15 HIPAA Violation Examples That Highlight Real-World Compliance Failures
Healthcare organizations rarely face enforcement because policies are missing. Enforcement actions usually occur because controls fail in practice, evidence cannot be produced, or accountability remains unclear across departments.

Hospitals, clinics, insurers, and healthcare technology vendors often maintain extensive policy documentation aligned with HIPAA requirements. However, regulators increasingly examine whether safeguards operate consistently, whether risk assessments occur regularly, and whether remediation efforts are documented.
This guide reviews fifteen HIPAA violation examples that resulted in regulatory penalties and explains how healthcare organizations can prevent similar failures through structured governance and oversight.
Quick Look
- Most HIPAA violations occur when documented safeguards fail operationally rather than when policies are completely absent.
- Many enforcement actions involve access control failures, unencrypted devices, or improper disclosure of protected health information.
- Weak documentation and missing evidence frequently worsen enforcement outcomes during investigations.
- Organizations that rely on spreadsheets struggle to track remediation ownership and audit evidence across departments.
- Structured oversight systems improve accountability by connecting policies, risks, and remediation activities in one environment.
- Continuous monitoring and centralized compliance tracking significantly reduce the likelihood of recurring violations.
What Is a HIPAA Violation?
A HIPAA violation occurs when an organization fails to protect protected health information according to the requirements established under the Health Insurance Portability and Accountability Act. Violations may involve unauthorized access, improper disclosure, insufficient safeguards, or failure to conduct risk assessments.
Enforcement authority rests with the U.S. Department of Health and Human Services Office for Civil Rights, which investigates complaints and may impose financial penalties or corrective action plans.
Also Read: How to Develop Corporate Governance Policies
Common Types of HIPAA Violations Organizations Must Watch
HIPAA violations rarely occur as isolated incidents. They typically follow repeatable patterns tied to weak controls, inconsistent oversight, or gaps in day-to-day execution.
Understanding these patterns helps compliance teams identify where breakdowns are most likely to occur and what needs to be strengthened operationally.
1. Unauthorized Access to Patient Records
One of the most frequent violations involves employees accessing patient records without a valid clinical or operational reason. These incidents often occur due to curiosity, lack of monitoring, or weak access controls.
In many enforcement cases, organizations had role-based access policies in place but failed to actively monitor audit logs or flag unusual access behavior.
2. Lost or Stolen Devices Containing PHI
Unencrypted laptops, mobile devices, or storage media continue to be a major source of HIPAA violations. When devices are lost or stolen, patient data becomes exposed if proper safeguards are not in place.
These incidents usually point to gaps in device management policies, encryption enforcement, and asset tracking systems.
3. Improper Disposal of Patient Information
Healthcare organizations sometimes discard physical records or electronic media without secure destruction processes. Investigations have uncovered patient records in dumpsters, recycling bins, or unsecured storage areas.
This type of violation reflects failures in records management policies and lack of oversight in disposal procedures.
4. Inadequate Risk Assessments
HIPAA requires regular risk assessments, yet many organizations either skip them or perform them inconsistently. Without ongoing risk analysis, vulnerabilities remain unidentified and unaddressed.
Regulators frequently cite missing or outdated risk assessments as a foundational compliance failure.
5. Weak Access Controls and Credential Management
Shared logins, excessive user privileges, or lack of multi-factor authentication create conditions for unauthorized access.
These violations often indicate that access governance exists on paper but is not enforced consistently across systems.
6. Improper Disclosure to Third Parties
Patient information is sometimes shared with vendors, partners, or external parties without proper authorization or safeguards.
In many cases, organizations fail to establish or maintain Business Associate Agreements, leading to compliance exposure.
7. Unsecured Communication of Patient Data
Sending protected health information through unencrypted email or messaging systems remains a common issue.
Even when secure tools are available, inconsistent usage across teams leads to avoidable data exposure.
8. Delayed Breach Notification
Organizations are required to notify affected individuals and regulators within specific timeframes after a breach.
Delays often occur due to unclear incident response processes or a lack of coordination between legal, compliance, and IT teams.
9. Insufficient Workforce Training
Employees may unintentionally violate HIPAA when they are not adequately trained on handling patient data.
Common issues include misdirected emails, inappropriate conversations, or improper use of systems containing protected health information.
10. Poor Vendor Risk Management
Third-party vendors frequently handle sensitive data, but many organizations fail to assess or monitor vendor compliance practices.
Regulatory investigations often reveal that vendor oversight is either inconsistent or entirely absent.
Also Read: Understanding Regulatory Compliance Management in the U.S.
15 HIPAA Violation Examples That Led to Regulatory Penalties
Real enforcement actions illustrate how operational failures create compliance exposure. The following examples highlight common control breakdowns observed during regulatory investigations.
These HIPAA violation examples demonstrate how seemingly small gaps can escalate into major enforcement actions:
1. Unauthorized Employee Access to Patient Records

Healthcare employees sometimes access patient records without a treatment, payment, or operational reason. These incidents often involve staff viewing records of colleagues, relatives, or public figures out of curiosity. Regulators consider this a violation of HIPAA’s minimum necessary requirement.
These cases typically reveal weak access monitoring or insufficient workforce oversight.
Tip to prevent this violation:
Implement role-based access controls and monitor audit logs that flag unusual record access patterns for compliance review.
Case Study:
In 2008, 13 UCLA Medical Center employees were fired and 6 physicians suspended for snooping on Britney Spears’s medical records without authorization or consent, violating patient privacy rules.
2. Lost or Stolen Unencrypted Devices
Many enforcement actions involve laptops, portable drives, or mobile devices containing patient information that were lost or stolen. When these devices lack encryption, unauthorized parties may access patient data.
Regulators frequently determine that encryption could have prevented the breach.
Tip to prevent this violation:
Require device-level encryption and maintain a centralized inventory of all hardware storing protected health information.
Case Study:
Children’s Medical Center in Dallas lost 3,800 PHI records from a stolen unencrypted BlackBerry without password protection, leading to a $3.2M penalty for inadequate device safeguards.
3. Improper Disposal of Patient Records
Healthcare organizations sometimes discard medical records or electronic storage media without secure destruction. Investigators have found patient files in dumpsters, recycling containers, or unsecured storage facilities.
Such incidents demonstrate failures in physical safeguards and records management.
Tip to prevent this violation:
Establish secure disposal policies and document destruction using certified shredding vendors or approved electronic media destruction processes.
Case Study:
Cornell Prescription Pharmacy improperly disposed of PHI for 1,610 patients, lacking secure policies, resulting in a $125,000 settlement and corrective action plan.
4. Misconfigured Cloud Storage Systems
Healthcare providers increasingly store data in cloud platforms. Misconfigured storage systems may expose patient records publicly or allow unauthorized access.
Several enforcement cases have resulted from improperly configured databases or file storage services.
Tip to prevent this violation:
Conduct routine cloud configuration audits and implement automated monitoring to detect publicly exposed storage systems.
5. Failure to Conduct a HIPAA Risk Assessment
HIPAA requires organizations to evaluate risks to patient data regularly. Some organizations fail to conduct formal risk assessments or update assessments when systems change.
Regulators frequently cite this failure during enforcement actions.
Tip to prevent this violation:
Perform documented risk assessments annually and track remediation activities through structured compliance workflows.
Case Study:
Alaska DHSS paid $1.7M in 2012 for lacking risk analysis and security protocols to protect PHI, exposing vulnerabilities across systems.
6. Inadequate Workforce Training
Employees may unintentionally disclose patient information when they lack adequate HIPAA training. Improper conversations, misdirected emails, or incorrect handling of medical records often result from insufficient workforce awareness.
Training deficiencies often appear during regulatory investigations.
Tip to prevent this violation:
Maintain recurring HIPAA training programs and track workforce training completion with documented compliance records.
7. Improper Disclosure to Third Parties
Healthcare organizations sometimes share patient information with vendors or external partners without proper authorization or contractual safeguards.
These incidents typically involve missing business associate agreements or poorly defined vendor responsibilities.
Tip to prevent this violation:
Maintain documented business associate agreements and review vendor access permissions regularly.
Case Study:
Manasa Health Center disclosed a patient’s PHI in response to a negative online review, violating privacy rules and lacking proper policies, settling for $30,000.
8. Weak Access Control Policies
Shared login credentials or poorly managed user privileges create opportunities for unauthorized system access. Regulators frequently identify these weaknesses during security reviews.
Weak access governance increases the likelihood of internal data misuse.
Tip to prevent this violation:
Require unique user credentials and enforce multi-factor authentication for systems containing protected health information.
Case Study:
Dr. H accessed patient records without authorization during his notice period out of curiosity about celebrities and colleagues, resulting in 4 months’ jail and $2,000 fine.
9. Sending Patient Information Through Unsecured Email
Employees sometimes send patient information through standard email channels without encryption. These communications may expose sensitive data if intercepted.
HIPAA enforcement actions have occurred when organizations failed to secure electronic communication methods.
Tip to prevent this violation:
Implement encrypted email systems or secure messaging platforms for patient-related communication.
Case Study:
Lanap & Dental Implants posted 11,000 unencrypted dental records on a torrent site for 4 years, accessible to anyone with basic skills, breaching secure sharing rules.
10. Failure to Maintain Audit Logs
Organizations must track access to patient information through system logs. When audit logs are absent or not reviewed, unauthorized access may go undetected.
Regulators consider missing audit logs a serious compliance weakness.
Tip to prevent this violation:
Deploy automated logging systems and conduct periodic reviews of system activity reports.
11. Delayed Breach Notification
HIPAA requires organizations to notify affected individuals and regulators promptly when breaches occur. Some organizations delay notifications while attempting internal investigations.
Regulators frequently impose penalties when notification timelines are not met.
Tip to prevent this violation:
Maintain an incident response plan that defines breach notification timelines and escalation procedures.
Case Study:
OSU-CHS delayed notifying 279,865 affected individuals and HHS about a 2016 breach discovered in 2018, paying $875,000 plus two-year monitoring.
12. Poor Vendor Risk Management
Third-party vendors often store or process patient information. When healthcare organizations fail to evaluate vendor safeguards, sensitive information may be exposed.
Regulatory investigations frequently reveal inadequate vendor oversight practices.
Tip to prevent this violation:
Conduct periodic vendor risk assessments and monitor vendor compliance obligations.
Case Study:
33 top U.S. hospitals used Meta Pixel trackers, sending PHI like appointments and conditions to Facebook via IP addresses, risking HIPAA violations.
13. Improper Social Media Disclosures
Healthcare staff occasionally post patient-related information on social media platforms without authorization. Even indirect references to identifiable information can violate HIPAA rules.
These incidents typically result from weak policy enforcement.
Tip to prevent this violation:
Implement clear social media policies and reinforce patient confidentiality obligations during employee training.
14. Weak Physical Security Controls
Unauthorized individuals may access workstations, medical records, or storage systems when physical safeguards are insufficient. Examples include unattended computers or unsecured storage rooms.
Such incidents indicate failures in facility access controls.
Tip to prevent this violation:
Use badge-based facility access systems and require automatic workstation locking when devices remain unattended.
15. Inadequate Incident Response Procedures
Organizations sometimes detect potential privacy incidents but lack structured processes for investigation and remediation. This delays response efforts and weakens compliance evidence.
Regulators often view weak incident response processes as governance failures.
Tip to prevent this violation:
Maintain documented incident response procedures and track investigations through structured case management workflows.
Case Study:
UMMC ignored known risks to 10,000 individuals’ ePHI, failed notifications, and lacked response, settling for $2.75M after breaches.
Also Read: Your Guide to Major Life Science Compliance Risks
When HIPAA violations occur, tracking obligations and safeguards across departments becomes difficult. See how ComplianceOps supports structured compliance oversight. Book a demo with VComply to control accountability across healthcare organizations.
The Most Common Causes Behind HIPAA Violations in Healthcare Organizations
While violations vary widely, several patterns appear repeatedly across enforcement actions. Understanding these root causes helps compliance leaders strengthen oversight structures.
The following operational weaknesses frequently contribute to HIPAA violations:
- Inadequate Access Governance: Many organizations lack clear processes for managing user access privileges, increasing the likelihood of unauthorized record access.
- Poor Documentation of Compliance Activities: When evidence of risk assessments or training programs is missing, organizations struggle to demonstrate compliance during regulatory investigations.
- Weak Vendor Oversight: Healthcare providers frequently rely on third parties without monitoring how vendors handle patient data.
- Fragmented Compliance Tracking: When policies, risks, and remediation tasks remain scattered across departments, oversight becomes inconsistent.
When compliance tracking relies on spreadsheets or disconnected systems, visibility into remediation ownership and evidence quickly breaks down. Explore how ComplianceOps structures compliance obligations, remediation tasks, and audit evidence within a centralized governance system. Book a demo with VComply to learn more.
HIPAA Violation Fines and Penalties
HIPAA violations can lead to significant financial penalties depending on the severity of the violation and the level of negligence involved. The U.S. Department of Health and Human Services Office for Civil Rights enforces penalties through a tiered structure that considers intent, corrective action, and the organization’s compliance history.
HIPAA violation penalties can range from hundreds to tens of thousands of dollars per violation, with annual caps reaching into the millions. In severe cases involving willful neglect or deliberate misuse of patient information, criminal charges and imprisonment may also apply.
Key HIPAA Requirements Healthcare Organizations Must Operationalize
HIPAA establishes several core requirements that organizations must translate into operational safeguards. These requirements form the foundation of healthcare compliance programs.
Healthcare organizations must operationalize the following controls:
- Administrative Safeguards: Organizations must implement policies governing workforce training, risk assessments, and incident response procedures.
- Technical Safeguards: Systems must include encryption, access controls, and monitoring capabilities that protect patient information.
- Physical Safeguards: Facilities must implement security controls that prevent unauthorized access to equipment or records containing protected information.
- Breach Notification Procedures: Organizations must detect breaches quickly and notify affected individuals within defined timelines.
How to Conduct a HIPAA Compliance Gap Assessment
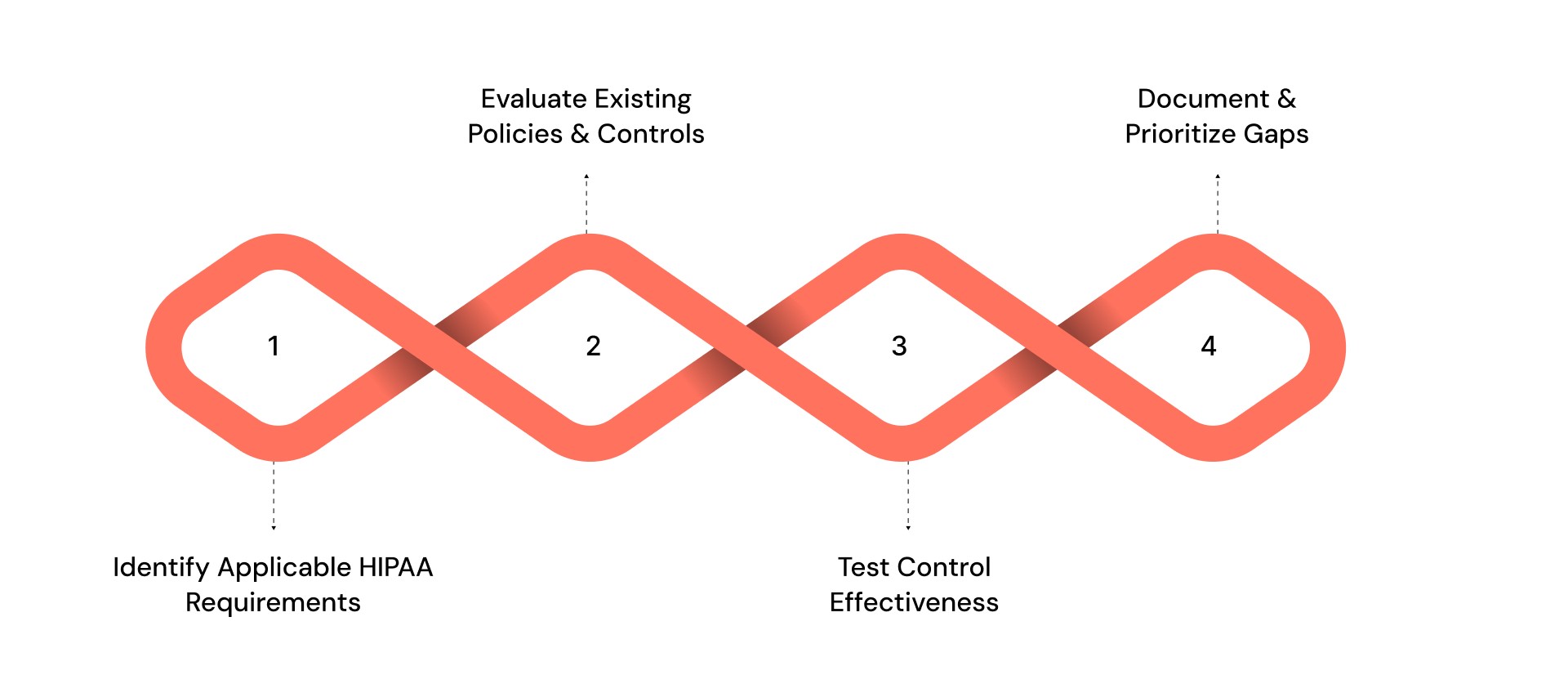
Healthcare organizations should regularly evaluate their compliance posture to identify weaknesses before regulators do. A structured gap assessment helps identify missing controls and prioritize remediation efforts.
Conduct a HIPAA compliance gap assessment using the following steps:
1. Identify Applicable HIPAA Requirements
Review privacy, security, and breach notification rules to determine which requirements apply to your organization.
- Compile a complete regulatory inventory
- Confirm obligations across departments
- Document responsibility assignments
2. Evaluate Existing Policies and Controls
Assess whether documented safeguards exist and whether they operate consistently across the organization.
- Review policy documentation
- Interview key stakeholders,
- analyze system configurations
3. Test Control Effectiveness
Determine whether safeguards function properly and produce verifiable evidence.
- Review training records
- examine audit logs
- validate encryption implementation
4. Document and Prioritize Gaps
Create a remediation plan that addresses high-risk deficiencies first.
- Assign remediation owners
- establish deadlines
- track progress consistently
Operationalizing HIPAA Compliance With Centralized Governance
Healthcare organizations often attempt to manage HIPAA obligations through spreadsheets, email reminders, and disconnected documentation repositories. As regulatory expectations expand, this fragmented approach makes it difficult to maintain visibility across policies, risks, and remediation tasks.
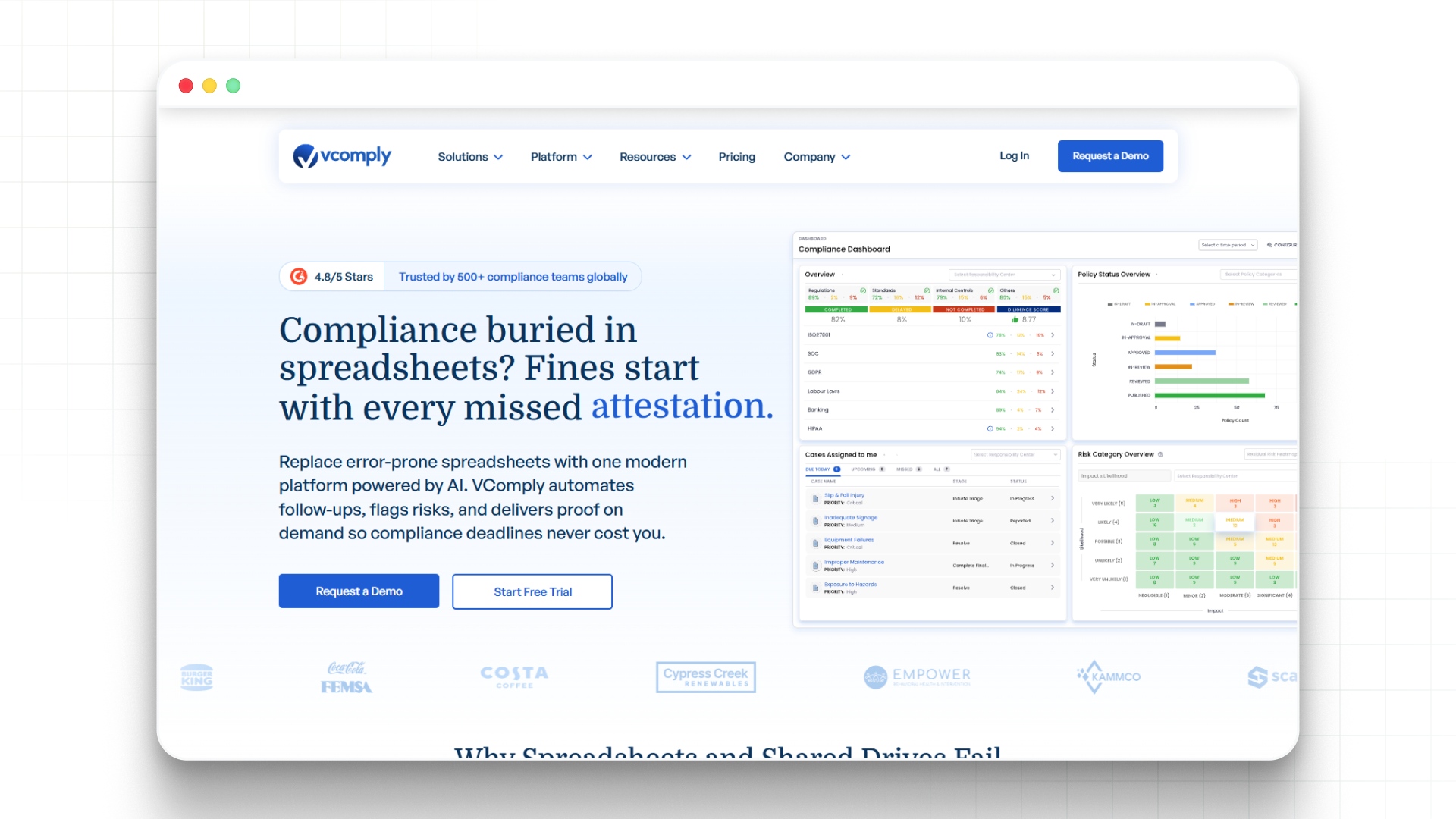
VComply provides a structured governance environment that centralizes compliance oversight within a unified platform. By connecting compliance activities across departments, healthcare organizations gain consistent visibility into regulatory obligations and remediation progress.
Within this environment:
- ComplianceOps tracks HIPAA obligations, assigns compliance tasks with due dates, and maintains audit-ready documentation across departments.
- RiskOps identifies risk exposures related to patient data protection and provides dashboards for leadership oversight.
- PolicyOps manages policy development, approvals, and employee attestation workflows aligned with HIPAA requirements.
- CaseOps enables structured incident tracking and resolution workflows when potential privacy violations occur.
Book a demo with VComply to learn how this integrated model helps organizations maintain continuous oversight instead of reacting only when regulators initiate investigations.
Conclusion
HIPAA violation examples reveal a consistent pattern across enforcement actions. Most penalties occur when operational controls fail, documentation remains incomplete, or oversight structures cannot demonstrate accountability.
Healthcare organizations reduce regulatory exposure by implementing structured governance processes that connect policies, risks, incidents, and remediation activities across departments.
See how ComplianceOps supports continuous HIPAA oversight and compliance tracking. Start a 21-day free trial of VComply to evaluate structured governance across your healthcare compliance program.
FAQs
Common violations include unauthorized access to patient records, lost devices containing patient data, failure to conduct risk assessments, and improper disclosure of protected health information.
The U.S. Department of Health and Human Services Office for Civil Rights investigates complaints, breach reports, and compliance failures to determine whether penalties or corrective action plans are necessary.
Healthcare organizations reduce risk by implementing strong access controls, conducting regular risk assessments, training employees, and maintaining documented compliance processes.
Many healthcare organizations centralize compliance tracking, risk monitoring, and remediation workflows through structured governance platforms such as VComply, reducing manual coordination across departments.
Unauthorized access to patient records is one of the most frequently reported HIPAA violations. These incidents usually occur when employees view medical records without a valid clinical or operational reason. Weak access controls and insufficient monitoring systems often allow such violations to occur. Regular access reviews, role-based permissions, and activity monitoring help organizations reduce this risk.

