Understanding AML Transaction Monitoring Processes
US financial institutions are moving away from traditional, rigid rules that often trigger unnecessary flags. The current focus has shifted toward a more flexible approach to AML monitoring, one that evaluates the actual risk a customer presents rather than just the dollar amount of a single transaction.

This change is creating a significant operational challenge: systems must now process high volumes of data in real-time while maintaining the accuracy needed for serious investigations. Relying on older, manual processes is no longer practical when faced with the speed and complexity of modern financial activity.
Success in this environment depends on a disciplined workflow that connects the dots between different types of data. A well-structured approach to AML monitoring does more than just spot errors; it provides the clarity needed to make fast, confident decisions that protect the organization from oversight failures.
Key Takeaways
- Batch processing is being phased out in favor of real-time AML monitoring to intercept illicit fund movements before they exit the system.
- Modern programs focus on reducing false positives through refined thresholds and behavioral profiling rather than simply increasing the number of alerts.
- The Anti-Money Laundering Act of 2020 (AMLA) continues to drive the move toward a risk-based approach, prioritizing national security threats such as cybercrime and fentanyl-related trafficking.
- Effective monitoring requires the integration of KYC, beneficial ownership data, and transaction history to create a holistic view of customer risk.
What is AML Transaction Monitoring?
Transaction monitoring is the continuous process of reviewing a customer’s financial activity to identify patterns that may indicate money laundering, terrorist financing, or other financial crimes. For US institutions, this process is governed by the Bank Secrecy Act (BSA) and the subsequent mandates of the Patriot Act and the AML Act of 2020.
In 2026, the definition of AML monitoring has expanded beyond simple cash transactions. It now encompasses a vast array of digital assets and cryptocurrency exchanges, cross-border wires, and complex, layered transfers involving multiple entities. The goal is to move beyond flagging isolated large deposits and instead identify the behavioral red flags that signal criminal intent.
What is the Main Objective of a Mature AML Program?
The ultimate objective is to provide law enforcement with high-quality, actionable intelligence. It ensures that every SAR (Suspicious Activity Report) filed contains the necessary context to assist FinCEN in its mission to safeguard the financial system.
Achieving this level of maturity requires a shift from a manual, checklist-driven approach to an automated, analytical framework that can distinguish between legitimate business growth and suspicious anomalies. This transition to an analytical framework is best executed through a structured, five-stage workflow.
Also Read: 7 Roles and Responsibilities of an AML Compliance Officer
How Does the AML Transaction Monitoring Process Work?
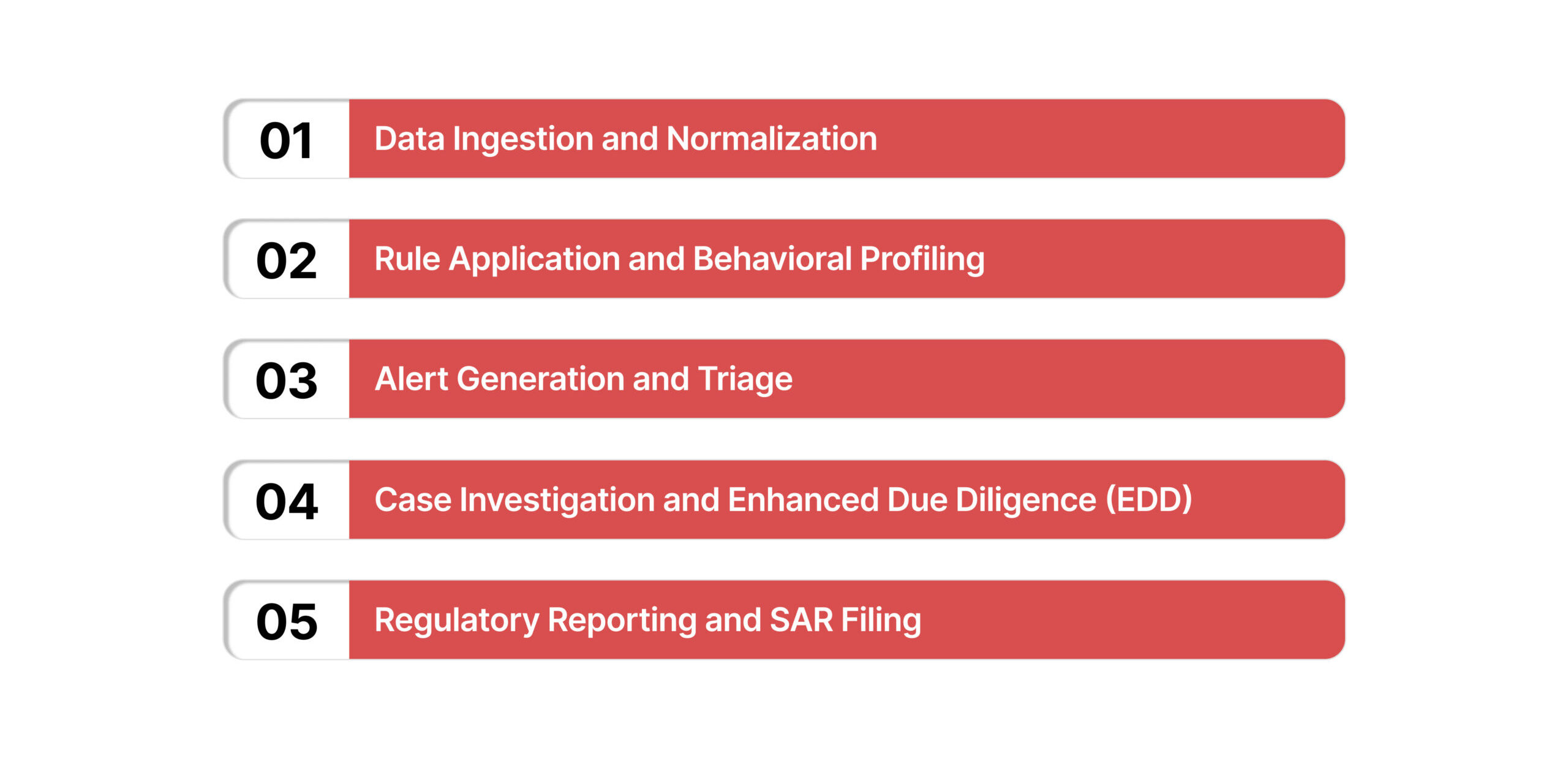
Operationalizing a risk-based approach requires a structured workflow that moves from raw data ingestion to regulatory reporting. This five-stage process provides the framework for defensible oversight.
1. Data Ingestion and Normalization
The foundation of any AML monitoring system is the quality of the data it receives. This stage involves pulling information from various sources, including core banking systems, payment gateways, and KYC databases.
In 2026, normalization is critical because institutions must consolidate data from disparate channels, such as mobile apps, branches, and third-party fintech partners, into a unified format.
2. Rule Application and Behavioral Profiling
Once the data is normalized, it is processed through a series of detection rules. These rules are designed based on known money laundering typologies. However, modern systems also incorporate behavioral profiling.
By establishing a baseline for a customer’s normal activity, the system can detect deviations that may not trigger a standard threshold rule but still represent a significant risk.
For example, a sudden increase in the frequency of international transfers for a locally focused small business would be flagged as an anomaly, even if the individual amounts remain low.
3. Alert Generation and Triage
When a transaction or pattern violates a rule or deviates from a profile, the system generates an alert. Triage is the process of sorting these alerts based on their risk level. High-priority alerts, such as those involving sanctioned jurisdictions or Politically Exposed Persons (PEPs), receive immediate attention, while lower-risk alerts are assigned for routine review.
4. Case Investigation and Enhanced Due Diligence (EDD)
During the investigation phase, compliance analysts review the context of the flagged activity. This often involves performing Enhanced Due Diligence (EDD) to verify the source of funds and the purpose of the transaction.
Analysts look for the following specific red flags:
- Layering: Moving funds through multiple accounts to obscure their origin.
- Structuring: Breaking down large cash deposits into smaller amounts to evade reporting limits.
5. Regulatory Reporting and SAR Filing
If the investigation confirms that the activity is suspicious and has no clear legal or business justification, the institution must file a SAR.
While automated filing systems have simplified the submission process, the burden remains on the institution to provide a clear narrative that explains the “who, what, when, where, and why” of the suspicious behavior.
Suggested Read: Master AML Data Today and Learn Best Practices to Strengthen Compliance
What are the Common AML Scenarios and Suspicious Typologies in 2026?
Criminal organizations continuously adapt their methods to bypass traditional controls. For a US-based financial institution, an effective AML monitoring system must be specifically calibrated to detect several high-risk scenarios:
Structuring and Smurfing
Structuring remains a primary method for evading the $10,000 Currency Transaction Report (CTR) threshold. Smurfing is a more complex version where multiple individuals make small deposits into various accounts, which are then consolidated.
A mature monitoring system identifies these patterns by looking for clusters of transactions occurring across different branches or digital wallets within a short period.
Layering Through Shell Companies
Layering creates a complex web of transactions to obscure the original source of funds. In 2026, this often involves the use of “shell companies”, entities with no active business operations.
Effective monitoring requires integration with the FinCEN Beneficial Ownership Registry to identify the individuals who actually control these companies, regardless of how many layers of ownership are created.
Rapid Fund Movement
High-velocity fund movement is a significant red flag. This occurs when an account receives a large deposit and immediately transfers it to another entity, often in a different jurisdiction.
This behavior is typical of money mules or accounts used to facilitate cybercrime. Monitoring rules must track the velocity of funds to flag accounts serving as temporary conduits rather than stable repositories of wealth.
High-Risk Jurisdictions and Sanctions
Transactions involving countries known for weak AML controls or those subject to US sanctions require the highest level of scrutiny.
In 2026, these lists are updated frequently, and a mature AML monitoring program must feature real-time integration with OFAC and other federal watchlists to prevent the movement of illicit capital.
Identifying these complex patterns is a significant technical hurdle, but the subsequent investigative process often creates the most operational friction. Organizations can evaluate how CaseOps structures these AML alert workflows, ensuring that every investigation is documented and resolved within a defensible, centralized system.
How Do the BSA and AML Act of 2020 Govern Transaction Monitoring?
The regulatory framework for AML monitoring in the United States is anchored in the Bank Secrecy Act (BSA) and significantly expanded by the Anti-Money Laundering Act of 2020 (AMLA). These statutes mandate that institutions move beyond passive reporting and into active, intelligence-led oversight.
The Mandate for Risk-Based Programs
The AML Act of 2020 explicitly requires financial institutions to implement “reasonably designed risk-based programs.” This means that the level of monitoring must be proportional to the risks posed by the institution’s specific products, customers, and geographic reach.
A one-size-fits-all approach is no longer sufficient; a small credit union in the Midwest will have different monitoring priorities than a large international bank in New York.
The Role of National AML/CFT Priorities
Under the AML Act, the Treasury Department has established specific national priorities that every AML monitoring program must incorporate. These priorities demand that AML monitoring systems be specifically tuned to detect:
- Corruption: Identifying funds related to foreign or domestic bribery.
- Cybercrime: Monitoring for ransomware payments and the proceeds of digital fraud.
- Fentanyl and Drug Trafficking: Detecting the financial footprints of transnational criminal organizations involved in the narcotics trade.
- Human Trafficking: Spotting transaction patterns that indicate the exploitation of vulnerable individuals.
The Corporate Transparency Act (CTA)
A critical component of the AMLA, the Corporate Transparency Act, requires businesses to report beneficial ownership information to FinCEN. For financial institutions, this data is a vital verification tool, ensuring that the person conducting a transaction is the actual owner rather than a front for a criminal enterprise.
How to Overcome the Operational Challenges of Transaction Monitoring?
The primary hurdle in modern compliance is not a lack of data, but the inability to discern legitimate business growth from suspicious activity. When systems are tuned too broadly, they generate an unmanageable volume of alerts, forcing analysts to spend more time clearing “noise” than investigating actual threats.
Avoiding the “One Size Fits All” Trap
Many false positives occur because institutions apply the same thresholds to all customers. A $9,500 cash deposit from a retail business is normal; the same deposit from a student is suspicious.
Mature programs implement customer segmentation, applying monitoring rules that align with an entity’s expected behavior and risk profile rather than applying blanket triggers across the entire database.
Bridging Data Silos
If the monitoring system lacks access to KYC or source-of-wealth data, analysts are forced to manually correlate disparate information, leading to slower decision-making.
Integrating these data layers is essential for providing analysts with the context needed to confirm or dismiss alerts rapidly.
Also Read: Why “AML on Paper” No Longer Satisfies Regulators
Managing AML Investigations with CaseOps
The effectiveness of an AML monitoring program depends on how an institution handles the transition from a flagged alert to a final resolution. CaseOps provides the structure needed to manage these investigations within a unified environment, ensuring every case is resolved with precision and accountability.
How CaseOps supports AML investigations:
- Centralized Evidence Management: Store KYC data, transaction records, and analyst notes in one location to eliminate fragmented data silos.
- Consistent Workflow Enforcement: Apply standardized investigative steps to ensure every alert is triaged and documented according to your risk policy.
- Automated Audit Trails: Capture every action and escalation in a time-stamped log to provide the transparency required for regulatory examinations.
- Collaborative Case Resolution: Assign tasks and share insights across teams to resolve complex alerts and prepare for SAR filings.
A structured investigative workflow ensures that every AML alert is reviewed, documented, and resolved according to internal and federal standards.
Wrapping Up
As the US financial sector addresses increasingly sophisticated threats in 2026, the maturity of an AML monitoring program serves as a primary indicator of institutional stability. Meeting the rigorous mandates of the BSA and the AML Act of 2020 requires a transition from manual, administrative oversight to a strategically integrated, data-driven framework.
By prioritizing data quality, rule precision, and investigative efficiency, institutions move beyond basic detection to achieve a defensible, risk-based program. This structural discipline ensures the organization remains resilient against evolving financial crimes while satisfying federal expectations for transparency and accountability.
Book a demo to see how VComply’s CaseOps provide the structure needed to manage modern AML investigations and oversight.
Frequently Asked Questions (FAQs)
An AML rule is a static threshold, such as “Flag any cash deposit over $9,999.” A behavioral profile is a dynamic baseline of a customer’s normal activity.
Profiles are often more effective because they can detect anomalies, such as a sudden change in transaction frequency, that may not trigger a specific dollar-amount rule but indicate a change in risk.
In 2026, rules should be reviewed at least quarterly, or immediately following the detection of a new money laundering typology or a change in federal law. Static rules quickly become obsolete as criminals adapt their methods to avoid detection.
Not necessarily. A SAR is only required when an institution has “reason to suspect” that a transaction involves criminal proceeds or is intended to hide them. The investigation phase is critical for determining if a seemingly unusual transaction has a legitimate business explanation.
Under the BSA and the AML Act of 2020, the penalties are severe. Financial institutions can face fines in the millions of dollars, and individual executives can be held personally liable and face prison terms for “willful” violations of reporting requirements.
VComply provides examiners with a centralized record of an institution’s compliance framework. It provides a time-stamped history of policies, monitoring results, and investigative documentation. This transparency allows you to demonstrate that your program is not only active but also consistently governed and documented.

