ISO 27001 – Everything You Need to Know
ISO 27001, often referred to as the gold standard for information security management, is a globally recognized framework that sets the guidelines and requirements for establishing, implementing, and maintaining an effective Information Security Management System (ISMS). This standard plays a pivotal role in safeguarding sensitive data and information assets, helping organizations protect against cybersecurity threats and data breaches.

In this comprehensive guide, we’ll look into everything you need to know about ISO 27001, from its core principles to its benefits for businesses and the steps to achieve compliance.
ISO 27001 is an international standard for information security management systems (ISMS). It’s often referred to as ISO/IEC 27001 due to its collaborative development by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). Collectively, these standards are part of the ISO/IEC 27000 series and provide best practices for Information Security Management Systems (ISMS).
The primary purpose of ISO 27001 is to assist organizations, regardless of their size, in safeguarding their information systematically, cost-effectively, and with a risk-based approach. While it’s not mandatory to implement ISO 27001, the benefits it can bring to your information security management are compelling.
It’s important to note that ISO 27001 doesn’t function in isolation; it requires input from management and other key decision-makers to accurately assess security risks, threats, and vulnerabilities. Customized security controls designed by an organization’s management are essential for addressing organization-specific security issues.
An ISMS consists of four core components, often referred to as the four Ps:
In practice, an ISMS covers a wide range of activities, from HR processes to data encryption, business continuity planning, and vendor risk management. It encompasses everything an organization does to identify and manage information security risks.
Compliance with an ISMS offers more than just ISO 27001 certification; it can lead to improved business efficiency, cost reduction, eliminating redundancies, and establishing scalable security practices.
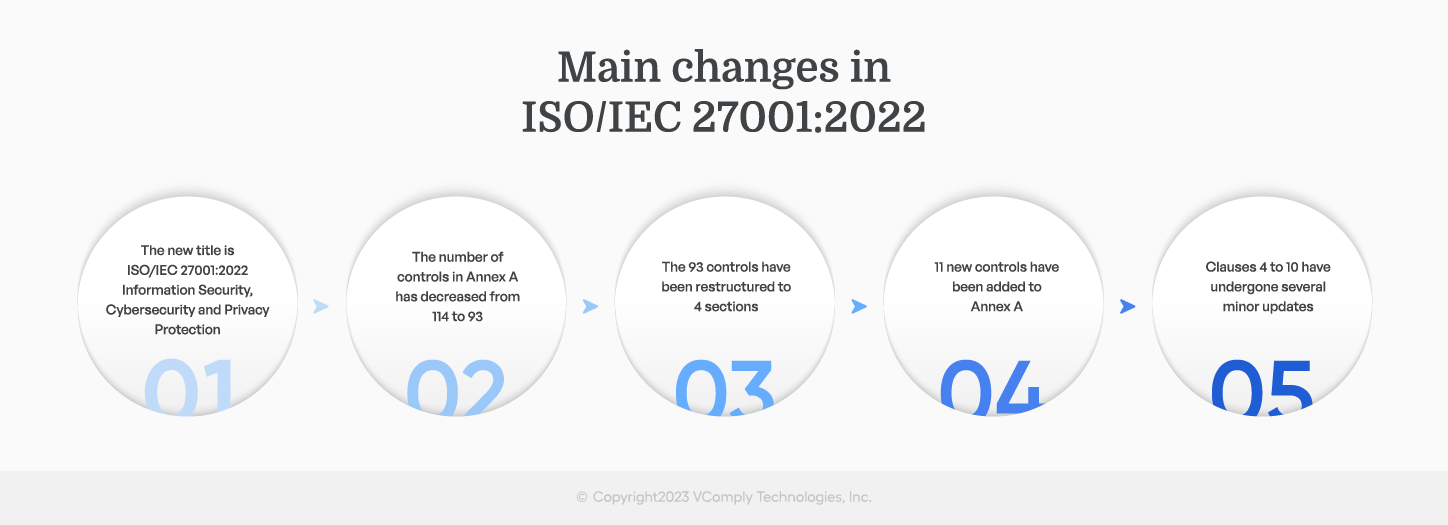
Clauses 4-10 outline the complete set of prerequisites that an Information Security Management System (ISMS) needs to fulfill for ISO 27001 certification. Meanwhile, Annex A provides a catalog of 93 security controls that organizations can adopt to satisfy these requirements.
Note that, prior to the updates in 2022, there were 114 controls; the number of controls has dropped from 114 to 93, and it is organized into only four sections versus the 14 sections in the 2013 revision.
The official ISO/IEC 27001:2022 standards document is structured into distinct sections, namely clauses and annexes. Among these, Clauses 4-10 and Annex A are of utmost significance for organizations seeking ISO 27001 certification.
In Clauses 4-10, you will find a comprehensive list of requirements that an Information Security Management System (ISMS) must fulfill to meet the criteria for ISO 27001 certification. These clauses define the fundamental elements an organization must have in place to establish and maintain a robust ISMS.
Annex A, on the other hand, contains a set of 93 security controls. These controls offer a practical framework that organizations can implement to address the requirements outlined in Clauses 4-10. By incorporating these controls, organizations can effectively bolster their information security measures and work towards ISO 27001 certification.
ISO 27001 is structured around several key clauses that define the requirements for establishing and maintaining an Information Security Management System (ISMS). Here, I’ll elaborate on Clauses 4 to 10, which cover various aspects of the ISMS:
Clause 4: Context of the Organization
4.1 Understanding the organization and its context: This clause requires the organization to identify internal and external factors that can affect its information security objectives. This includes understanding the business environment, stakeholders, and the legal and regulatory context.
4.2 Understanding the needs and expectations of interested parties: Organizations must identify the needs and expectations of relevant stakeholders (e.g., customers, regulatory authorities) and ensure these are considered in defining information security objectives.
Clause 5: Leadership
5.1 Leadership and commitment: Top management should demonstrate leadership and commitment to the ISMS, including establishing an information security policy and assigning roles and responsibilities.
5.2 Policy: The organization is required to establish an information security policy that aligns with its objectives and commitment to information security.
Clause 6: Planning
6.1 Actions to address risks and opportunities: Organizations must determine the risks and opportunities that need to be addressed to ensure the ISMS can achieve its intended outcomes. This includes assessing and treating risks and identifying opportunities for improvement.
6.2 Information security objectives and planning to achieve them: Set information security objectives at relevant functions and levels, and create plans to achieve them. Objectives should be measurable and consistent with the information security policy, and the organization’s risk assessment should be taken into account.
Clause 7: Support
7.1 Resources: Ensure that adequate resources (including personnel, infrastructure, and technology) are available to establish, implement, maintain, and continually improve the ISMS.
7.2 Competence: Identify the necessary competence for personnel involved in information security, provide training as needed, and ensure that personnel are aware of the relevance and importance of their activities to information security.
7.3 Awareness: Create awareness within the organization regarding the information security policy, objectives, and the importance of conforming to information security requirements.
7.4 Communication: Establish and maintain internal and external communication processes relevant to the ISMS, ensuring that information security issues are addressed.
7.5 Documented Information: Maintain and control documented information necessary for the effectiveness of the ISMS, including policies, procedures, and records.
Clause 8: Operation
8.1 Operational planning and control: Plan and control processes and activities to address information security risks and opportunities and to achieve information security objectives.
8.2 Information security risk assessment: Assess information security risks based on the organization’s criteria and then treat these risks to reduce them to an acceptable level.
8.3 Information security objectives and planning to achieve them: Implement the plans created in Clause 6 to achieve the information security objectives.
Clause 9: Performance Evaluation
9.1 Monitoring, measurement, analysis, and evaluation: Regularly evaluate the performance and effectiveness of the ISMS, including the security controls and risk management processes.
9.2 Internal Audit: Conduct internal audits to assess the ISMS’s conformity and effectiveness and identify areas for improvement.
9.3 Management Review: Conduct management reviews to ensure the continuing suitability, adequacy, and effectiveness of the ISMS.
Clause 10: Improvement
10.1 Nonconformity and corrective action: Identify and address nonconformities and take corrective actions to prevent their recurrence.
10.2 Continual Improvement: Continually improve the suitability, adequacy, and effectiveness of the ISMS by addressing the findings from internal audits and management reviews, as well as acting on opportunities for improvement.
These clauses provide a structured framework for implementing and maintaining an effective ISMS that aligns with ISO 27001 requirements and helps organizations manage their information security effectively.
The initial domain in ISO 27001’s Annex A controls in 2013 focused on whether your organization has well-defined policies for ensuring the security of its information systems.
Annex A controls within the ISO/IEC 27001 standard have undergone significant changes in the 2022 version. These changes were aimed at enhancing the usability and implementation of the standard. The key alterations include a reduction in the total number of controls, which decreased from 114 to 93. These controls are now organized into four overarching groups or domains: Organizational, People, Physical, and Technological. This restructuring has made the standard more manageable and user-friendly.
Here’s a breakdown of these domains, their respective sections, and a brief overview of the controls they encompass:
1. Organizational (Section 5 – 37 controls):
This domain focuses on policies and procedures related to the organization’s information security. It covers areas such as information policies, cloud service usage, and asset management.
2. People (Section 6 – 8 controls):
The People domain addresses security concerns related to employees and their interactions with the organization’s information assets. It includes controls for remote work, confidentiality, non-disclosure agreements, and employee screening. Here are some examples of human resources security controls:
- Screening and Background Checks: Implement controls to screen and conduct background checks on potential employees and contractors to verify their suitability and trustworthiness before granting them access to sensitive information.
- Job Descriptions: Clearly define roles, responsibilities, and duties related to information security in job descriptions and employment agreements to ensure that employees understand their security-related obligations.
- Security Awareness Training: Provide security awareness training to all employees, educating them on information security policies, best practices, and their role in safeguarding sensitive data.
3. Physical (Section 7 – 14 controls):
Physical security is crucial for safeguarding information assets. This domain encompasses controls for security monitoring, storage media handling, maintenance of physical assets, and facility security.
4. Technological (Section 8 – 34 controls):
The Technological domain deals with controls related to the use of technology and information systems. It covers aspects such as authentication, encryption, data leak prevention, and more.
In addition to the restructuring, the 2022 version introduced 11 new controls to address emerging security challenges. These controls fall into various categories:
- Threat intelligence: Enhancing the organization’s ability to proactively identify and respond to threats.
- Information security for the use of cloud services: Addressing the specific security considerations when using cloud services.
- Information and communications technology for business continuity: Ensuring information and communication systems support business continuity efforts.
- Physical security monitoring: Implementing controls for monitoring and securing physical facilities.
- Configuration management: Managing and controlling changes to the organization’s information systems.
- Information deletion: Ensuring secure and proper data deletion when it is no longer needed.
- Data masking: Implementing techniques to protect sensitive data by masking or obfuscating it.
- Data leakage prevention: Controls to prevent unauthorized data leakage.
- Monitoring activities: Monitoring and auditing various activities to maintain security.
- Web filtering: Implementing controls to filter and secure web traffic.
- Secure coding: Promoting secure software development practices to prevent vulnerabilities.
For a comprehensive understanding of these controls, their descriptions, and how to implement them, it is advisable to refer to the ISO 27001 and 27002 standards and review these documents with your team. These standards provide detailed guidance on information security management and best practices.
- Comprehensive documentation of information security policies at a high level.
- The methods employed to effectively communicate these policies throughout the organization.
- A systematic process is in place for regular policy reviews and updates.
- A transparent explanation of how these policies align with the broader requirements and objectives of the business.
This domain sets the foundation for information security processes, and its strength significantly influences all other aspects of your security measures. It ensures that your information security policies are not just words on paper but are integrated into the organization’s daily operations.
These 4 domains provide a comprehensive framework for organizations to establish, maintain, and continually improve their Information Security Management System (ISMS) to ensure the protection of their information assets.
ISO 27001:2022 Organizational Controls
| Annex A Control Type | ISO/IEC 27001:2022 Annex A Identifier | ISO/IEC 27001:2013 Annex A Identifier | Annex A Name |
|---|---|---|---|
| Organizational Controls | Annex A 5.1 | Annex A 5.1.1 Annex A 5.1.2 |
Policies for Information Security |
| Organizational Controls | Annex A 5.2 | Annex A 6.1.1 | Information Security Roles and Responsibilities |
| Organizational Controls | Annex A 5.3 | Annex A 6.1.2 | Segregation of Duties |
| Organizational Controls | Annex A 5.4 | Annex A 7.2.1 | Management Responsibilities |
| Organizational Controls | Annex A 5.5 | Annex A 6.1.3 | Contact With Authorities |
| Organizational Controls | Annex A 5.6 | Annex A 6.1.4 | Contact With Special Interest Groups |
| Organizational Controls | Annex A 5.7 | NEW | Threat Intelligence |
| Organizational Controls | Annex A 5.8 | Annex A 6.1.5 Annex A 14.1.1 |
Information Security in Project Management |
| Organizational Controls | Annex A 5.9 | Annex A 8.1.1 Annex A 8.1.2 |
Inventory of Information and Other Associated Assets |
| Organizational Controls | Annex A 5.10 | Annex A 8.1.3 Annex A 8.2.3 |
Acceptable Use of Information and Other Associated Assets |
| Organizational Controls | Annex A 5.11 | Annex A 8.1.4 | Return of Assets |
| Organizational Controls | Annex A 5.12 | Annex A 8.2.1 | Classification of Information |
| Organizational Controls | Annex A 5.13 | Annex A 8.2.2 | Labelling of Information |
| Organizational Controls | Annex A 5.14 | Annex A 13.2.1 Annex A 13.2.2 Annex A 13.2.3 |
Information Transfer |
| Organizational Controls | Annex A 5.15 | Annex A 9.1.1 Annex A 9.1.2 |
Access Control |
| Organizational Controls | Annex A 5.16 | Annex A 9.2.1 | Identity Management |
| Organizational Controls | Annex A 5.17 | Annex A 9.2.4 Annex A 9.3.1 Annex A 9.4.3 |
Authentication Information |
| Organizational Controls | Annex A 5.18 | Annex A 9.2.2 Annex A 9.2.5 Annex A 9.2.6 |
Access Rights |
| Organizational Controls | Annex A 5.19 | Annex A 15.1.1 | Information Security in Supplier Relationships |
| Organizational Controls | Annex A 5.20 | Annex A 15.1.2 | Addressing Information Security Within Supplier Agreements |
| Organizational Controls | Annex A 5.21 | Annex A 15.1.3 | Managing Information Security in the ICT Supply Chain |
| Organizational Controls | Annex A 5.22 | Annex A 15.2.1 Annex A 15.2.2 |
Monitoring, Review and Change Management of Supplier Services |
| Organizational Controls | Annex A 5.23 | NEW | Information Security for Use of Cloud Services |
| Organizational Controls | Annex A 5.24 | Annex A 16.1.1 | Information Security Incident Management Planning and Preparation |
| Organizational Controls | Annex A 5.25 | Annex A 16.1.4 | Assessment and Decision on Information Security Events |
| Organizational Controls | Annex A 5.26 | Annex A 16.1.5 | Response to Information Security Incidents |
| Organizational Controls | Annex A 5.27 | Annex A 16.1.6 | Learning From Information Security Incidents |
| Organizational Controls | Annex A 5.28 | Annex A 16.1.7 | Collection of Evidence |
| Organizational Controls | Annex A 5.29 | Annex A 17.1.1 Annex A 17.1.2 Annex A 17.1.3 |
Information Security During Disruption |
| Organizational Controls | Annex A 5.30 | NEW | ICT Readiness for Business Continuity |
| Organizational Controls | Annex A 5.31 | Annex A 18.1.1 Annex A 18.1.5 |
Legal, Statutory, Regulatory and Contractual Requirements |
| Organizational Controls | Annex A 5.32 | Annex A 18.1.2 | Intellectual Property Rights |
| Organizational Controls | Annex A 5.33 | Annex A 18.1.3 | Protection of Records |
| Organizational Controls | Annex A 5.34 | Annex A 18.1.4 | Privacy and Protection of PII |
| Organizational Controls | Annex A 5.35 | Annex A 18.2.1 | Independent Review of Information Security |
| Organizational Controls | Annex A 5.36 | Annex A 18.2.2 Annex A 18.2.3 |
Compliance With Policies, Rules and Standards for Information Security |
| Organizational Controls | Annex A 5.37 | Annex A 12.1.1 | Documented Operating Procedures |
ISO 27001:2022 People Controls
| Annex A Control Type | ISO/IEC 27001:2022 Annex A Identifier | ISO/IEC 27001:2013 Annex A Identifier | Annex A Name |
|---|---|---|---|
| People Controls | Annex A 6.1 | Annex A 7.1.1 | Screening |
| People Controls | Annex A 6.2 | Annex A 7.1.2 | Terms and Conditions of Employment |
| People Controls | Annex A 6.3 | Annex A 7.2.2 | Information Security Awareness, Education and Training |
| People Controls | Annex A 6.4 | Annex A 7.2.3 | Disciplinary Process |
| People Controls | Annex A 6.5 | Annex A 7.3.1 | Responsibilities After Termination or Change of Employment |
| People Controls | Annex A 6.6 | Annex A 13.2.4 | Confidentiality or Non-Disclosure Agreements |
| People Controls | Annex A 6.7 | Annex A 6.2.2 | Remote Working |
| People Controls | Annex A 6.8 | Annex A 16.1.2 Annex A 16.1.3 |
Information Security Event Reporting |
ISO 27001:2022 Physical Controls
| Annex A Control Type | ISO/IEC 27001:2022 Annex A Identifier | ISO/IEC 27001:2013 Annex A Identifier | Annex A Name |
|---|---|---|---|
| Physical Controls | Annex A 7.1 | Annex A 11.1.1 | Physical Security Perimeters |
| Physical Controls | Annex A 7.2 | Annex A 11.1.2 Annex A 11.1.6 |
Physical Entry |
| Physical Controls | Annex A 7.3 | Annex A 11.1.3 | Securing Offices, Rooms and Facilities |
| Physical Controls | Annex A 7.4 | NEW | Physical Security Monitoring |
| Physical Controls | Annex A 7.5 | Annex A 11.1.4 | Protecting Against Physical and Environmental Threats |
| Physical Controls | Annex A 7.6 | Annex A 11.1.5 | Working In Secure Areas |
| Physical Controls | Annex A 7.7 | Annex A 11.2.9 | Clear Desk and Clear Screen |
| Physical Controls | Annex A 7.8 | Annex A 11.2.1 | Equipment Siting and Protection |
| Physical Controls | Annex A 7.9 | Annex A 11.2.6 | Security of Assets Off-Premises |
| Physical Controls | Annex A 7.10 | Annex A 8.3.1 Annex A 8.3.2 Annex A 8.3.3 Annex A 11.2.5 |
Storage Media |
| Physical Controls | Annex A 7.11 | Annex A 11.2.2 | Supporting Utilities |
| Physical Controls | Annex A 7.12 | Annex A 11.2.3 | Cabling Security |
| Physical Controls | Annex A 7.13 | Annex A 11.2.4 | Equipment Maintenance |
| Physical Controls | Annex A 7.14 | Annex A 11.2.7 | Secure Disposal or Re-Use of Equipment |
ISO 27001:2022 Technological Controls
| Annex A Control Type | ISO/IEC 27001:2022 Annex A Identifier | ISO/IEC 27001:2013 Annex A Identifier | Annex A Name |
|---|---|---|---|
| Technological Controls | Annex A 8.1 | Annex A 6.2.1 Annex A 11.2.8 |
User Endpoint Devices |
| Technological Controls | Annex A 8.2 | Annex A 9.2.3 | Privileged Access Rights |
| Technological Controls | Annex A 8.3 | Annex A 9.4.1 | Information Access Restriction |
| Technological Controls | Annex A 8.4 | Annex A 9.4.5 | Access to Source Code |
| Technological Controls | Annex A 8.5 | Annex A 9.4.2 | Secure Authentication |
| Technological Controls | Annex A 8.6 | Annex A 12.1.3 | Capacity Management |
| Technological Controls | Annex A 8.7 | Annex A 12.2.1 | Protection Against Malware |
| Technological Controls | Annex A 8.8 | Annex A 12.6.1 Annex A 18.2.3 |
Management of Technical Vulnerabilities |
| Technological Controls | Annex A 8.9 | NEW | Configuration Management |
| Technological Controls | Annex A 8.10 | NEW | Information Deletion |
| Technological Controls | Annex A 8.11 | NEW | Data Masking |
| Technological Controls | Annex A 8.12 | NEW | Data Leakage Prevention |
| Technological Controls | Annex A 8.13 | Annex A 12.3.1 | Information Backup |
| Technological Controls | Annex A 8.14 | Annex A 17.2.1 | Redundancy of Information Processing Facilities |
| Technological Controls | Annex A 8.15 | Annex A 12.4.1 Annex A 12.4.2 Annex A 12.4.3 |
Logging |
| Technological Controls | Annex A 8.16 | NEW | Monitoring Activities |
| Technological Controls | Annex A 8.17 | Annex A 12.4.4 | Clock Synchronization |
| Technological Controls | Annex A 8.18 | Annex A 9.4.4 | Use of Privileged Utility Programs |
| Technological Controls | Annex A 8.19 | Annex A 12.5.1 Annex A 12.6.2 |
Installation of Software on Operational Systems |
| Technological Controls | Annex A 8.20 | Annex A 13.1.1 | Networks Security |
| Technological Controls | Annex A 8.21 | Annex A 13.1.2 | Security of Network Services |
| Technological Controls | Annex A 8.22 | Annex A 13.1.3 | Segregation of Networks |
| Technological Controls | Annex A 8.23 | NEW | Web filtering |
| Technological Controls | Annex A 8.24 | Annex A 10.1.1 Annex A 10.1.2 |
Use of Cryptography |
| Technological Controls | Annex A 8.25 | Annex A 14.2.1 | Secure Development Life Cycle |
| Technological Controls | Annex A 8.26 | Annex A 14.1.2 Annex A 14.1.3 |
Application Security Requirements |
| Technological Controls | Annex A 8.27 | Annex A 14.2.5 | Secure System Architecture and Engineering Principles |
| Technological Controls | Annex A 8.28 | NEW | Secure Coding |
| Technological Controls | Annex A 8.29 | Annex A 14.2.8 Annex A 14.2.9 |
Security Testing in Development and Acceptance |
| Technological Controls | Annex A 8.30 | Annex A 14.2.7 | Outsourced Development |
| Technological Controls | Annex A 8.31 | Annex A 12.1.4 Annex A 14.2.6 |
Separation of Development, Test and Production Environments |
| Technological Controls | Annex A 8.32 | Annex A 12.1.2 Annex A 14.2.2 Annex A 14.2.3 Annex A 14.2.4 |
Change Management |
| Technological Controls | Annex A 8.33 | Annex A 14.3.1 | Test Information |
| Technological Controls | Annex A 8.34 | Annex A 12.7.1 | Protection of Information Systems During Audit Testing |
* This information has been sourced from isms.online
The recently released ISO/IEC 27001: 2022 standard signifies a significant update aimed at addressing global cybersecurity challenges and enhancing digital trust. This renowned information security management standard is crucial for safeguarding information assets in our increasingly digital world. If you’re responsible for information security, it’s essential to implement these changes to maintain compliance and align your information security practices with the evolving digital landscape and associated threats.
The modifications in ISO/IEC 27001: 2022 include both editorial adjustments, such as replacing “international standard” with “document” for clarity and improved international translation, as well as changes to harmonize with the ISO approach:
- A restructuring of numbering.
- A requirement to define processes for implementing the Information Security Management System (ISMS) and their interactions.
- An explicit requirement for communicating organizational roles related to information security.
Introduction of a new clause, 6.3 – Planning of Changes. - New requirements regarding communication (clause 7.4).
- Establishing criteria for operational processes and implementing control.
The most substantial changes relate to updates in Annex A controls to better align with recent changes in ISO/IEC 27002. These updates acknowledge the expanding scope of risk management across different organizational functions, making it more accessible for a wider audience to map and implement the necessary security controls.
Key changes in Annex A controls for ISO/IEC 27001: 2022 include:
- Reducing the number of controls from 114 to 93.
- Deletion, merger, and revision of several controls.
- Addition of 11 new security controls addressing evolving information security and cybersecurity challenges.
Consequently, organizations need to update their management systems to optimize their existing ISMS and align better with their information security risks and context. The standard’s structure has been consolidated into four key areas: Organizational, People, Physical, and Technological, in contrast to the 14 areas in the previous version of the standard.
The responsibility for implementing ISO 27001 controls typically falls on multiple parties within an organization. Here are the key individuals and roles involved:
Top Management: Senior executives and leadership play a critical role in establishing the overall direction, support, and commitment to the implementation of ISO 27001 controls. They are responsible for creating the policies, setting objectives, and providing necessary resources for compliance.
Information Security Manager: The Information Security Manager is often the key person responsible for coordinating and overseeing the implementation of ISO 27001 controls. They ensure that the ISMS is designed and maintained effectively and that controls are appropriately selected and applied.
Information Security Team: This team is responsible for executing specific tasks related to implementing controls, including risk assessments, security awareness training, incident response, and ongoing monitoring of security measures.
IT and Operations Teams: Various IT and operations personnel are responsible for executing technical aspects of controls, such as configuring security settings and access controls, and ensuring the secure operation of information systems.
Employees: All employees have a role in implementing controls by adhering to information security policies, reporting incidents or vulnerabilities, and maintaining a security-conscious culture.
Internal and External Auditors: Internal and external auditors are responsible for assessing and verifying the implementation and effectiveness of ISO 27001 controls. Their role is to provide an independent evaluation of compliance.
Third-party Suppliers and Vendors: Organizations that engage third-party suppliers or vendors are also responsible for ensuring that these external entities meet the required security controls, as outlined in the supplier relationships domain.
Compliance and Legal Teams: Compliance and legal teams are responsible for ensuring that the organization adheres to relevant laws and regulations, which is crucial in the compliance domain.
Risk Management Team: This team is responsible for conducting risk assessments and ensuring that controls are designed to mitigate identified risks effectively.
Human Resources: HR plays a role in ensuring that employee hiring, onboarding, and offboarding processes align with information security controls, as outlined in the human resources security domain.
Asset Owners and Custodians: Individuals or departments responsible for specific information assets should enforce controls for the classification, access, and protection of those assets.
In essence, implementing ISO 27001 controls is a collaborative effort involving various stakeholders across the organization. Each party plays a crucial role in ensuring that the controls are effectively designed, implemented, monitored, and continually improved to maintain information security.
The implementation of ISO 27001 involves several key steps and considerations. Here are the key points to keep in mind:
Management Support: Management backing is essential for the success of ISO 27001 implementation. Adequate resources and commitment from management ensure that the Information Security Management System (ISMS) can be effectively developed and maintained.
Defining Scope: Define the scope of the ISMS project, considering whether the entire organization or specific parts should be covered. The scope should remain manageable to minimize project risks.
Risk Assessment: Conduct a thorough risk assessment to identify vulnerabilities and threats that could impact the organization’s information security. Use methods like SWOT and PEST analysis to understand the risks comprehensively.
Risk Treatment: Once risks are identified, develop strategies to mitigate them. This can include implementing security controls from Annex A of ISO 27001, transferring risk through insurance, avoiding certain activities, or accepting minimal risks that are more cost-effective to tolerate.
Statement of Applicability: Refer to Annex A of ISO 27001, which lists 133 controls. Determine which controls are applicable to your organization, explain the reasons for their applicability, and define control objectives.
Risk Treatment Plan: Create a Risk Treatment Plan, also known as the Action Plan, which outlines how applicable controls will be implemented. It specifies the control owner, frequency, and implementation details.
Control Implementation: Put the applicable controls into action, and establish methods for measuring their effectiveness. This may involve introducing new technologies and procedures.
Training and Awareness Programs: Conduct regular training and awareness programs for employees to ensure they understand and comply with new policies and procedures. Cybersecurity threats, especially social engineering attacks, require heightened awareness.
Monitoring the ISMS: Follow the Plan-Do-Check-Act (PDCA) cycle as per ISO 27001. Regularly review the ISMS through internal audits, document results, and take necessary actions to improve policies, procedures, and controls.
While ISO 27001 implementation may seem complex and costly, it offers numerous benefits, including:
- Systematic management of security risks, ensuring the safety of sensitive information.
- Providing confidence to stakeholders, customers, and third-party suppliers that international best practices for security are followed.
- Mitigating risks, avoiding financial losses, and safeguarding against costly security breaches have become increasingly common.
An Information Security Management System (ISMS) serves as the protective vault for an organization’s valuable information assets, safeguarding them through a combination of people, systems, technology, processes, and security policies.
However, the ISMS is not just the hardware and software used to ensure data security; it’s also a set of guiding principles that dictate how information is used, stored, risk-assessed, and continuously improved.
Building an ISMS offers several advantages:
- Stakeholder Identification: It helps identify key stakeholders and their specific information security needs.
- Clear Expectations: An ISMS sets clear expectations and responsibilities for information security across the entire organization.
- Threat Identification: It aids in identifying threats to information assets.
- Control Implementation: An ISMS facilitates the definition and implementation of controls to mitigate vulnerabilities.
- Performance Monitoring: It allows for the monitoring and measurement of the performance of information security controls.
- Continuous Improvement: An ISMS supports continuous improvement in information security practices.
With VComply, streamlining and implementing ISO 27001 has become easy. Our platform offers a comprehensive solution that integrates built-in controls, a structured framework, streamlined workflow, continuous monitoring, actionable insights, and efficient audit capabilities to ensure your organization’s information security management aligns with ISO 27001 standards. Our inbuilt controls provide a robust foundation for your compliance efforts, helping you address information security risks effectively. Our structured framework guides you through the ISO 27001 requirements, ensuring you don’t miss critical elements.
The workflow capabilities streamline processes, making it easy to assign tasks, track progress, and collaborate effectively. Continuous monitoring keeps a vigilant eye on your compliance status, while insightful analytics provide a deeper understanding of your information security posture. Our audit features facilitate seamless assessments and reporting, ensuring your ISO 27001 compliance remains strong and auditable. With VComply, ISO 27001 implementation becomes a well-organized, efficient, and insightful process for your organization.
Implementing ISO 27001 is essential for organizations of all sizes to minimize security risks and ensure the protection of sensitive information, offering peace of mind to stakeholders and avoiding potential financial and reputational losses resulting from security breaches.