How to Manage Operational Risk? 2025 Complete Guide
In the modern day business enviornment, the intricate interplay of various elements such as processes, technology, and human resources brings forth a dynamic and challenging environment. At the heart of this complexity lies the concept of operational risk — a critical aspect that demands attention and strategic management.

Key takeaways (TL;DR)
-
Understand operational risk and its impact on processes, people, systems, and business continuity.
-
Learn the five stages of operational risk management to identify, assess, and mitigate risks.
-
See how technology and automation enhance monitoring, reporting, and proactive risk prevention efforts.
-
Discover best practices like scenario planning, risk indicators, and board-level ORM involvement.
-
Explore how VComply’s centralized risk register streamlines compliance and strengthens organizational resilience.
What Is Operational Risk?
Operational risk refers to the potential risk of losses arising from disruptions to a company’s internal operations, ineffective business processes, people, systems, or any external events that disrupt the flow of operations. It is a component of enterprise risk management. Operational risk can occur for various reasons, including internal control failures, process errors, human errors, business practice disruptions, system breakdowns, external events like natural disasters or pandemics, and fraudulent activities perpetrated by employees.
Operational risk has a ripple effect, where small oversights and control failures can quickly snowball into more significant risks. As a result, this can lead to organizational failures that can harm a company’s financial standing and reputation. While operational risk management falls under the umbrella of enterprise risk management, it should be noted that it doesn’t include strategic, financial, or reputational risks.
The Evolution of Operational Risk
Although businesses have been concerned with operational risk for centuries, it wasn’t officially recognized as a separate risk category until the 20th century. The discipline of operational risk management emerged in the late 1990s and early 2000s, prompted by numerous high-profile operational risk failures that resulted in significant financial losses and reputational harm for companies.
The collapse of Barings Bank in 1995 is a particularly notable event that drew attention to operational risk. An employee’s unauthorized trading activities caused the bank’s losses of over $1 billion. This incident demonstrated the need for improved controls and management systems to mitigate operational risks.
As a response to these events, financial regulators such as the Basel Committee on Banking Supervision began to stress the importance of operational risk management in the financial services industry. In 2001, the committee introduced the Basel II Accord, which established a standardized approach to measuring and managing operational risk.
The introduction of the Internal Control-Integrated Framework by COSO in 1992 and the Sarbanes-Oxley Compliance Act of 2002, which were prompted by financial frauds at Enron and WorldCom, emphasized the importance of a robust operational risk management system. In the U.S., there has been a growing demand for senior executives to take a more active role in risk oversight, with pressure primarily coming from the audit committee. Recently, COSO also launched an Enterprise Risk Management Framework, but risk managers have shifted their focus toward operational risk management processes after implementing the framework for several years.
Different Types and Examples of Operational Risks
Operational risks encompass a wide range of potential challenges that organizations may face due to internal processes, external factors, or human actions. Understanding and managing these risks is essential for maintaining operational efficiency and safeguarding the organization’s reputation. Here are some common types of operational risks:
Internal Fraud: Risks associated with fraudulent activities carried out by employees, such as embezzlement, theft, or unauthorized transactions. Effective controls and monitoring mechanisms can help mitigate this risk.
External Fraud: Risks arising from fraudulent activities perpetrated by external entities, including cyberattacks, phishing scams, or identity theft. Robust cybersecurity measures and employee awareness programs are crucial for mitigating these risks.
Legal and Compliance: Risks related to non-compliance with laws, regulations, or contractual obligations. Failure to meet legal requirements can result in fines, penalties, litigation, and reputational damage. A comprehensive compliance program is vital for managing this risk.
Employee Practices and Workplace Safety: Risks associated with employee behavior, such as misconduct, workplace accidents, or violation of health and safety regulations. Promoting a culture of safety, providing training, and enforcing policies can help mitigate these risks.
Client, Products, and Business Practices: Risks stemming from inadequate client service, product defects or failures, unethical business practices, or insufficient due diligence in business relationships. Robust quality control measures and ethical guidelines are necessary to mitigate these risks.
Data and IT Infrastructure: Risks related to data breaches, IT system failures, or disruptions in network infrastructure. Strong cybersecurity measures, data protection protocols, and regular system maintenance can help minimize these risks.
Business Disruption and System Failures: Risks arising from operational disruptions such as natural disasters, power outages, supply chain disruptions, or failures in critical systems and infrastructure. Business continuity planning and risk mitigation strategies are essential in managing these risks.
Execution, Delivery, and Process Management: Risks associated with errors or failures in operational processes, inadequate delivery of products or services, or inefficient process management. Robust process documentation, continuous improvement initiatives, and performance monitoring can help mitigate these risks.
Reputational Risk: Risks resulting from negative publicity, public perception, or damage to the organization’s reputation due to operational failures, ethical breaches, or adverse events. Upholding high ethical standards, effective communication, and proactive reputation management are key in mitigating this risk.
Vendor and Outsourcing Risks: Risks arising from dependencies on third-party vendors or outsourcing partners, including inadequate performance, service disruptions, data breaches, or non-compliance with contractual obligations. Thorough due diligence, contract management, and monitoring are crucial in managing these risks.
It’s important for organizations to identify, assess, and prioritize the operational risks that are most relevant to their specific industry, operations, and risk appetite. By implementing robust risk management strategies and controls, organizations can mitigate potential risks and enhance their overall operational resilience.
The Significance of Managing Operational Risk
Managing operational risk has become increasingly intricate due to various factors, such as technological advancements, global competition, and diminishing profit margins, which have pushed organizations to adopt more complex processes. The operational risk management maturity level may vary across industries, but there is increased recognition of managing and comprehending operational risks effectively. It is crucial for organizations as it enables them to comprehend their operational risk profiles, risk tolerance, and appetite.
Through developing and implementing their own risk culture and ethical guidelines, leaders can prioritize, understand, and effectively communicate the significance of risks, leading to informed decision-making that balances the requirements of customers, shareholders, product and service specifications, and organizational needs.
Operational risk management facilitates the creation of a sustainable and dependable organization that satisfies the expectations of customers, regulators, shareholders, and internal and external stakeholders, thereby providing a competitive edge. It helps businesses to reduce potential losses by identifying and mitigating emerging risks. A well-designed ORM program enables a company to achieve its strategic objectives and maintain business continuity, even in the face of unexpected disruptions.
It facilitates decision-making based on quantitative metrics and enables businesses to establish internal controls based on risk assessments. These controls are designed to detect and prevent illicit activities within the enterprise.
Implementing an effective ORM program also signals to stakeholders that the company is prepared to deal with disasters and losses, leading to improved brand recognition and product performance, stronger relationships with customers and stakeholders, increased investor confidence, better performance reporting, and more sustainable financial forecasting.
Operational risk management involves assessing and mitigating processes, products, services, and operations risks. There are five stages in the operational risk management (ORM) process, and they can help organizations prepare better for potential risks to their operations.
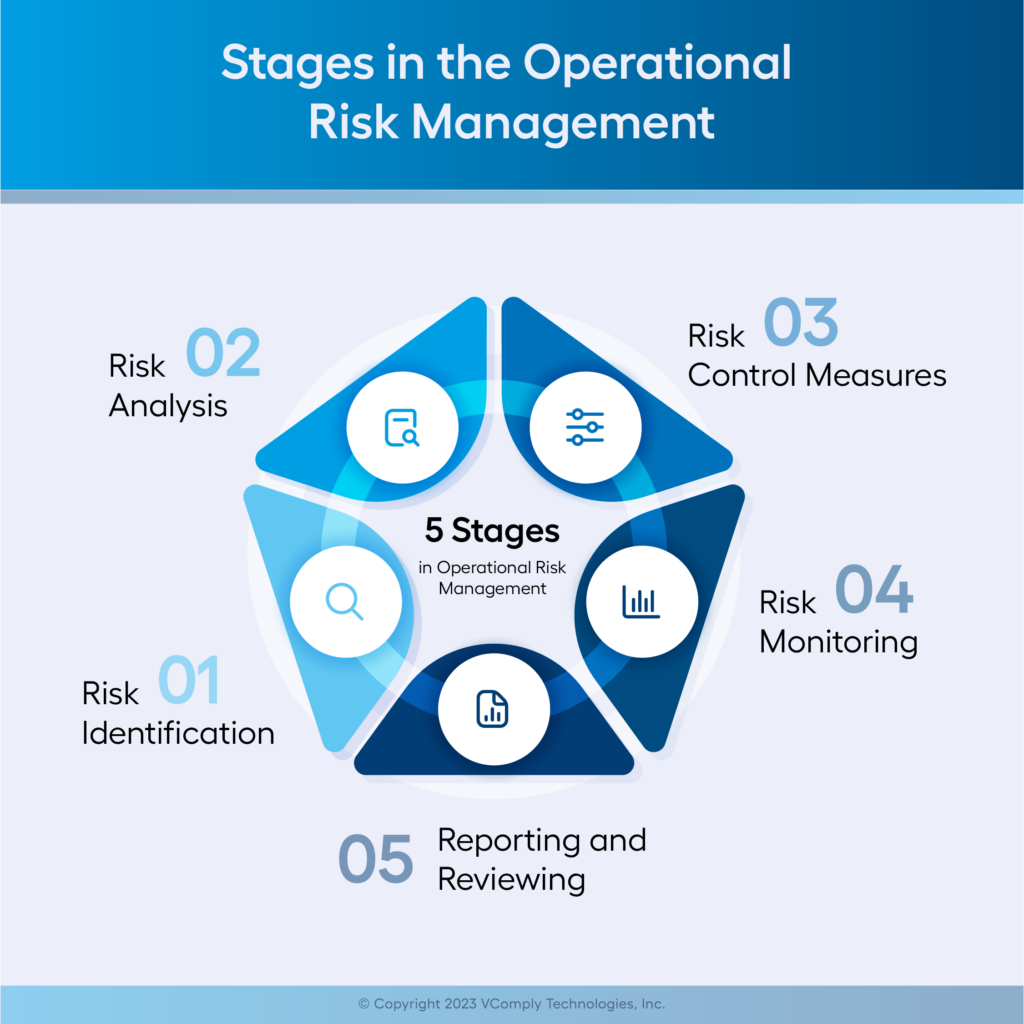
Risk Identification
The first stage in ORM is Risk Identification. It involves identifying any potential risks associated with current or future operations. This includes factors such as major losses or accidents, legal liabilities, inadequate insurance protection, or other threats that could negatively affect the business or organization. When potential risks are identified early on, it allows for better preparedness to manage them if something occurs. However, since the risk culture is not widespread at all levels of the company at this stage, there is a total dependence on the quality and integrity of employees and shareholders to maintain adequate control of events.
Risk Analysis
The second stage is Risk Analysis. Once risks have been identified, the next step is analyzing them to determine their likelihood and potential impact on operations. This helps prioritize the most important risks so they can be addressed first while also allowing organizations to make informed decisions regarding spending resources on achieving desired results in terms of risk reduction.
Risk Control Measures
The third stage of the operational risk management process is Risk Control Measures. Once recognized and prioritized, risks must be addressed by implementing effective control measures such as policies and procedures for employees to follow and training and education to understand better why these measures are necessary. Additionally, technological solutions such as automated processes and systems can help reduce operational risk significantly. At this stage, companies establish a specific area to manage risks. They define policies, responsibilities, and supporting tools. The resources available for managers to manage risk at this phase include mapping processes to identify risks and formalizing controls,
Risk Monitoring
The fourth stage in ORM is Risk Monitoring. It involves monitoring how well control measures are working to reduce operational risk over time by assessing how successfully they have prevented losses or accidents from occurring in specific areas of operations or departments within an organization. Regular reviews should be conducted to ensure the effectiveness of all control measures taken against identified risks before implementing further adjustments if needed.
Risk indicators, both qualitative and quantitative, and the goals or limits, are established to monitor them. Risk exposure measures are consolidated in a balanced scorecard to measure business performance in relation to risks. In this phase, management is decentralized across all areas of the organization, and the risk culture is strengthened. In addition, monitoring ceases to depend on the compliance area, and leaders are assigned to analyze and monitor processes and activities.
Reporting and Reviewing
The final stage in ORM is Reporting & Reviewing. It requires organizations to document all information related to each stage – from initial identification through the implementation of controls – consistently so that stakeholders may review it periodically for accuracy and completeness before any decisions regarding changes or updates are made accordingly. Doing this ensures stakeholders understand what has been done throughout each phase so far, helping them make smart decisions about their investments moving forward.
In conclusion, the five stages of the ORM process help organizations to identify potential risks, analyze them, implement risk control measures, and monitor the effectiveness of the control measures.
Implementing a risk management software solution can greatly benefit businesses by allowing for the daily identification and management of potential risks.
Best Practices in Operational Risk Management
-
Establish a Risk-Aware Culture
Encourage employees at all levels to identify and report risks. -
Leverage Technology
Use GRC (Governance, Risk, and Compliance) platforms to automate monitoring, reporting, and analytics. -
Integrate ORM with Enterprise Risk Management (ERM)
Align operational risk with strategic and financial risk frameworks for a holistic approach. -
Scenario Planning & Stress Testing
Run simulations of worst-case scenarios (e.g., cyberattack, system outage) to test resilience. -
Continuous Improvement
Risk management is not static—adapt processes to evolving risks, especially those tied to digital transformation. -
Board and Executive Involvement
Ensure ORM is championed at the top and supported with resources.
Tools and Techniques for ORM
-
Risk Control Self-Assessment (RCSA): Departments evaluate their own risks and controls.
-
Loss Event Database: Tracks past incidents for future prevention.
-
Key Risk Indicators (KRIs): Metrics that signal rising risk levels (e.g., system downtime > 2 hours).
-
Incident Management Systems: Logs and tracks operational failures.
-
Business Continuity Planning (BCP): Prepares for natural disasters, outages, or crises.
ORM and Compliance
Operational risk is intertwined with compliance. Key regulations include:
-
SOX (Sarbanes–Oxley Act): Requires internal controls for financial reporting.
-
Basel III: Requires banks to hold capital against operational risks.
-
HIPAA: Protects patient data in healthcare.
-
GDPR/CCPA: Data privacy and protection laws.
Organizations that integrate ORM with compliance management reduce audit costs and regulatory penalties.
The Future of Operational Risk Management
By 2025, ORM is increasingly shaped by technology and global trends:
-
AI & Automation: Predictive analytics for identifying risks earlier.
-
Cybersecurity: ORM frameworks must account for ransomware, phishing, and nation-state cyberattacks.
-
Third-Party Risk Management: As supply chains expand, vendor risks are under greater scrutiny.
-
ESG Risks: Environmental and social risks are increasingly viewed as operational risks.
-
Remote/Hybrid Work Risks: Requires stronger IT monitoring, access controls, and communication protocols.
Automating Operational Risk Using VComply
When it comes to managing operational risks, there is no such thing as being too cautious. Using a risk management tool can significantly improve an organization’s overall security, making it a worthwhile investment. One of the advantages of VComply is the ability to maintain a centralized risk register, providing a comprehensive overview of all identified risks. It helps you assess risks and alerts on risks that are above the threshold. It also facilitates integrating risk management and compliance activities into the organization’s operations.
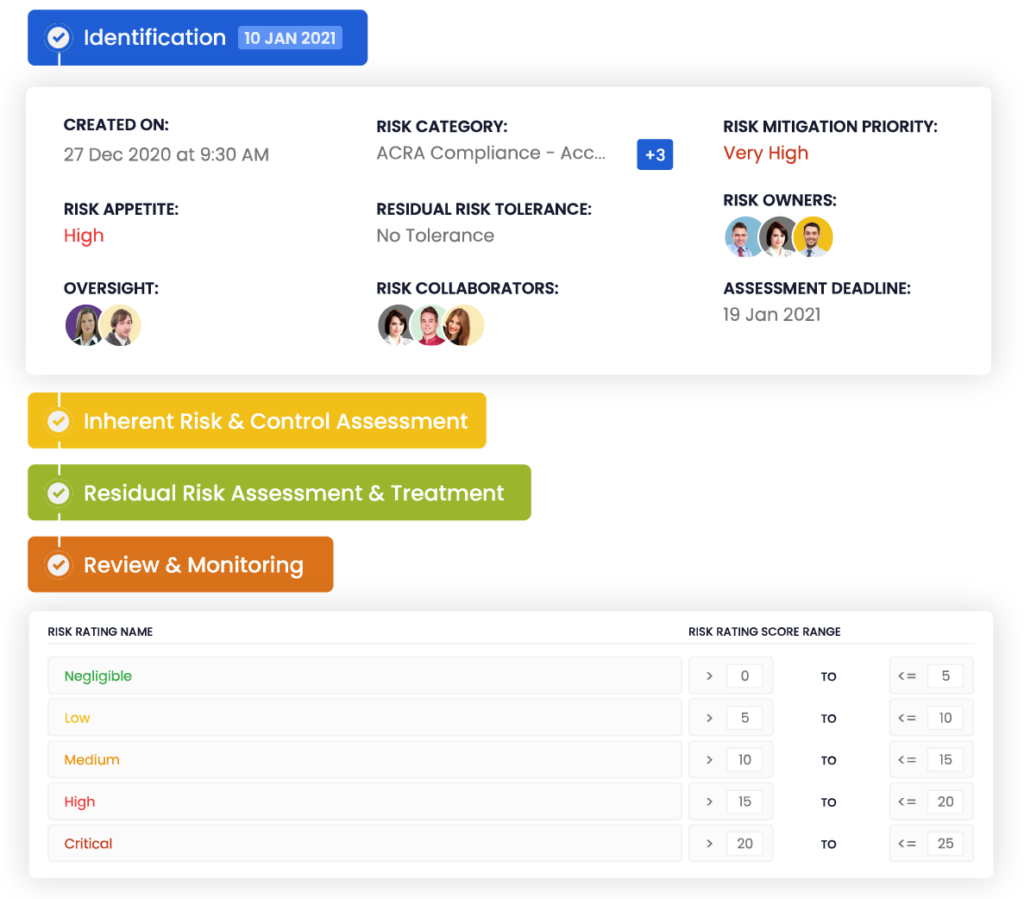
By using VComply, organizations can effectively manage risk and compliance posture, giving them easy access, control, and documentation of existing rules that mitigate vendor risks.
So, why wait? Consider implementing VComply to effectively identify and manage potential risks, ensuring the safety and success of your organization in the long run.
Request a demo today to learn more about how VComply can help your business.
Frequently Asked Questions (FAQ) on Operational Risk Management
1. What is operational risk?
Operational risk is the potential for loss resulting from failed processes, people, systems, or external events that affect daily business operations.
2. How is ORM different from Enterprise Risk Management (ERM)?
ERM covers all types of risks (strategic, financial, compliance, operational), while ORM specifically focuses on risks in day-to-day operations.
3. Which industries need ORM the most?
Banking, finance, healthcare, energy, and technology face the highest operational risk exposures, but ORM is applicable across all industries.
4. What are Key Risk Indicators (KRIs)?
KRIs are metrics used to signal potential risk exposure, such as rising error rates, increased downtime, or a surge in customer complaints.
5. Is ORM mandatory by law?
In highly regulated industries like banking (Basel III) and healthcare (HIPAA), ORM practices are effectively mandatory. In other sectors, ORM is a best practice rather than a legal requirement.
6. How does ORM help during a cyberattack?
ORM frameworks include preventive IT controls, monitoring systems, incident response plans, and recovery strategies that minimize impact from cyber threats.
7. What tools support ORM?
Risk registers, RCSA, loss event databases, GRC software, KRIs, and business continuity plans are widely used tools.
8. What role does leadership play in ORM?
Leaders must set the tone for a risk-aware culture, allocate resources, and ensure ORM is integrated into decision-making processes.
9. How does ORM save costs?
By preventing fraud, downtime, and compliance breaches, ORM reduces financial losses, fines, and reputational damage.
10. What is the future of ORM?
Future ORM will focus heavily on technology-driven risks (cybersecurity, AI), ESG obligations, vendor risk, and predictive analytics for early detection of threats.

