NIST 800-171: Requirements, Controls, and Compliance for Handling CUI
For compliance leaders and security teams supporting federal contracts, NIST 800-171 is rarely encountered as a standalone framework; it shows up in audits, contract clauses, and assessment requirements.
DFARS 252.204-7012 mandates its implementation, incident reporting timelines are enforced, and CMMC assessments increasingly require organizations to demonstrate that controls are not only defined but are also actively operating.
The challenge is not understanding the requirements. It is proving them. Teams are expected to maintain System Security Plans, track remediation through POA&Ms, and produce audit-ready evidence across more than 100 controls, often spread across systems, departments, and third-party environments.
As regulatory scrutiny increases, this becomes a governance problem. Without structured oversight, organizations struggle to maintain visibility into control status, coordinate across teams, and sustain continuous compliance.
Understanding NIST 800-171, in this context, is not just about the controls; it is about how those controls are implemented, monitored, and demonstrated under audit conditions.
Key Takeaways
- NIST 800-171 establishes the baseline cybersecurity requirements for protecting Controlled Unclassified Information (CUI) in contractor environments, making it a core compliance obligation for organizations participating in federal supply chains.
- Compliance is increasingly tied to contract eligibility, particularly through DFARS clauses and the Department of Defense’s CMMC program, which formalizes how contractors must demonstrate implementation of required controls.
- The framework’s 110 security requirements span operational domains such as access control, incident response, audit logging, and risk assessment, requiring coordination across IT, compliance, security, and internal audit functions.
- Auditors and federal assessors expect structured documentation, including System Security Plans (SSPs), Plans of Action and Milestones (POA&Ms), and evidence of continuous monitoring.
- Sustainable compliance depends on governance discipline, ensuring controls, risks, policies, and remediation efforts are tracked systematically rather than managed through fragmented spreadsheets or isolated security tools.
What Is NIST 800-171?
NIST Special Publication 800-171 is a cybersecurity standard that defines security requirements for protecting Controlled Unclassified Information (CUI) when that information resides in non-federal systems and organizations. The framework was developed by the National Institute of Standards and Technology (NIST) publication page to help federal agencies ensure that sensitive government information remains protected even when it is shared with contractors, research institutions, and supply-chain partners.
Unlike internal federal security standards, NIST 800-171 focuses specifically on organizations outside government networks that still handle federal data as part of contracts or cooperative programs. In practice, this means defense contractors, subcontractors, technology providers, and research universities must implement defined security practices wherever CUI is processed, stored, or transmitted.
From a governance perspective, the framework does more than prescribe technical safeguards. It requires organizations to establish structured oversight around access control, incident response, risk assessment, system integrity, and other operational security disciplines that directly affect how sensitive data moves through the enterprise.
What This Means for Compliance and Security Teams
For organizations handling CUI, NIST 800-171 is not a one-time implementation—it becomes part of daily operations. Controls must be continuously monitored, evidence must be maintained, and audit readiness must be sustained across systems and teams.
In practice, teams are managing:
- Control ownership across IT, security, and compliance
- Ongoing POA&M tracking and remediation
- Evidence collection for audits and assessments
- Alignment with CMMC requirements and contract obligations
When these activities are handled through spreadsheets or disconnected systems, visibility breaks down. Teams spend more time coordinating and validating than managing risk.
For most organizations, the challenge is not understanding NIST 800-171; it is operationalizing it at scale without losing control or audit readiness.
Who Must Comply With NIST 800-171?
NIST 800-171 primarily applies to organizations that handle federal information but operate outside government networks. In most cases, compliance is triggered through contractual obligations rather than statutory regulation.
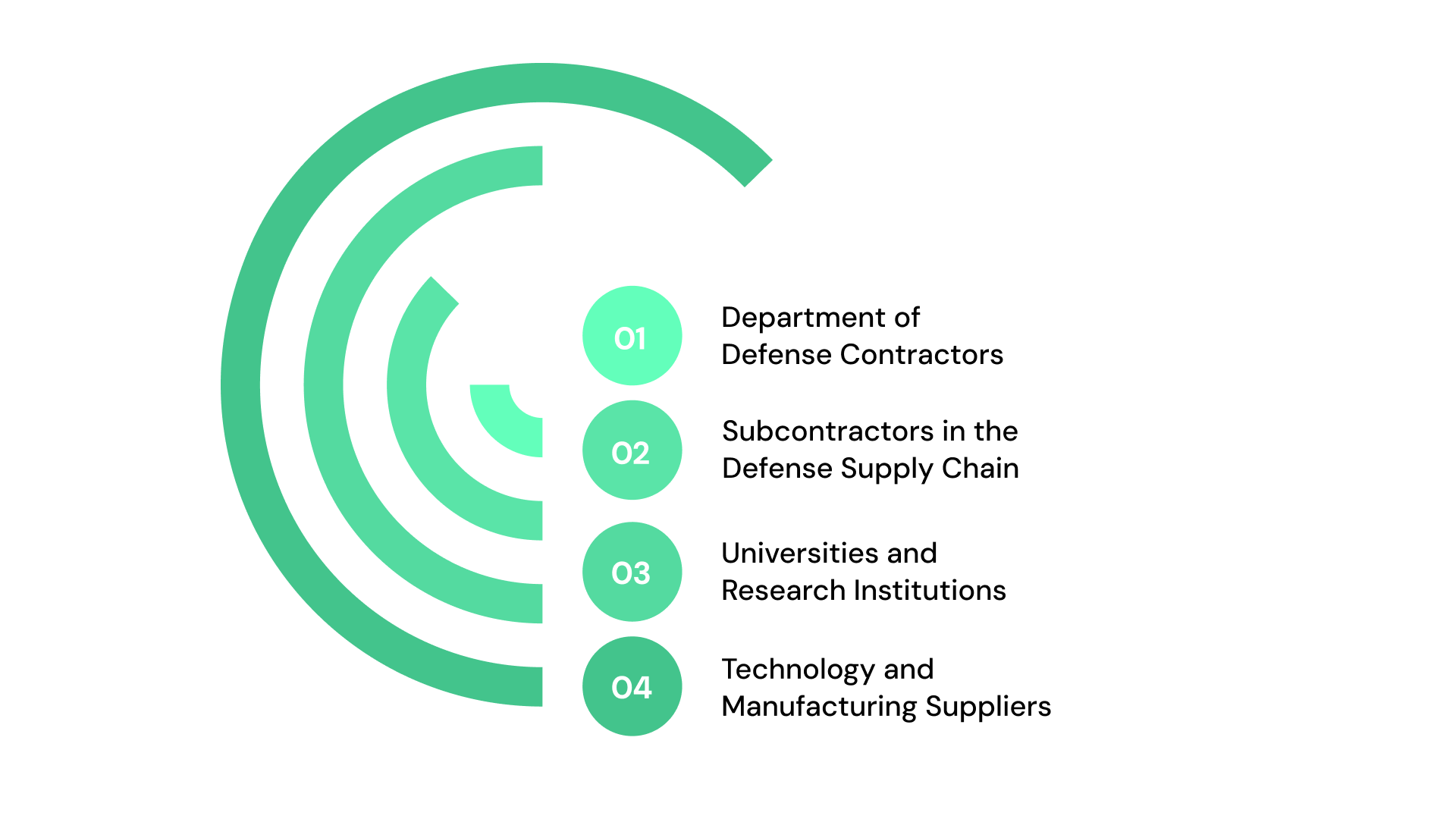
1. Department of Defense Contractors
The most visible group subject to NIST 800-171 is the Defense Industrial Base (DIB). Companies supporting Department of Defense programs must protect government data in contractor environments. These requirements typically appear in procurement agreements through the Defense Federal Acquisition Regulation Supplement (DFARS).
For governance leaders, the implication is clear: cybersecurity controls become part of contract performance requirements, not just internal security policy.
2. Subcontractors in the Defense Supply Chain
Compliance obligations often extend beyond prime contractors. Subcontractors that store or process controlled government information must also implement NIST 800-171 safeguards.
In large supply chains, common in aerospace, defense manufacturing, and advanced engineering, this creates a distributed compliance environment where multiple organizations must maintain consistent security controls and documentation.
3. Universities and Research Institutions
Universities conducting federally funded research frequently receive datasets, technical specifications, or engineering documentation that qualify as CUI. As a result, many academic institutions must implement NIST 800-171 security practices within research labs, IT infrastructure, and collaborative environments.
4. Technology and Manufacturing Suppliers
Organizations providing software, components, or technical services to federal programs may also handle controlled data. Even when the organization is not directly working with a federal agency, the presence of CUI in operational systems can trigger NIST 800-171 requirements.
For leadership teams, the challenge is ensuring governance processes extend across third-party relationships and supply-chain partners.
What Is Controlled Unclassified Information (CUI)?
The concept of Controlled Unclassified Information (CUI) sits at the center of the NIST 800-171 framework.
Definition of CUI
CUI refers to sensitive government information that does not meet the criteria for classified national security information but still requires safeguarding or controlled dissemination.
Examples may include:
- Defense technical drawings
- Export-controlled engineering specifications
- Sensitive research datasets
- Federal law enforcement information
- Procurement and acquisition data
While these materials are not classified, their exposure could still create operational, security, or economic risks.
Why CUI Requires Special Protection
Federal agencies routinely share information with external organizations to enable research, manufacturing, software development, and national infrastructure projects. Without structured safeguards, this information becomes vulnerable once it leaves government systems.
NIST 800-171 establishes a consistent security baseline so that federal agencies can trust external partners to protect that information appropriately.
Examples of CUI in Supply Chains
Organizations often encounter CUI in areas such as:
- defense program documentation
- federally funded research programs
- engineering and manufacturing supply chains
- cybersecurity threat intelligence shared with contractors
Identifying where CUI exists within the organization is one of the first operational challenges in implementing NIST 800-171.
The 110 Security Controls in NIST 800-171
At the operational level, NIST 800-171 translates data protection expectations into a defined set of security practices.
The framework includes 110 security requirements organized into 14 control families, covering both technical safeguards and organizational security processes.
These requirements provide the baseline security posture organizations must maintain when handling CUI.
The 14 Control Families
The controls are grouped into functional categories that reflect common areas of enterprise cybersecurity governance.
Examples include:
- Access Control (AC) – restricting system access to authorized users
- Awareness and Training (AT) – ensuring personnel understand security responsibilities
- Audit and Accountability (AU) – logging and reviewing system activity
- Configuration Management (CM) – controlling system changes
- Identification and Authentication (IA) – verifying user identities
- Incident Response (IR) – responding to security incidents
- Media Protection (MP) – protecting storage media containing CUI
- Physical Protection (PE) – securing facilities and hardware
- Risk Assessment (RA) – identifying and evaluating security risks
- Security Assessment (CA) – evaluating control effectiveness
- System and Communications Protection (SC) – protecting system communications
- System and Information Integrity (SI) – ensuring systems remain secure and uncompromised
Together, these domains create a comprehensive security control structure covering both technical infrastructure and operational processes.
How Controls Are Structured
Each control family contains specific security requirements that organizations must implement. These requirements may include technical configurations, operational procedures, and monitoring activities.
For example, the access control family includes requirements to restrict system access to authorized users and limit the functions that those users can perform.
This structure ensures security protections operate across personnel practices, system configurations, and operational processes rather than relying on isolated technical safeguards.
Assessment Objectives and Evidence
Demonstrating compliance requires more than implementing controls. Organizations must maintain evidence showing that those controls are functioning as intended.
Assessments typically evaluate:
- configuration settings
- policy documentation
- monitoring activities
- incident response procedures
- audit logs and system records
This documentation forms the basis of compliance validation during audits and certification processes.
Documentation Required for NIST 800-171 Compliance
Implementing the framework requires extensive documentation to demonstrate how security practices are applied and maintained.
1. System Security Plan (SSP)
The System Security Plan (SSP) describes the system environment where CUI is handled and explains how each NIST 800-171 control is implemented.
An SSP typically includes:
- system architecture and boundaries
- implemented security controls
- responsible personnel and processes
- supporting technologies and safeguards
For auditors and assessors, the SSP serves as the central reference document for evaluating compliance.
2. Plan of Action and Milestones (POA&M)
The POA&M identifies security gaps and outlines remediation plans. Each unresolved requirement is documented, along with the steps needed to address it and the completion timeline.
In practice, the POA&M becomes a management tool for tracking remediation progress.
3. Policies, Procedures, and Evidence
Organizations must also maintain operational documentation supporting control implementation. This includes:
- security policies
- incident response procedures
- risk assessments
- training records
- monitoring reports
Maintaining these artifacts in an organized manner is essential for demonstrating compliance during audits.
5 Required Steps to NIST 800-171 Compliance Before Your Next Audit
Implementing NIST 800-171 is not a linear checklist; it is a coordinated effort across cybersecurity, compliance, IT, and audit functions. Each step requires not just execution, but traceability, documentation, and alignment with assessment expectations.
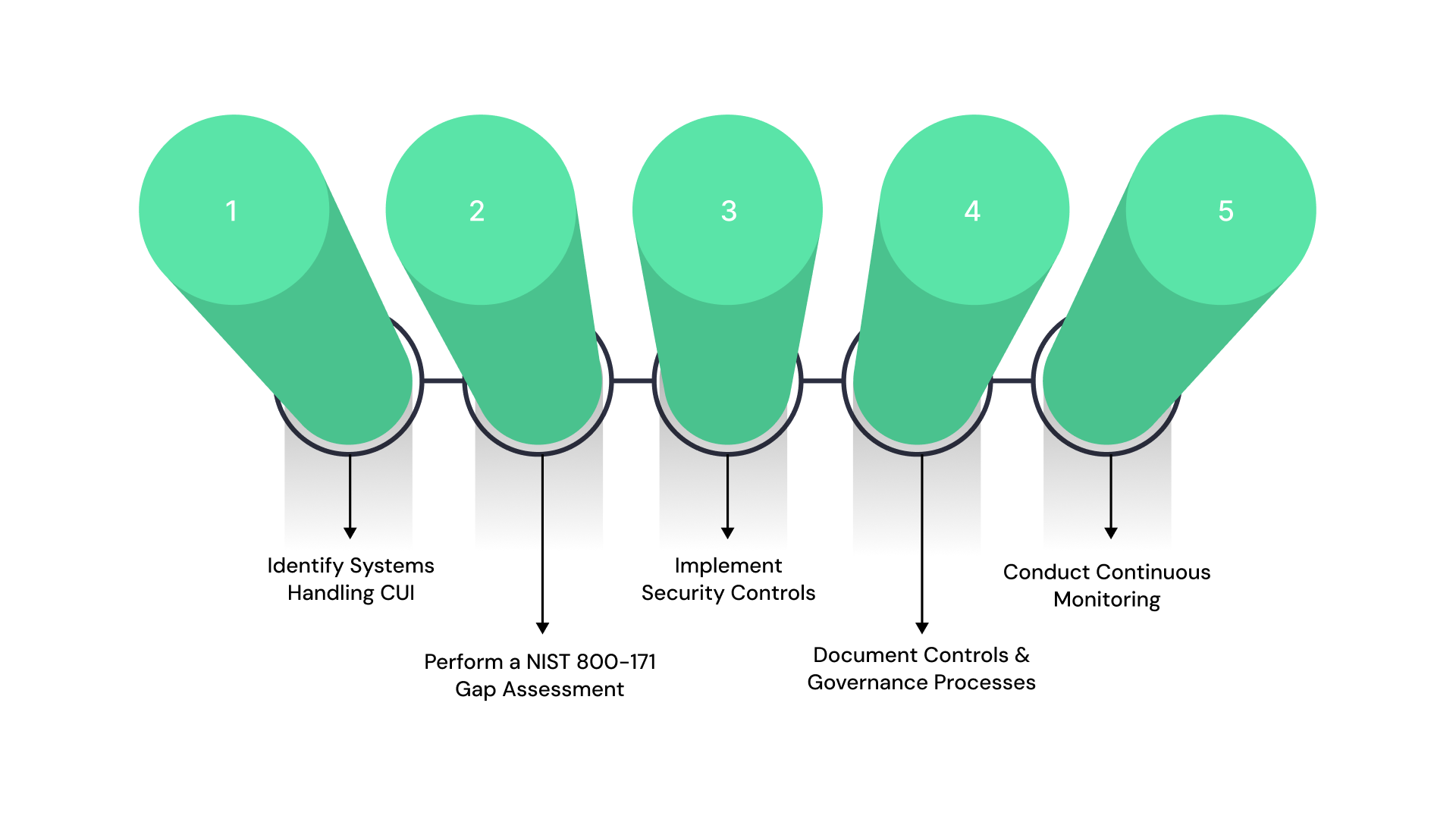
Step 1. Identify Systems Handling CUI
Organizations must first determine where CUI exists within their systems. This requires clearly defining system boundaries, data flows, and third-party interactions—not just at a high level, but in a way that can be documented and defended during an assessment.
In practice, this step often exposes gaps:
- CUI stored in collaboration tools or unmanaged environments
- Lack of clarity on which systems fall in scope
- Third-party vendors handling CUI without full visibility
Without accurate scoping, downstream controls and documentation become unreliable.
Step 2. Perform a NIST 800-171 Gap Assessment
A gap assessment compares current controls against the 110 NIST 800-171 requirements to identify missing or incomplete safeguards.
This is not just a technical review, it should evaluate:
- Policies and procedures
- Control implementation across systems
- Availability of supporting evidence
The output of this step is critical. Identified gaps must be formalized into a Plan of Action and Milestones (POA&M) with defined ownership, timelines, and remediation priorities.
For most organizations, this is where the first major challenge appears: gaps are identified, but tracking and resolving them consistently becomes difficult.
Step 3. Implement Security Controls
Organizations then implement required safeguards across technical, administrative, and operational domains. This includes access controls, logging, incident response, configuration management, and risk assessment processes.
Implementation is not just about deploying tools. It requires:
- Aligning controls with actual system usage
- Ensuring policies reflect real practices
- Training personnel responsible for execution
A common failure point is treating controls as static configurations rather than ongoing operational activities.
Step 4. Document Controls and Governance Processes
Documentation is central to NIST 800-171 compliance. Auditors do not assess intent—they assess what is documented, implemented, and evidenced.
Key artifacts include:
- System Security Plan (SSP): documents how each control is implemented
- POA&M: tracks unresolved gaps and remediation progress
- Policies, procedures, and supporting evidence
Inconsistent or outdated documentation is one of the most common reasons organizations fail assessments or lose contract opportunities.
This step often becomes a bottleneck when documentation is managed across multiple systems without clear ownership.
Step 5. Conduct Continuous Monitoring
Compliance does not end after implementation or assessment. Controls must be continuously monitored to ensure they remain effective as systems, users, and risks evolve.
This includes:
- Periodic control testing
- Ongoing risk assessments
- Updating SSP and POA&M as changes occur
- Maintaining real-time evidence for audits
As CMMC requirements increase, organizations are expected to move from periodic compliance to continuous readiness, where evidence and control status are always current, not assembled during audits.
Common Challenges in NIST 800-171 Compliance
Even well-resourced organizations encounter operational challenges when implementing the framework.
1. Tracking Evidence Across Multiple Controls
With more than 100 individual requirements, maintaining accurate evidence for each control can become complex, particularly when documentation is distributed across different teams.
2. Coordinating Compliance Across Teams
NIST 800-171 requirements span multiple departments, including:
- cybersecurity
- IT operations
- compliance and risk management
- internal audit
- legal and procurement
Coordinating activities across these groups requires structured governance processes.
3. Maintaining Continuous Compliance Readiness
Organizations often implement controls during initial compliance efforts but struggle to maintain oversight over time. Changes in infrastructure, personnel, or suppliers can introduce new risks that affect compliance posture.
Operationalizing NIST 800-171 Compliance
For many organizations, the most difficult aspect of NIST 800-171 is not understanding the requirements; it is sustaining compliance operationally.
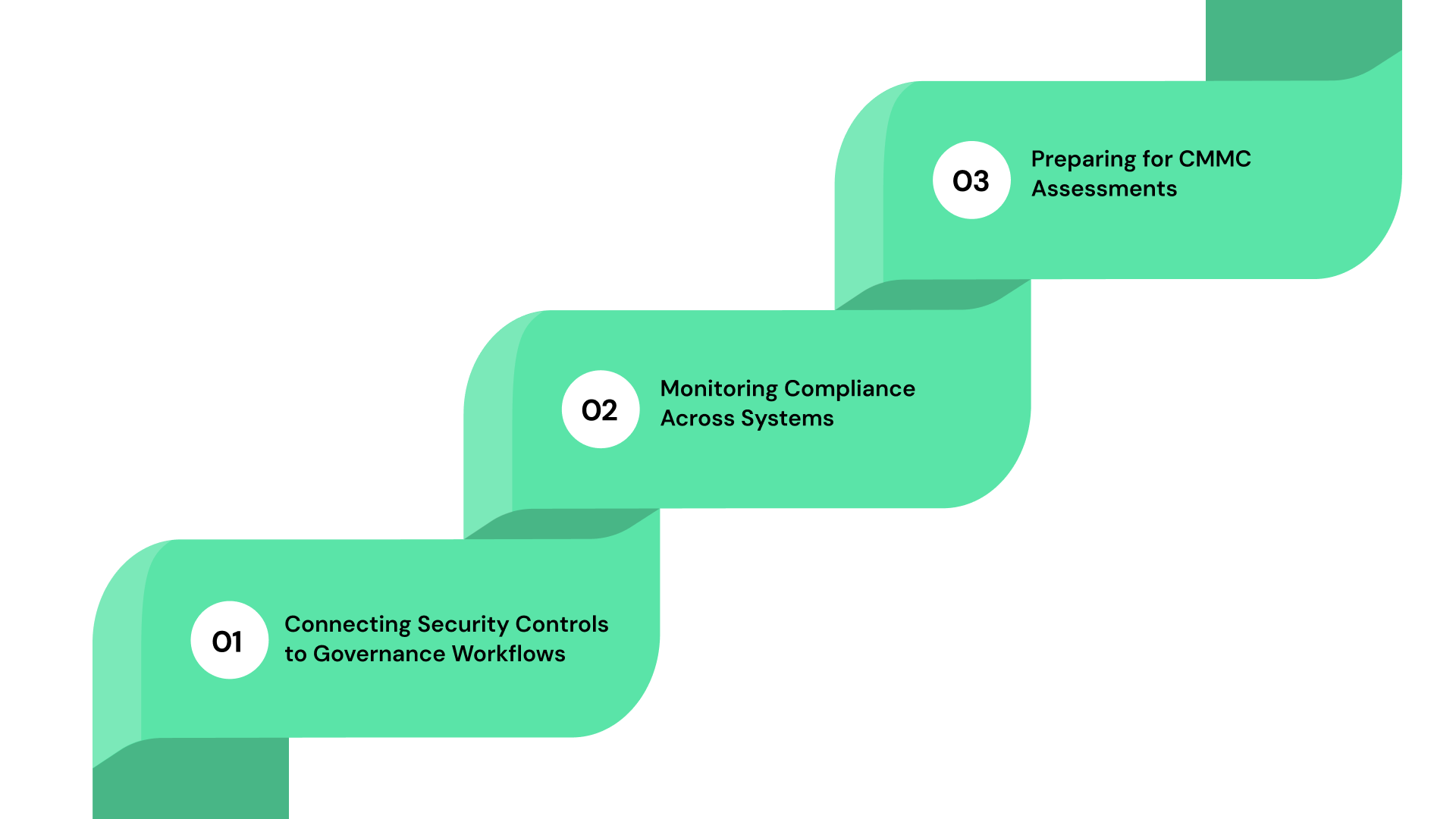
1. Connecting Security Controls to Governance Workflows
Security controls must be embedded into everyday operational processes such as access provisioning, system configuration changes, and incident management.
Without defined workflows, controls risk becoming policy statements rather than enforceable practices.
2. Monitoring Compliance Across Systems
Organizations handling CUI often operate complex IT environments that include cloud services, on-premise systems, and third-party platforms. Maintaining consistent visibility across these environments is essential for identifying compliance gaps.
3. Preparing for CMMC Assessments
As CMMC assessments become more common in federal contracting, organizations must ensure they can demonstrate evidence of control implementation and ongoing oversight.
This requires governance structures that connect risk management, compliance documentation, and security monitoring into a coordinated operational framework.
Structuring NIST 800-171 Compliance Across the Organization
As NIST 800-171 programs mature, the challenge shifts from implementing controls to managing them consistently. Teams must track control ownership, maintain audit-ready evidence, update documentation, and monitor remediation across more than 100 requirements, often spread across systems and departments. As CMMC assessments increase, this expectation moves from periodic validation to continuous oversight.
In many organizations, these activities are still managed through spreadsheets, shared drives, and manual coordination. This makes it difficult to maintain a clear view of control status, ensure consistency in documentation, and respond confidently during audits.
ComplianceOps helps address this by bringing NIST 800-171 into a structured operational system. It centralizes control tracking, aligns requirements with evidence, and provides visibility into compliance status across teams, so organizations can maintain continuous audit readiness rather than assembling it under pressure.
See how ComplianceOps supports structured oversight of NIST 800-171 by centralizing control tracking, documentation, and compliance workflows. Book a demo.
Conclusion
Federal contractors and supply-chain partners handling Controlled Unclassified Information operate under constant pressure to prove that controls are in place, evidence is current, and risks are actively managed.
In practice, this often translates into chasing documentation, reconciling spreadsheets, and coordinating across teams just to stay audit-ready, while visibility into actual control performance remains limited.
The goal is not just to meet NIST 800-171 requirements, but to run compliance as a controlled, continuous process, where controls are clearly owned, evidence is always audit-ready, and leadership has real-time visibility into compliance posture.
VComply enables this shift by bringing NIST 800-171 into a structured governance system, connecting controls, evidence, risk tracking, and audit workflows so teams can move from reactive compliance to consistent operational oversight.
Start a 21-Day Free Trial to see how VComply helps maintain continuous compliance and audit readiness across governance programs.
FAQs
NIST 800-171 is a cybersecurity framework that defines security requirements for protecting Controlled Unclassified Information (CUI) in systems operated by contractors and other non-federal organizations.
Organizations that store, process, or transmit CUI on behalf of U.S. federal agencies—particularly defense contractors, subcontractors, research institutions, and supply-chain partners- are typically required to implement NIST 800-171 controls.
The framework includes 110 security requirements organized into 14 control families, covering areas such as access control, incident response, risk assessment, and system integrity.
NIST 800-171 itself is a guidance standard, but it becomes mandatory when referenced in federal contracts, particularly through Defense Federal Acquisition Regulation Supplement (DFARS) clauses for Department of Defense programs.
Organizations typically maintain documentation such as System Security Plans (SSPs), Plans of Action and Milestones (POA&Ms), risk assessments, policies, and monitoring records to demonstrate how security controls are implemented and maintained.

