Data Protection Compliance: Key Regulations and How to Execute Them
Regulatory audits continue to reveal a consistent issue: controls are defined but not consistently enforced or evidenced across systems. For compliance and risk teams, the challenge is not frameworks; it is proving control effectiveness across fragmented environments, vendors, and reporting cycles.

Gaps in access management, data retention, and third-party oversight often emerge where accountability is dispersed, and evidence is hard to consolidate. As data flows through cloud platforms and external processors, maintaining audit-ready traceability becomes an ongoing operational need.
In this context, data protection compliance is less about alignment with frameworks and more about reliable execution. The priority shifts to continuously monitoring, validating, and reporting controls as systems scale and regulatory expectations increase. Sustaining consistency and structured oversight is key to maintaining both regulatory confidence and internal control integrity.
At a Glance
Data protection compliance is the operational ability to enforce and prove that data handling meets regulatory requirements across systems and workflows.
- It requires translating regulations (HIPAA, CCPA, GLBA) into consistent, testable controls rather than managing them in isolation.
- Most failures occur at the execution layer. Policies exist, but enforcement, ownership, and evidence remain inconsistent.
- Fragmented systems reduce visibility, making it difficult to track, control, and produce audit-ready evidence.
- Periodic, audit-driven approaches create gaps; continuous monitoring and real-time oversight are becoming baseline expectations.
- Mature programs rely on systemized compliance operations; centralized control tracking, clear accountability, and always-available evidence.
What Is Data Protection Compliance?
Data protection compliance is how an organization ensures its handling of sensitive data meets regulatory requirements, and can prove it when reviewed. It goes beyond having policies in place; it depends on whether controls around access, storage, sharing, and retention are consistently followed and can be verified through clear records and system activity.
The difference between data protection and compliance is practical: data protection is the goal, while compliance is how that goal is enforced and demonstrated. Issues usually arise when expectations are documented but not consistently executed or tracked, making it difficult to show accountability under audit or regulatory scrutiny.
Data Compliance vs Data Protection Compliance
In practice, data protection compliance builds on both, requiring organizations to align regulatory obligations with enforceable security controls.
| Aspect | Data Compliance | Data Security Compliance |
|---|---|---|
| Scope | Broad: covers all regulatory requirements related to data handling | Narrow: focuses only on protecting data from unauthorized access |
| Objective | Ensure data is collected, processed, stored, and shared in line with laws and standards | Ensure technical safeguards are in place to secure data |
| Coverage | Privacy, governance, retention, consent, reporting, and security | Encryption, access controls, network security, monitoring |
| Ownership | Compliance, legal, risk, operations | IT, security, engineering |
| Regulatory Link | Driven by laws like HIPAA, CCPA, GLBA, GDPR | Driven by security standards like NIST, ISO 27001, PCI DSS |
| Audit Expectation | Demonstrate end-to-end control over data lifecycle | Demonstrate effectiveness of security controls |
Data security compliance is a subset of data compliance. Security controls may be implemented correctly, but without alignment to regulatory obligations, organizations still fail audits.
Why Data Protection Compliance Has Become Operationally Complex
Data protection compliance has become harder to sustain, not because requirements are unclear, but because execution now spans multiple systems, teams, and regulatory expectations. The challenge lies in maintaining consistent control and visibility as data moves across environments that are not centrally governed.
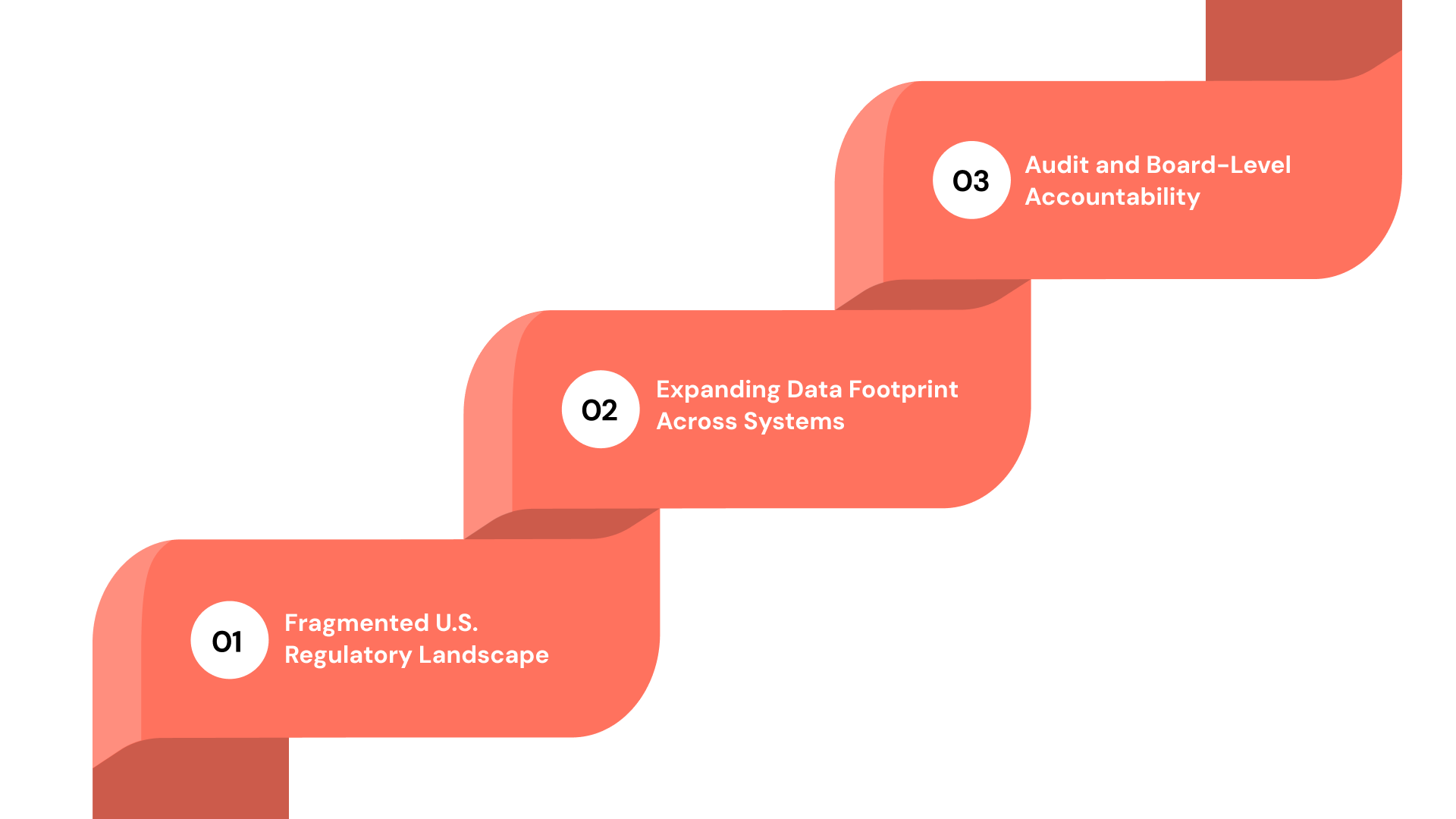
1. Fragmented U.S. Regulatory Landscape
U.S. organizations operate under a mix of federal and state-level regulations, each with different requirements for data use, disclosure, and consumer rights. Laws such as HIPAA, GLBA, and CCPA introduce overlapping but not identical obligations. For lean compliance teams, this means constantly interpreting how the same control applies across different jurisdictions, often while maintaining separate spreadsheets for each framework. Without a centralized, structured GRC system, consistency and traceability break down fast.
2. Expanding Data Footprint Across Systems
Data no longer lives in one place. It flows across cloud environments, identity providers, SaaS tools, and vendor ecosystems, often without a unified view of who has access, where it’s stored, or how it’s processed. As a result:
- Access controls vary from tool to tool.
- Data ownership and responsibility become unclear.
- Third‑party and vendor‑risk exposure is harder to track and justify.
Without centralized visibility, maintaining control feels like firefighting rather than governance.
3. Audit and Board-Level Accountability
Regulators and boards no longer care just that you have a policy—they demand evidence of control effectiveness, traceable approvals, and clear ownership. They expect:
- Proof that controls are actually running, not just documented.
- Audit‑ready records of who did what, when, and why.
- Timely, structured reporting on data‑protection posture.
When evidence is scattered in emails, folders, and spreadsheets, audits become longer, messier, and more stressful.
If you’re dealing with evolving data protection requirements across multiple systems, the shift is from fragmented tracking to a more structured way of managing compliance.
Platforms like VComply help connect risks, controls, and incidents into a single workflow, making it easier to maintain visibility, enforce ownership, and stay audit-ready without manual effort.
Also Read: How to Set Up GDPR Compliance in 10 Steps
Key Data Protection Regulations U.S. Organizations Must Address
Data protection compliance in the U.S. is shaped by a combination of sector-specific laws and cross-industry standards. The complexity lies not in understanding each regulation individually, but in aligning overlapping requirements into a consistent control structure that can be executed and evidenced.
1. General Data Protection Regulation (GDPR)
The GDPR applies to any organization that processes personal data of EU residents, regardless of where the organization is based. For U.S. organizations with global operations, this introduces additional obligations beyond domestic regulatory requirements.
Key requirements include:
- Lawful basis for processing personal data
- Clear and explicit consent where applicable
- Data minimization and purpose limitation
- Strong security measures to protect personal data
- Breach notification within 72 hours
The regulation also establishes enforceable data subject rights:
- Right to access personal data
- Right to correct inaccurate data
- Right to request deletion (“right to be forgotten”)
Non-compliance can result in fines of up to 4% of global annual revenue or €20 million.
Operational consideration:
Organizations often struggle with maintaining traceability of consent, mapping data across systems, and executing data subject requests within required timelines.
2. California Consumer Privacy Act (CCPA / CPRA)
The CCPA and its amendment, CPRA, apply to businesses that collect or process personal data of California residents and meet defined thresholds.
The regulation focuses on consumer control and transparency, introducing rights such as:
- Right to know what personal data is collected
- Right to delete personal data
- Right to opt out of the sale or sharing of personal data
To meet these requirements, organizations must:
- Maintain accurate and up-to-date privacy disclosures
- Provide mechanisms to process consumer requests
- Track how data is shared across internal systems and third parties
Penalties include:
- $2,500 per violation
- $7,500 per intentional violation
Operational consideration:
Breakdowns typically occur where organizations lack visibility into data flows or cannot consistently fulfill consumer requests across fragmented systems.
Also Read: California Privacy Protection Agency Website Information
3. Health Insurance Portability and Accountability Act (HIPAA)
HIPAA governs the handling of protected health information (PHI) by healthcare providers, insurers, and associated entities.
Core requirements include:
- Administrative, physical, and technical safeguards
- Controlled access to PHI
- Audit logging of access and activity
- Defined breach notification processes
Operational consideration:
Compliance gaps often emerge in access control enforcement and the ability to produce reliable audit logs across systems and vendors.
Industry Standards and Frameworks
In addition to legal requirements, organizations often align with established frameworks to structure their compliance programs:
- NIST → Provides guidance on security controls and risk management
- SOC 2 → Focuses on control effectiveness related to security, availability, and confidentiality
- PCI DSS → Applies to organizations handling payment card data
These frameworks help standardize controls, but also add layers that must be mapped back to regulatory obligations, increasing the need for structured oversight.
Other Relevant Regulations and Standards
Depending on industry and geography, organizations may also need to align with:
- GLBA (Financial Services): Requires safeguarding consumer financial information and managing third-party risk.
- FERPA (Education): Protects student education records and defines access rights.
With regulatory context established, the focus shifts to how compliance is executed in practice.
How to Achieve Data Protection Compliance (Step-by-Step)
Data protection compliance requires aligning visibility, controls, ownership, and monitoring into a system that consistently enforces and demonstrates compliance across environments. The steps below outline a structured approach to building that capability.
Step 1. Establish Data Visibility and Inventory
Compliance begins with knowing what data exists, where it resides, and how it flows across systems.
This requires:
- identifying sensitive and regulated data (PII, PHI, financial data)
- mapping data across applications, cloud environments, and vendors
- defining ownership for each dataset
Without a reliable data inventory, control enforcement becomes inconsistent and difficult to evidence.
Step 2. Map Regulatory Requirements to Unified Controls
Regulations define expectations, but execution depends on translating them into controls that can be applied consistently.
This involves:
- aligning overlapping requirements (HIPAA, CCPA, GLBA) into shared controls
- defining how each control is implemented across systems
- ensuring each control is testable and auditable
When requirements are managed in isolation, duplication and gaps emerge quickly.
Step 3. Define Ownership and Accountability for Controls
Data protection compliance spans multiple teams, but accountability must be explicit.
This includes:
- assigning control owners across compliance, IT, and operations
- defining responsibility for execution, monitoring, and reporting
- ensuring ownership is tracked and visible
Lack of ownership is one of the most common reasons controls fail in practice.
Step 4. Embed Controls into Operational Workflows
Controls must operate within day-to-day processes, not outside them.
This means:
- integrating approvals, reviews, and validations into system workflows
- reducing reliance on manual coordination and follow-ups
- ensuring controls are triggered as part of routine activity
When compliance operates separately from workflows, enforcement becomes inconsistent.
Step 5. Implement Continuous Monitoring and Validation
Periodic audits are no longer sufficient to maintain compliance.
A more effective approach includes:
- ongoing monitoring of control performance
- real-time identification of exceptions or failures
- continuous validation of access, retention, and data handling controls
This reduces the need for reactive audit preparation and improves control reliability.
Step 6. Maintain Centralized Evidence and Audit Readiness
Compliance is ultimately measured by the ability to produce evidence.
Organizations need:
- audit trails showing control execution
- records of approvals, changes, and exceptions
- centralized access to evidence across systems
Manual evidence collection introduces delays and inconsistencies, especially under audit timelines.
Step 7. Strengthen Third-Party and Vendor Oversight
Data often extends beyond internal systems into vendor ecosystems.
Effective compliance requires:
- visibility into how third parties handle data
- contractual and operational controls over data sharing
- monitoring of vendor-related risks and compliance posture
Third-party gaps are a frequent source of regulatory findings.
Execution depends on a set of foundational components working together.
Core Components of a Data Protection Compliance Framework
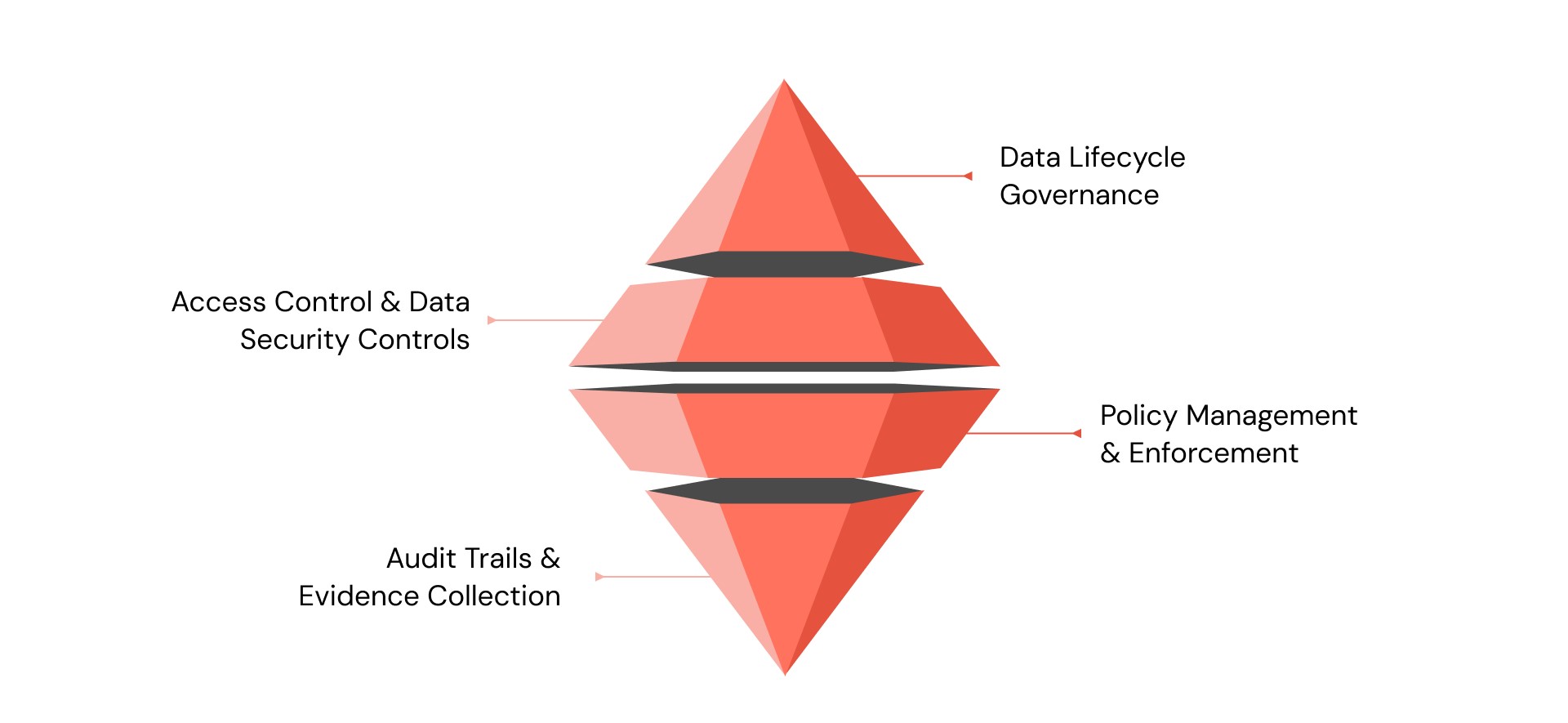
Data protection compliance depends on how well controls are structured across the data lifecycle and how consistently they can be enforced and evidenced. Most breakdowns occur not because controls are missing, but because they are not connected into a system that supports visibility, accountability, and audit readiness.
1. Data Lifecycle Governance
Compliance begins with clear control over how data moves through the organization—from collection to deletion. This includes:
- Defining what data is collected and why
- Controlling how it is processed and stored
- Setting retention and deletion rules based on regulatory requirements
Without lifecycle governance, organizations struggle to demonstrate where sensitive data resides and how it is being managed at any given time.
2. Access Control and Data Security Controls
Access remains one of the most scrutinized areas during audits. Effective compliance requires:
- Role-based access controls aligned with job responsibilities
- Authentication mechanisms to prevent unauthorized access
- Encryption for data at rest and in transit
Gaps often emerge when access policies exist but are not consistently enforced across systems or third-party environments.
3. Policy Management and Enforcement
Policies define expectations, but compliance depends on how those policies are applied in practice. This requires:
- Clear ownership of policy implementation
- Alignment between policy requirements and system controls
- Mechanisms to track acknowledgment and adherence
When policies are not tied to execution, they fail to support audit requirements.
4. Audit Trails and Evidence Collection
Regulatory reviews depend on evidence, not intent. Organizations must be able to show:
- When controls were executed
- Who performed or approved actions
- Whether exceptions were identified and addressed
Manual evidence collection introduces delays and inconsistencies, making continuous, system-driven tracking essential for maintaining audit readiness.
Even well-structured programs experience recurring execution breakdowns.
Common Gaps in Data Protection Compliance Programs

Data protection compliance programs often break down not because requirements are unclear, but because execution is inconsistent across systems and teams. Policies may be well-defined, but enforcement tends to vary in practice, and visibility across controls remains fragmented.
1. Weak Enforcement of Defined Policies
Policies frequently exist at a documentation level but are not embedded into system workflows or consistently followed. This leads to missed access reviews, inconsistent retention practices, and untracked exceptions, making it difficult to prove that controls are actively governing data handling.
2. Fragmented Systems and Limited Visibility
Compliance activities are often spread across multiple tools and teams, leading to a lack of unified oversight. Without centralized visibility, organizations struggle to track and control performance, identify gaps in real time, or produce reliable, consolidated evidence during audits.
3. Reactive, Audit-Driven Execution
Many programs shift into action only when an audit is imminent, forcing teams to reconstruct records and validate controls retrospectively. This reactive approach increases manual effort, introduces inconsistencies, and weakens confidence in the accuracy of compliance reporting.
Addressing these gaps requires a shift in how compliance is managed operationally.
From Fragmented Execution to Structured Compliance Operations
As data environments expand, compliance programs begin to strain where execution depends on manual coordination and disconnected tools. Controls may be defined, but without a system to track ownership, monitor execution, and consolidate evidence, consistency breaks down under audit pressure.
A more sustainable approach connects regulatory requirements, control execution, and evidence into a single operational layer.
How ComplianceOps supports structured execution
- Centralized control tracking and task ownership
Assign, monitor, and track compliance tasks across teams with clear accountability, ensuring controls are consistently executed and not lost across functions - Always audit-ready evidence and documentation
Store and link evidence directly to controls and activities, with complete audit trails and version-controlled records available on demand - Real-time visibility through dashboards and reporting
Track compliance status, control performance, and gaps through centralized dashboards, enabling leadership to assess posture without manual consolidation - Automated workflows and continuous monitoring
Replace manual coordination with automated workflows, alerts, and real-time tracking to ensure compliance activities remain consistent as systems scale
This shifts compliance from fragmented execution to a structured system where controls are enforced, ownership is visible, and evidence is continuously available.
Book a demo to see how it enables consistent execution, centralized visibility, and audit-ready evidence without reactive effort.
Conclusion
Data protection compliance is ultimately tested in execution, whether controls are consistently applied, monitored, and evidenced across systems without disruption. As regulatory expectations continue to focus on accountability and traceability, programs that rely on periodic reviews or manual coordination struggle to maintain consistency under scrutiny. The shift toward continuous oversight is not a matter of optimization, but of maintaining control in environments where data movement and regulatory obligations are constantly evolving.
Sustaining this level of discipline requires more than defined policies or mapped frameworks; it depends on structured governance systems that connect requirements, controls, and evidence into a single, reliable operating model. Understand how ComplianceOps supports continuous compliance oversight, enabling organizations to maintain control and visibility, enforce accountability, and stay audit-ready as regulatory demands evolve.
Start a 21-day free trial.
FAQs
It is the ability to enforce and demonstrate how data is handled in line with regulatory requirements. This includes applying controls over access, storage, sharing, and retention, and maintaining clear evidence that these controls are working when reviewed.
Requirements depend on the type of data handled. Common regulations include HIPAA (health data), GLBA (financial data), and CCPA/CPRA (consumer data). Many organizations must align with multiple regulations at once, especially when operating across states or industries.
Most regulations focus on personally identifiable information (PII) and sensitive data such as health, financial, or identity-related information. Organizations must map where this data exists, how it is processed, and which controls apply at each stage of its lifecycle.
Failures usually stem from inconsistent execution rather than missing policies. Common issues include incomplete access reviews, lack of centralized evidence, and difficulty demonstrating control effectiveness across systems and vendors.
Effective programs move beyond documentation and embed controls into workflows, with continuous monitoring and evidence collection. Structured systems that connect regulatory requirements, control execution, and reporting—such as VComply—help maintain visibility, accountability, and audit readiness without relying on manual effort.

