a recurring pattern: organizations maintain documented policies, but fail to demonstrate how those policies are executed, validated, and enforced in practice.

As organizations scale across systems, vendors, and regulatory frameworks, compliance policies become harder to enforce consistently. Teams rely on static documents, manual tracking, and fragmented systems, which weakens accountability and delays validation. Leadership cannot determine whether policies are functioning because visibility into execution remains incomplete and reactive.
This guide explains how compliance policies function as enforceable systems through ownership, control linkage, and audit-ready evidence.
At a Glance
- Compliance policies fail when they remain disconnected from controls, workflows, and measurable execution signals across teams and systems.
- Audit readiness depends on traceability, where every policy maps to controls, tasks, and verifiable evidence generated during execution.
- Policy effectiveness must be measured through acknowledgment latency, control validation results, and exception trends rather than document existence.
- Version control is critical for audit defensibility, ensuring organizations can prove which policy was active during a specific period.
- Ownership must extend beyond policy authorship to include control owners and execution-level accountability across workflows.
- Scalable compliance requires systemization, where policies, controls, risks, and incidents operate within a unified governance structure.
What Is a Compliance Policy
A compliance policy defines how an organization aligns its operations with regulatory requirements, internal standards, and control expectations. It establishes rules, responsibilities, and enforcement mechanisms that guide decision-making and operational behavior.
Effective policies connect regulatory obligations to workflows, controls, and measurable outcomes. Failures occur when policies remain static documents without ownership, validation mechanisms, or traceability, making it difficult to demonstrate compliance during audits or regulatory reviews.
Also read: How to Improve Compliance Management for Audit-Ready Programs 2026
The Role of Compliance Policy
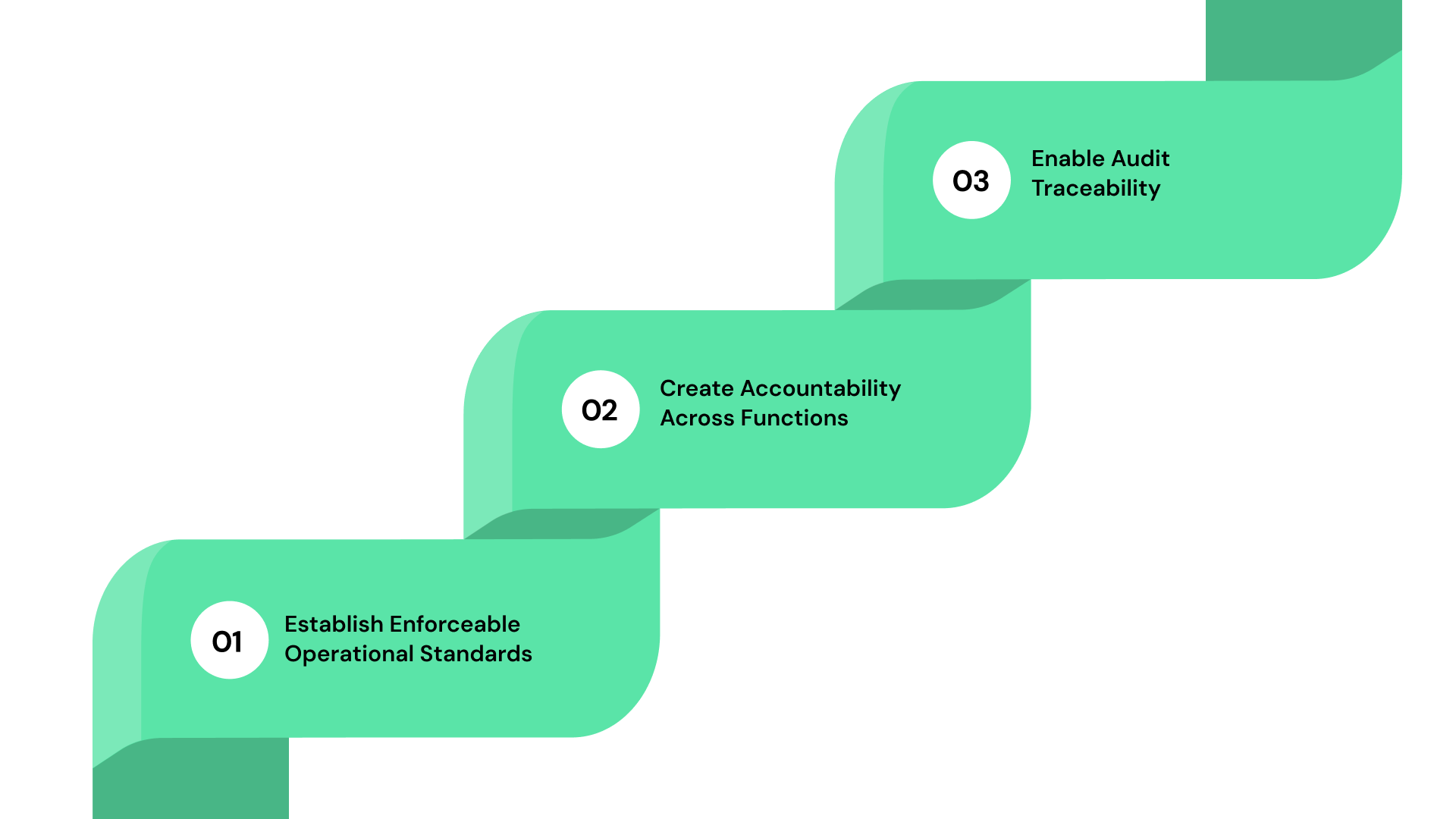
Compliance policies serve as the bridge between regulatory requirements and operational execution, ensuring that expectations translate into enforceable actions across teams:
1. Establish Enforceable Operational Standards
Policies define how regulatory obligations translate into actionable requirements across workflows, systems, and teams. They ensure that expectations are not interpreted differently across departments. Without enforceable standards, compliance becomes inconsistent and dependent on individual judgment rather than structured execution aligned with regulatory intent.
2. Create Accountability Across Functions
Policies assign responsibility for control execution, monitoring, and validation across business functions. This ensures that compliance is not centralized within a single team but distributed across operational roles. Without accountability, tasks remain incomplete, and enforcement becomes inconsistent across departments and processes.
3. Enable Audit Traceability
Policies provide the foundation for linking regulatory requirements to controls and evidence. This ensures that organizations can demonstrate how requirements are implemented and validated. Without traceability, audits rely on explanations instead of verifiable proof, increasing regulatory risk.
The 6 Core Components of a Compliance Policy
A compliance policy must function as an execution framework rather than a documentation artifact. Each component must support enforceability, traceability, and measurable outcomes:
1. Clear Scope, Applicability, and Regulatory Mapping
Policies must define scope, affected systems, and applicable regulatory frameworks such as SOX or HIPAA. This ensures clarity on where and how policies apply. Without a defined scope, policies become ambiguous, leading to inconsistent interpretation and execution across teams.
2. Defined Ownership Across Policy, Control, and Execution Levels
Ownership must extend beyond policy creation to include control owners and task-level accountability. Each policy requirement must map to individuals responsible for execution and validation. This ensures accountability is enforced across workflows rather than remaining centralized within compliance teams.
3. Control Linkage and Validation Requirements
Policies must map directly to controls that can be tested and validated. Each requirement should define how compliance will be measured through control execution. Without validation, policies remain assumptions rather than enforceable mechanisms.
4. Evidence Expectations and Audit Traceability
Policies must specify what evidence is required to demonstrate compliance. This includes logs, approvals, and validation records. Evidence must be generated during execution and linked to controls, ensuring audit readiness without retrospective documentation.
5. Version Control, Approval, and Change Tracking
Policies must maintain version history, approval workflows, and change logs. This ensures organizations can demonstrate policy evolution and alignment with regulatory updates. Without version control, audit defensibility weakens significantly.
6. Distribution, Attestation, and Enforcement Mechanisms
Policies must be distributed based on roles and require structured acknowledgment. Attestation tracking ensures employees confirm understanding and acceptance. Enforcement mechanisms ensure non-compliance is detected and addressed systematically.
This is where most organizations recognize that policy structure alone is not enough without system-driven enforcement. Evaluate how ComplianceOps connects policies, controls, and validation workflows so each requirement is measurable and continuously enforced.
Also read: 5 Essential Compliance Management Tools For Teams
Examples of Compliance Policies in Business Operations
Compliance policies vary based on regulatory exposure and operational complexity, but they typically align with the following categories:
1. Data Protection and Privacy Policies
These policies define how personal data is collected, processed, and protected. They align with frameworks such as HIPAA and GDPR. They include controls for access management, consent tracking, and data retention.
2. Financial Reporting and SOX Compliance Policies
These policies ensure accuracy and integrity in financial reporting. They define controls for approvals, reconciliations, and audit trails. They support regulatory expectations for transparency and accountability in financial operations.
3. Information Security and Access Control Policies
These policies govern system access, authentication, and data protection. They define controls for user permissions, encryption, and monitoring. They ensure that sensitive data is protected against unauthorized access.
4. Third-Party Risk and Vendor Management Policies
These policies govern how vendors are evaluated, onboarded, monitored, and offboarded based on risk exposure and regulatory requirements. They define due diligence processes, contractual controls, and ongoing monitoring expectations.
5. Incident Response and Regulatory Reporting Policies
These policies define how organizations detect, escalate, investigate, and report incidents, including breaches, control failures, or regulatory violations. They establish timelines, ownership, and reporting obligations aligned with regulatory expectations.
How to Build a Compliance Policy
Building a compliance policy requires structured workflows that connect regulatory requirements to execution:
1. Policy Creation Based on Risk and Regulatory Triggers
Policies should originate from regulatory requirements, audit findings, or risk assessments.
- Identify applicable regulations and risks
- Define scope and objectives
- Map to affected workflows
- Assign initial ownership
2. Multi-Layer Approval Workflows With Accountability
Approval workflows must validate accuracy and feasibility before implementation.
- Include compliance, legal, and operations
- Define approval hierarchy
- Track approval timestamps
- Maintain audit logs
3. Controlled Distribution Based on Roles and Functions
Policies must reach relevant stakeholders based on responsibilities.
- Map roles to policy applicability
- Automate distribution
- Track delivery status
- Ensure accessibility
4. Attestation Tracking and Acknowledgment Validation
Acknowledgment must be tracked and validated continuously.
- Capture acknowledgment timestamps
- Track completion rates
- Identify delays
- Trigger reminders
5. Continuous Review Cycles and Update Triggers
Policies must evolve based on regulatory and operational changes.
- Define review frequency
- Monitor regulatory updates
- Track version changes
- Communicate updates
Also read: UK Modern Slavery Act Compliance: Requirements & Best Practices
How to Measure Compliance Policy Effectiveness Using Execution Metrics
Measurement ensures that policies function as intended rather than existing as documentation:
- Policy Acknowledgment Rates and Timeliness: Track how quickly employees acknowledge policies after distribution. Delays indicate weak enforcement or communication gaps, even if completion rates appear high.
- Control Validation Outcomes Linked to Policy Requirements: Measure whether controls mapped to policies are tested and operating effectively. Failed validations indicate execution gaps or flawed policy design.
- Exception Frequency and Policy Deviation Trends: Analyze recurring exceptions to identify systemic issues. High exception rates often indicate impractical policies or inconsistent enforcement across teams.
- Audit Findings Attributed to Policy Gaps: Track audit findings linked to policy failures. This helps identify whether issues originate from documentation gaps or execution failures.
7 Common Compliance Policy Failures That Disrupt Execution
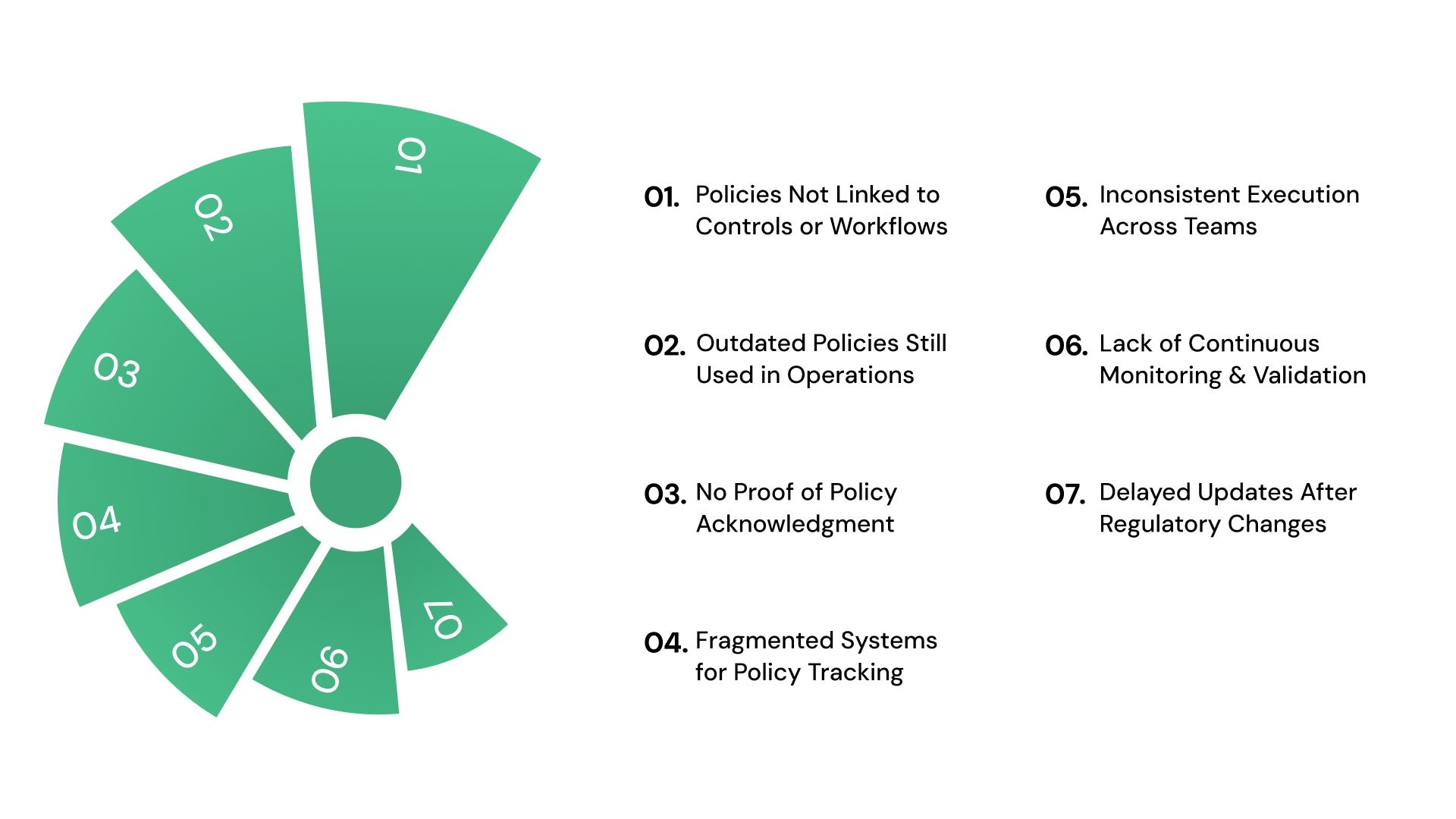
Compliance policy failures are rarely caused by missing documentation. They emerge when policies are not embedded into workflows, validated through controls, or supported by traceable evidence.
These failures indicate structural gaps in how policies are executed, monitored, and updated across systems and teams.
The most critical execution failures that disrupt compliance policy effectiveness include:
1. Policies Not Linked to Controls or Workflows
Policies often define requirements without specifying how those requirements are executed within operational workflows. This disconnect prevents organizations from validating whether policies are enforced consistently.
Without linking policies to controls and tasks, compliance becomes dependent on interpretation rather than measurable execution, making it difficult to demonstrate enforcement during audits.
2. Outdated Policies Still Used in Operations
Policy updates may be approved centrally, but fail to replace older versions across systems and teams. Employees continue referencing outdated documents stored locally or in shared drives.
This creates misalignment between current regulatory requirements and actual execution, exposing organizations to audit findings where enforcement reflects obsolete policy versions rather than approved updates.
3. No Proof of Policy Acknowledgment
Organizations distribute policies without structured acknowledgment tracking or validation. As a result, there is no verifiable record of whether employees have reviewed or accepted policy requirements.
During audits, this gap signals weak governance, as organizations cannot demonstrate awareness, accountability, or enforcement across impacted roles and functions.
4. Fragmented Systems for Policy Tracking
Policy lifecycle activities are often managed across emails, spreadsheets, and disconnected tools. This fragmentation prevents organizations from maintaining a unified view of policy status, ownership, and compliance progress.
Without centralized tracking, teams spend time reconciling information instead of enforcing policies, increasing the risk of inconsistencies and missed actions.
5. Inconsistent Execution Across Teams
Different teams interpret and apply policies based on local practices rather than standardized workflows. This creates variability in how controls are executed and documented across departments.
During audits, these inconsistencies appear as systemic weaknesses, where the same policy produces different outcomes depending on the team or system involved.
6. Lack of Continuous Monitoring and Validation
Policies are often reviewed periodically rather than monitored continuously through control validation and execution data. This delays detection of non-compliance and allows gaps to persist between audit cycles.
Without ongoing monitoring, organizations rely on assumptions instead of real-time insights into whether policies are functioning as intended.
7. Delayed Updates After Regulatory Changes
Regulatory updates or audit findings do not always trigger timely policy revisions. This delay creates a gap between external requirements and internal governance.
Policies remain outdated while operations continue, increasing exposure to compliance failures that could have been mitigated through structured update and approval workflows.
These failure patterns rarely require more policies, but they do require structured lifecycle control and enforcement. Understand how PolicyOps introduces version control, ownership tracking, and attestation workflows that reduce policy execution gaps across teams.
Also read: Optimizing Policy Management in Behavioral Health
Best Practices to Maintain Continuous Compliance Policy Governance
Sustaining compliance policy governance requires systems that enforce consistency, enable real-time visibility, and adapt to regulatory and operational changes. Governance must function as a continuous process where policies are validated, updated, and aligned with execution at all times.
To maintain consistency and audit readiness, organizations should focus on the following practices:
1. Continuous Monitoring Instead of Periodic Reviews
Policies must be validated through ongoing control testing and execution tracking rather than scheduled reviews. Continuous monitoring ensures that deviations are detected as they occur, not after the fact.
This approach allows compliance teams to address issues early and maintain alignment between policy intent and operational execution.
2. Shared Visibility Across Compliance, Risk, and Operations
Policy governance requires coordination across multiple functions, but fragmented visibility creates gaps in execution and decision-making. Centralized dashboards that combine policy status, control performance, and risk exposure provide a unified view, enabling teams to identify gaps quickly and make informed decisions.
This ensures that all stakeholders operate with the same information, improving alignment and enabling faster, informed responses.
3. Risk-Based Prioritization of Policy Enforcement
Not all policies carry equal impact, yet many organizations apply uniform enforcement across all areas. Risk-based prioritization ensures that policies governing high-risk activities receive more frequent validation and stricter oversight. This approach improves resource allocation and strengthens protection against critical compliance failures.
4. Feedback Loops From Audits and Incidents Into Policies
Audit findings and incidents often remain isolated from policy updates, causing the same issues to recur. Integrating feedback loops ensures that insights from audits, exceptions, and incidents directly inform policy revisions and workflow improvements, creating a system that evolves based on actual execution data.
5. Strict Version Control and Change Management
Policy updates must follow structured workflows that capture approvals, version history, and communication to impacted stakeholders. This ensures that all teams operate on current policies and that historical versions remain traceable for audit purposes.
Strong version control prevents confusion, reduces risk, and supports defensible compliance during reviews.
Also read: Top 5 Nonprofit Compliance Mistakes and How to Avoid Them
Turn Compliance Policies Into Enforceable, Measurable Workflows with VComply
Compliance policies break when lifecycle stages, controls, and enforcement remain disconnected across systems and teams. This fragmentation weakens traceability, delays validation, and creates gaps that surface during audits.
VComply structures compliance policies through integrated workflows that connect ownership, controls, and evidence into a unified system, ensuring that policies are not only documented but consistently executed, validated, and traceable across teams:
- Use ComplianceOps to map policies directly to regulatory requirements and control frameworks: This ensures every policy requirement is translated into testable controls with clear execution paths and audit linkage.
- Apply PolicyOps to manage the full policy lifecycle with version control and attestation tracking: Policies remain current, approvals are documented, and employee acknowledgment is tracked with time-stamped records for audit defensibility.
- Integrate RiskOps to prioritize policy enforcement based on real risk exposure: This allows you to focus validation and monitoring efforts on high-impact areas instead of applying uniform enforcement across all policies.
- Track violations and remediation workflows using CaseOps: Every policy breach is logged, assigned, investigated, and resolved within structured workflows, ensuring accountability and closure visibility.
- Leverage the GRCOps Suite to unify compliance, risk, policy, and incident data: This creates a centralized system of record where leadership can monitor policy effectiveness, control performance, and enforcement trends in real time.
This structure ensures that compliance policies operate as enforceable systems rather than static documents. Book a demo with VComply to evaluate how structured workflows improve policy execution and audit readiness.
Conclusion
Compliance policies determine how organizations translate regulatory requirements into operational behavior. When policies connect ownership, controls, and evidence, they support consistent execution and audit readiness across teams.
VComply enables organizations to centralize policy management, align controls with execution, and maintain visibility across compliance workflows. This approach replaces fragmented tracking with structured governance.
Start a 21-day free trial of VComply to evaluate how integrated systems improve compliance policy execution and audit outcomes.
FAQs
A compliance policy defines how regulatory requirements translate into operational rules, controls, and responsibilities. It ensures that expectations are enforced consistently across workflows, supported by measurable outcomes and audit-ready evidence.
Policies fail when they are not linked to controls, ownership, or evidence. This creates gaps between documented intent and actual execution, making it difficult to demonstrate compliance under audit conditions.
Organizations measure effectiveness through acknowledgment rates, control validation outcomes, exception trends, and audit findings. These metrics provide insight into whether policies are enforced consistently.
A compliance policy should include scope, regulatory mapping, ownership, control linkage, evidence requirements, version control, and enforcement mechanisms to ensure traceability and accountability.
Policies should be reviewed regularly based on regulatory updates, audit findings, and risk changes. Continuous monitoring ensures that policies remain aligned with operational and regulatory requirements.
Organizations can implement structured systems like VComply that connect policies, controls, ownership, and evidence into unified workflows, ensuring consistent execution and audit readiness.

