Understanding FISMA Compliance: Requirements and Best Practices
When you’re responsible for safeguarding sensitive systems, risk rarely shows up as a headline breach; it lurks in missed controls, outdated inventories, and gaps auditors spot first. Too often, compliance teams act only when audits loom or federal contracts are at stake.

A 2024 GAO study found that only 8 of 23 civilian agencies had effective FISMA programs, showing that even well-resourced teams struggle with daily risk governance. For healthcare, finance, energy, manufacturing, and higher education, this means Monday-morning scrambles, last-minute control updates, and the blind spots auditors always notice.
In this blog, we will walk you through what FISMA compliance really requires, its core controls, and best practices to make your program resilient and audit-ready.
Key Takeaways
- FISMA compliance is continuous, risk‑based governance, not a one‑time audit, linking risk management to federal expectations and ongoing monitoring.
- Structured documentation and evidence aligned with NIST SP 800‑53 ensure audit readiness.
- Centralized tracking with VComply reduces manual effort, bridges team gaps, and enhances preparedness across healthcare, finance, energy, education, and manufacturing.
- Consistent compliance lowers breach risk, streamlines audits, and strengthens trust, while fragmented spreadsheets hinder scale.
- Operational platforms provide real‑time visibility, evidence management, and audit readiness.
Did you know?
In the U.S. Department of Health and Human Services’ (HHS) FY 2024 FISMA audit, the agency’s overall information security program was rated “Not Effective”, the same outcome as the prior year, showing that even major federal departments struggle with baseline compliance maturity under FISMA. This highlights that FISMA isn’t just theoretical governance: it directly affects how federal systems are rated for risk, maturity, and audit readiness.
What Is FISMA Compliance and What Does It Require of Organizations?
FISMA compliance involves creating a disciplined information security program that protects federal systems and data, enforces accountability and risk ownership, and emphasizes continuous security rather than one-time certification.
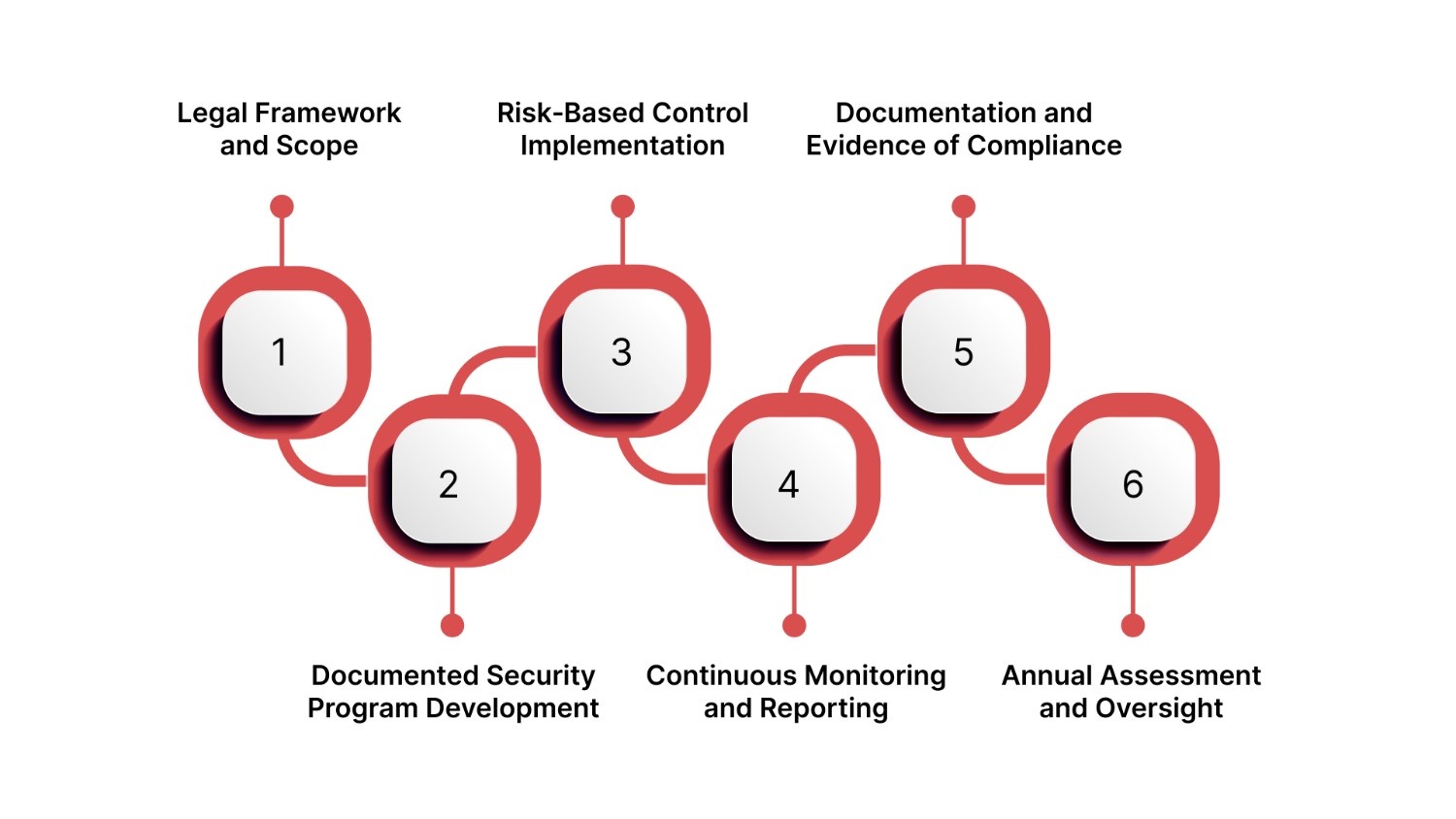
Below are the key elements that define what FISMA compliance requires:
- Legal Framework and Scope: FISMA (Federal Information Security Modernization Act) is a U.S. federal law mandating agencies and certain contracted organizations to establish structured information security programs to safeguard government information and operations.
- Documented Security Program Development: Organizations must develop, document, and implement a comprehensive security program grounded in risk management that spans people, processes, and technology.
- Risk‑Based Control Implementation: Select and implement security controls based on risk impact, using NIST standards such as the Risk Management Framework and SP 800‑53 as guiding frameworks.
- Continuous Monitoring and Reporting: Maintain ongoing monitoring of systems to detect vulnerabilities, assess control effectiveness, and update risk posture dynamically, not just annually.
- Documentation and Evidence of Compliance: Keep updated security plans, assessment results, system inventories, and monitoring outcomes to demonstrate compliance readiness at any time.
- Annual Assessment and Oversight: Conduct annual assessments and report findings to oversight bodies (such as OMB and inspectors general) to show measurable improvement and accountability.
Also Read: Understanding the Cost of PCI Compliance
Understanding these requirements is easier when you see the history and purpose behind FISMA, which set the foundation for modern federal information security.
Why FISMA Was Introduced and How It Shapes Federal Data Security Today
The U.S. Congress enacted FISMA (modernized under FISMA 2014) to address decades of inconsistent federal information security. Before FISMA, agencies lacked standardized risk governance, leaving sensitive systems vulnerable and oversight fragmented.
Below are the key drivers and impacts behind FISMA’s introduction:
- Standardize Security Practices Across Agencies: FISMA created consistent security programs, defining roles for agency heads, CIOs, and Inspectors General to close gaps in risk assessments, documentation, and accountability.
- Shift From Reactive to Proactive Risk Management: It shifted federal cybersecurity from reactive incident response to continuous risk assessment, monitoring, and mitigation.
- Foundation for Modern Federal Cybersecurity Programs: FISMA institutionalized risk-based policies and controls with reporting requirements, shaping today’s structured federal cybersecurity programs and frameworks.
- Industry Reinforcement Through High‑Profile Breaches: High-profile incidents, such as the 2023 CFPB financial data breach, highlight the ongoing need for disciplined information security and risk governance in federal and affiliated entities.
When FISMA requirements live across spreadsheets, emails, and disconnected tools, compliance becomes reactive and fragile. VComply’s ComplianceOps centralizes FISMA requirements, maps NIST controls to systems, and keeps evidence continuously updated.
Understanding these requirements is easier when you see the history and purpose behind FISMA, which set the foundation for modern federal information security.
Who Needs to Be FISMA Compliant Across Government, Contractors, and Regulated Industries
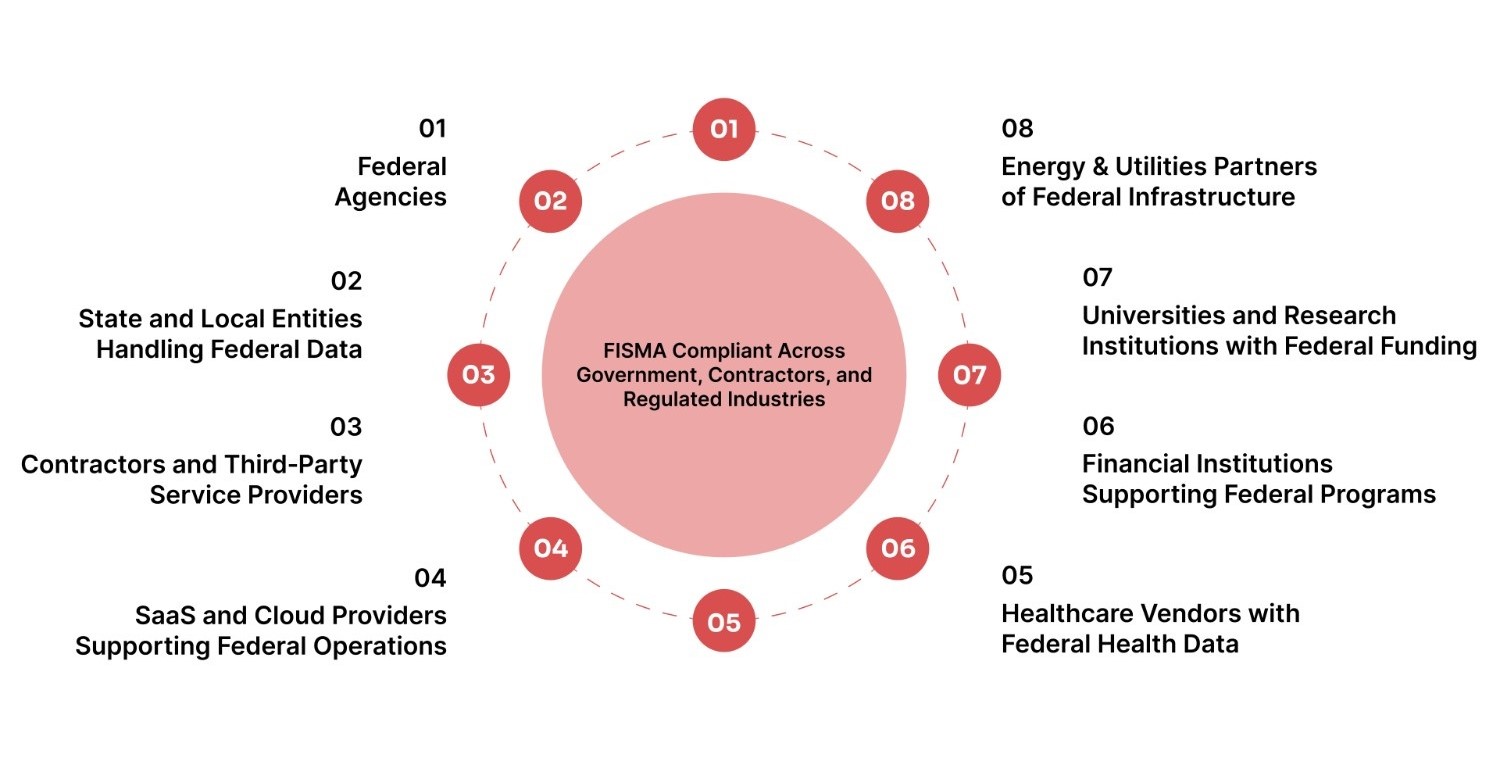
Determining if FISMA applies is critical for compliance officers, risk managers, CTOs, and CEOs, especially when handling federal data, systems, or funding. Its scope includes not only federal agencies but also partners and vendors managing sensitive government information.
Below are the key categories of organizations that are required (or commonly expected) to comply with FISMA requirements:
- Federal Agencies: All executive branch departments must comply with FISMA standards, maintain security programs, and report annually on their information security posture.
- State and Local Entities Handling Federal Data: State/local agencies, universities, and research institutions handling federal data, grants, or programs must implement FISMA-aligned controls.
- Contractors and Third‑Party Service Providers: Organizations contracting with federal agencies, including IT, consulting, and support providers, must meet FISMA requirements for any federal information they handle.
- SaaS and Cloud Providers Supporting Federal Operations: Providers supporting federal operations by processing, storing, or transmitting federal data must integrate FISMA compliance, often via frameworks like FedRAMP.
- Healthcare Vendors with Federal Health Data: Organizations in healthcare handling federally funded patient data or program systems (e.g., Medicare, Medicaid) that support federal operations must implement FISMA‑aligned security controls to protect sensitive health information.
- Financial Institutions Supporting Federal Programs: Banks and financial firms that manage federal program data, grants, loans, or systems on behalf of government agencies fall under FISMA expectations when they handle or store federal information.
- Universities and Research Institutions with Federal Funding: Higher education institutions receiving federal grants or conducting research involving federal systems must ensure information security programs meet FISMA criteria to protect sensitive research data.
- Energy & Utilities Partners of Federal Infrastructure: Critical infrastructure operators that support federal systems or handle controlled federal data must align security programs with FISMA’s mandate for systemic risk management.
Once you identify who must comply, the next step is understanding operational requirements, blending both technical controls and governance responsibilities.
FISMA Compliance Operational Requirements: Technical and Non‑Technical Perspectives
FISMA compliance blends technical control implementation with organizational processes that demonstrate how your security program manages risk continuously and remains audit‑ready.
Below, we break the requirements into technical components and complementary non‑technical compliance expectations.
Technical Components of a FISMA Compliance Program
These are the building blocks that make your systems secure and measurable:
- Maintain an Updated Information System Inventory: Keep a comprehensive inventory listing all systems that process or store federal information, including integrations and boundaries. This inventory forms the foundation for risk categorization and control mapping.
- Risk Categorization and Framework Alignment: Classify systems based on potential impact (low/moderate/high) using standards such as FIPS 199. This risk categorization drives control selection and prioritization.
- Security Control Selection and Implementation: Select and implement appropriate security controls from NIST SP 800‑53 tailored to each system’s risk level. These controls cover access management, incident response, configuration management, and more.
- Continuous Monitoring and System Assessment: Establish mechanisms to monitor controls and system health continuously, detect changes, and measure effectiveness over time. This ensures that security stays current and aligned with emerging risks.
- Documentation and Evidence of Control Performance: Technical documentation, such as System Security Plans (SSPs), assessment results, and monitoring outputs, must be maintained and updated regularly to support audit readiness.
Non‑Technical Compliance Requirements for Leaders
These are the compliance expectations that help your organization stay aligned with FISMA governance and federal oversight expectations:
- Develop and Maintain Policies and Procedures: Establish written policies, governance roles, and operating procedures that guide security activities, control implementation, and risk decisions.
- Formal Risk Assessments and Documentation: Conduct risk assessments regularly and after system changes, and document decisions to support both internal governance and external audit evidence.
- Annual Reporting and Oversight Preparation: Prepare comprehensive reports and evidence packages for annual FISMA reporting. These include summaries of control performance, risk posture, and compliance status.
- Certification and Authorization Processes: Before systems operate, conduct assessments and acquire formal authorizations to operate (ATO) based on documented evidence and control effectiveness.
- Leadership Accountability and Review: Senior leadership must review and approve compliance activities, ensuring accountability and governance visibility across teams and programs.
FISMA breaks down when risks are identified but not tracked, owned, or acted on. VComply’s RiskOps turns risk assessments into living workflows. This links system impact levels, control gaps, incidents, and remediation plans in one place.
Also Read: How to Achieve and Maintain Cybersecurity Compliance
Central to operational compliance are FISMA controls, which define actionable safeguards that protect federal information and scale across systems
What Are FISMA Controls and How Organizations Should Manage Them at Scale

FISMA controls safeguard the confidentiality, integrity, and availability of federal information systems. Grouped by operational themes, they support consistent risk governance and scalable compliance, and are based on NIST SP 800‑53, the standard control catalog for FISMA.
Below are the key thematic control areas you should focus on:
- Access Management Controls: Controls that regulate system and data access, including account management, role-based permissions, and authentication, to prevent unauthorized use.
- Incident Response Controls: Establish capabilities to detect, respond, and recover from security events with documented plans, defined roles, and testing exercises.
- Risk Assessment Controls: Ongoing identification and evaluation of threats and vulnerabilities to prioritize fixes and tailor controls to actual risks.
- Configuration Management Controls: Enforce secure baselines, track changes, and manage updates/patches to prevent vulnerabilities and maintain auditability.
- Monitoring and Reporting Controls: Continuously track security events and control effectiveness through logging, anomaly review, and compliance reporting for governance and audit readiness.
Implementing controls is only half the story; organizations benefit from practical, operational steps to maintain continuous FISMA compliance every day.
Best Practices & Checklist for Operational FISMA Compliance
FISMA compliance isn’t just about checking boxes; it’s about repeatable practices that keep risks visible, evidence current, and teams accountable every day. Scattered spreadsheets and disconnected tools make readiness time-consuming, error-prone, and stressful, especially during audits.
Below are integrated, practical steps that help you make compliance continuous, manageable, and audit‑ready.
1. Centralize Compliance Data and Evidence
Maintain a unified repository for system inventories, policies, controls, risks, evidence artifacts, and reporting metrics. This reduces siloed information flows and speeds up audit evidence assembly, especially when disparate teams must collaborate.
Example: In healthcare environments handling federal health data, a central source of truth lets compliance teams quickly confirm control implementation across electronic medical record systems.
2. Assign Clear Ownership for Controls and Risks
Designate accountable owners for each control, risk area, and compliance documentation artifact. Defined ownership drives follow‑through on remediation, reduces blind spots, and clarifies responsibility during audits or oversight reviews.
3. Automate Evidence Collection and Monitoring
Automate the aggregation of logs, assessments, configurations, and compliance artifacts where feasible. With continuous data feeds and alerts, you reduce manual tracking, improve accuracy, and ensure evidence stays audit‑ready.
4. Maintain Always‑Audit‑Ready Documentation
Treat key compliance documents, System Security Plans (SSPs), POA&Ms, policies, and risk assessments as living artifacts. Update them as systems change and reflect changes in control status or organization structure. Regular maintenance saves time and supports federal reporting cycles.
5. Integrate Risk and Incident Tracking
Link incident logs to risk registers and controls so that events automatically feed back into your risk and compliance view. This ensures vulnerabilities and incidents drive real improvements to controls and evidence quality.
6. Conduct Continuous Monitoring Instead of Annual Audits Only
FISMA emphasizes ongoing evaluation of security controls, not just annual reviews. Operational practices should include real‑time monitoring and reporting of key compliance metrics, vulnerability scans, and configuration changes so gaps are detected early.
7. Produce Audit‑Ready Reports On Demand
Build systems and workflows that let you generate compliance reports, evidence logs, control status summaries, and executive briefings at any time, not just when an audit is imminent.
Also Read: Compliance Management Best Practices for Public Agencies
Now, let’s explore some operational and organizational challenges that can impede achieving full FISMA compliance.
Common Challenges Organizations Face With FISMA Compliance
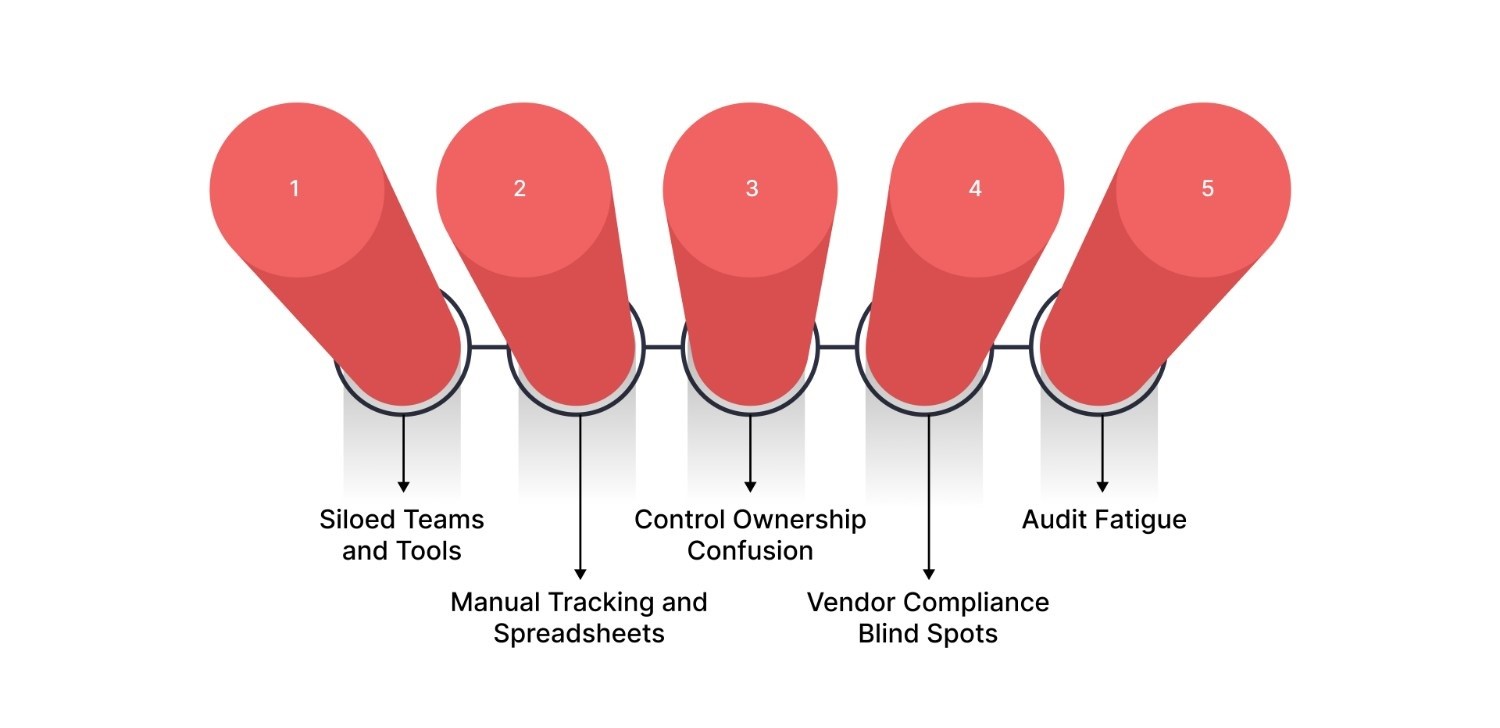
Below are the most prevalent challenges organizations encounter as they implement and sustain FISMA compliance:
- Siloed Teams and Tools: Compliance data and evidence spread across IT, security, risk, and legal departments create inconsistent documentation and disjointed control implementation, making coherent audit evidence difficult.
- Manual Tracking and Spreadsheets: Ad-hoc spreadsheets for systems, controls, and remediation increase errors, version confusion, and slow audit preparation, diverting time from proactive risk mitigation.
- Control Ownership Confusion: Unclear accountability across teams leads to gaps in control implementation and delays in producing audit-ready evidence.
- Vendor Compliance Blind Spots: Third-party and cloud systems can create compliance gaps when oversight and inventory of external systems are incomplete or misaligned with agency responsibilities.
- Audit Fatigue: Annual reporting, continuous monitoring, and periodic assessments without automation or centralized evidence management result in repeated audit fire drills rather than sustained readiness.
FISMA compliance fails most often at the seams where compliance, risk, policy, and incident teams operate in isolation. VComply’s GRCOps approach unifies ComplianceOps, RiskOps, PolicyOps, and CaseOps into a single operating system. That means fewer handoffs, clearer accountability, and a continuous line of sight from federal requirements to controls, risks, incidents, and audit evidence.
Even with benefits in sight, organizations often encounter operational and organizational challenges that can impede achieving full FISMA compliance.
How VComply Helps Organizations Operationalize FISMA Compliance End to End
FISMA compliance requires more than checklists; it demands a centralized system that operationalizes policy, risk, evidence, and audit readiness. VComply, a cloud-native GRC platform, unifies these activities into a single interface, reducing manual effort, providing real-time visibility, and keeping organizations audit-ready without relying on spreadsheets or last-minute preparation.
Below is how VComply supports end‑to‑end FISMA compliance outcomes that matter most:
- Centralized Compliance Management: A unified dashboard centralizes responsibilities, audit evidence, control status, and task assignments, reducing manual reconciliation and keeping teams aligned.
- Policy Oversight with Version Control: Automates policy distribution, approval workflows, and version tracking, ensuring stakeholders have access to current requirements and audit-ready documentation.
- Proactive Risk and Control Tracking: RiskOps lets you identify, assess, prioritize, and monitor risks in a centralized register with dashboards and heatmaps to visualize control effectiveness and action plans.
- Incident and Case Management: CaseOps centralizes incident reporting, investigation, and remediation, linking every incident to evidence and risk records for traceability and audit readiness.
- Audit-Ready Reporting: Streamlined evidence capture and custom dashboards allow on-demand compliance reporting for executives and auditors without hunting through files.
- Integrated Operations: Combining ComplianceOps, RiskOps, PolicyOps, and CaseOps breaks down silos, providing cohesive oversight of controls, risks, policies, incidents, and evidence in one platform.
Book a free demo at VComply to explore how it can transform your FISMA compliance program, ensuring continuous operational compliance, audit readiness, and executive confidence.
Final Thoughts
FISMA compliance is more than a checklist; it’s a strategic commitment to protecting sensitive government information and sustaining operational resilience amid continuous cyber threats. A strong FISMA program aligns security with risk management, enforces accountability, and enables rapid incident response, with structured programs, continuous monitoring, and documented evidence forming its foundation.
Managing continuous compliance, from inventories and controls to reporting and audits, is complex. VComply offers a unified platform that embeds compliance into daily operations, centralizing control management, policy oversight, risk tracking, incident management, and audit-ready dashboards.
If you’re ready to transform your compliance operations and stay audit‑ready with less effort, start a 21‑day free trial today to experience how VComply can streamline your FISMA compliance journey.
FAQs
FISMA compliance requires detailed artifacts such as a System Security Plan (SSP), Security Assessment Report (SAR), Plans of Action and Milestones (POA&M), continuous monitoring strategy, and incident response documentation. These records demonstrate control implementation, risk status, and readiness for audits.
Organizations should update their SSP whenever significant changes occur, such as new systems, altered risks, or updated controls, and at least annually to reflect current architecture, control status, and security posture before assessment and reporting cycles.
FISMA impact levels, Low, Moderate, and High, are determined based on the potential impact of a security breach on confidentiality, integrity, and availability. Higher impact systems require more stringent controls and oversight.
FISMA generally does not apply to organizations that do not process, store, or transmit federal information or do not operate systems on behalf of federal agencies. Entities without any federal data responsibilities are typically out of scope.
An ATO is a formal authorization granted by an Authorizing Official after evaluating a system’s security posture based on documentation like SSP, SAR, and POA&M. Validity varies by agency policy but must be reevaluated with ongoing monitoring and reauthorization processes.

